Microsoft Internet Information Services (IIS) 6.0 is vulnerable to a zero-day Buffer Overflow vulnerability (CVE-2017-7269) due to an improper validation of an ‘IF’ header in a PROPFIND request
A remote attacker could exploit this vulnerability in the IIS WebDAV Component with a crafted request using PROPFIND method. Successful exploitation could result in denial of service condition or arbitrary code execution in the context of the user running the application. According to the researchers who found this flaw, this vulnerability was exploited in the wild in July or August 2016. It was disclosed to the public on March 27. Other threat actors are now in the stages of creating malicious code based on the original proof-of-concept (PoC) code.
What is WebDAV?
Web Distributed Authoring and Versioning (WebDAV) is an extension of the HTTP protocol that allows clients to perform remote Web content authoring operations. WebDAV extends the set of standard HTTP methods and headers allowed for the HTTP request. Few example of WebDAV methods are COPY, LOCK, MKCOL, PROPFIND, UNLOCK etc.
This vulnerability is exploited using the PROPFIND method and IF header. The PROPFIND method retrieves properties defined on the resource identified by the Request-URI. All the WebDAV-Compliant resources must support the PROPFIND method.
The IF header handles the state token as well as the ETags. It makes the request conditional by supplying a series of state lists with conditions that match tokens and ETags to specific resource. If all states present in the IF header fail, the request fails with 412 (Precondition Failed) status.
A simple PROPFIND request is shown below:
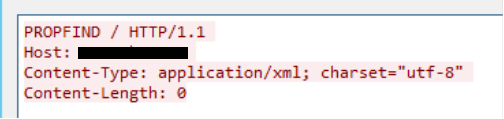
Figure 1. PROFIND request
An example of a typical syntax of IF header:
If: <http://www.example.com/resource1> (<locktoken:Test1>) (["ETag"]) <http://www.example.com/random>(["ETag"])
Vulnerability Description
This is a typical buffer overflow vulnerability . The affected system reported (by the researcher) is Windows 2003 and IIS version 6. The vulnerability could be exploited with an overly large ‘IF’ header in the ‘PROPFIND’ request with at least two http resource in the IF header. If successfully exploited, this vulnerability could lead to remote code execution. Sometimes, an unsuccessful attack could still lead to denial of service conditions.
Mitigation and Trend Micro Solutions
IIS 6.0 was included with Windows Server 2003; unfortunately, Microsoft isn't supporting and won't be patching the old OS version anymore. To mitigate the risk, disabling the WebDAV service on the vulnerable IIS 6.0 installation is recommended. Newer versions of Windows Server shipped with newer versions of IIS are not affected by this vulnerability.
Trend Micro Deep Security customers are recommended to apply the DPI rule below:
- 1008266 - Microsoft IIS WebDAV ScStoragePathFromUrl Buffer Overflow Vulnerability (CVE-2017-7269)
Deep Discovery Inspector protects customers from this threat via this DDI Rule:
- Rule 2357 - CVE-2017-7269-HTTP_WEBDAV_BUFFER_OVERFLOW_
TippingPoint customers are protected from attacks exploiting this vulnerability with this MainlineDV filter:
- 27643: HTTP: Microsoft IIS WebDAV ScStoragePathFromUrl Buffer Overflow Vulnerability
Users with Trend Micro Home Network Security are protected via the following signature:
- 1133548 WEB Microsoft IIS WebDAV ScStoragePathFromUrl Buffer Overflow (CVE-2017-7269)
Additional information provided by Suraj Sahu and Ziv Chang.

