Ransomware
Examining Ransomware Payments From a Data-Science Lens
In this entry, we discuss case studies that demonstrated how data-science techniques were applied in our investigation of ransomware groups' ransom transactions, as detailed in our joint research with Waratah Analytics, “What Decision-Makers Need to Know About Ransomware Risk.”
In partnership with: Erin Burns, Eireann Leverett of Waratah Analytics
Ransomware has come a long way since the Internet’s pre-cryptocurrency days. The advent of cryptocurrency was an important turning point in the evolution of this cyberthreat, as malicious actors are now no longer confined to available local or regional payment options when collecting ransom payments.
The operation costs and monetization models of a ransomware group can be telling of its persistence methods, the tactics, techniques, and procedures (TTPs) in its arsenal, and the qualifications of its members — all valuable insights for defenders if they are to mount a defense strategy that can hold out against increasingly sophisticated ransomware attacks. Previously, we explored how analyzing CVE data through data-science approaches can guide cybersecurity teams’ patching priorities — one of many data sources that organizations can turn to as a means of understanding the inner workings of the ransomware ecosystem. In this entry, we discuss case studies that demonstrated how data-science techniques were applied in our investigation of ransomware groups' ransom transactions, as detailed in our joint research with Waratah Analytics, “What Decision-Makers Need to Know About Ransomware Risk.”
Ransomware groups profile potential victims to calculate the ransom amount
Several factors contribute to the ransom amount that attackers initially demand from their victims and later, over the course of negotiations with them, the minimum amount for which malicious actors are willing to settle. The victim's revenue is one of the attacker's top considerations. Based on Conti’s leaked internal chat logs, we observed that the historic ransomware group, which had its own dedicated open-source intelligence (OSINT) team that collected information on their potential victims, profiled companies and kept tabs on their financial state using business information that was publicly available online.
The contents of the data stolen in a ransomware attack — including sensitive financial information like any recent monetary transactions, bank statements, and tax reports — might also factor into the negotiation process: If the victim claims an inability to pay when the ransomware actors are aware of contract payments or available funds found on their systems, the attackers might retaliate by hiking up the ransom amount or publishing the victim’s data.
Their business model determines a ransomware group's operational costs
Ransomware groups need to cover the costs of their operations if they are to turn a profit and prove their business model effective. Some groups demand a fixed amount from all their victims, while others set the ransom based on a detailed profile of the victim. Knowing how the attackers operate and the size of the ransom can help security teams distinguish targeted from non-targeted ransomware campaigns. Case in point, being able to tell the difference is important, as circumventing these attacks will require specific defense strategies.
Operational costs vary across ransomware groups and depend largely on the business model of the attackers. If the ransom amount is negotiable for ransomware actors, the costs that they incur in an attack designed for a particular victim might be used as a lower-bound estimate for the ransom.
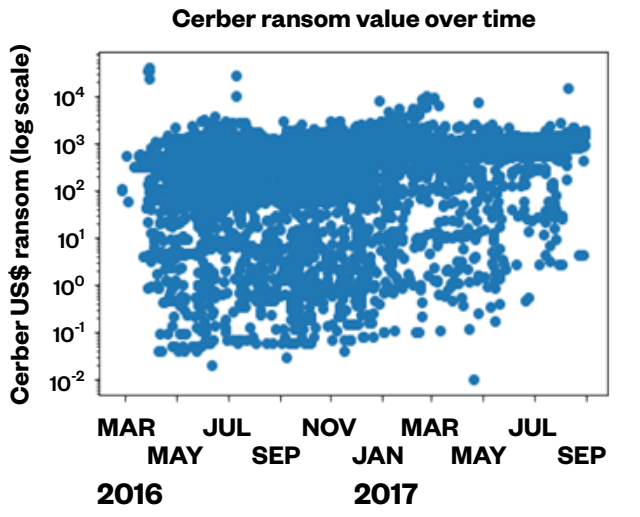
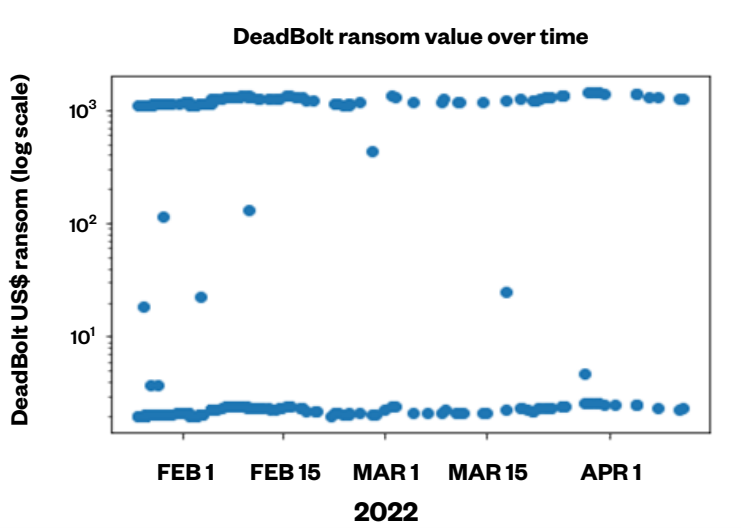
For ransomware groups whose business model involves adjusting the ransom size to the victim, we observed that ransom payments vary greatly in size, as was the case for the ransomware-as-a-service (RaaS) Cerber (Figure 1). On the other hand, the likes of the DeadBolt ransomware, which are focused on volume-based attacks, will show little variation (Figure 2). Indeed, groups like Cerber will calculate the initial ransom size and the threshold of the negotiated amount based on the individual target because the costs that go into organizing and carrying out an attack on a victim might need additional personnel and infrastructure.
Analyzing various data sources, including ransomware groups’ financial transactions, can provide cybersecurity professionals with insights into how these malicious actors operate under different business models. Our findings suggest that ransomware groups whose monetization strategy involves staging targeted attacks have skills, approaches, and attack capabilities similar to those observed in advanced persistent threat (APT) groups. For cybersecurity teams, thwarting this kind of ransomware group will take resources comparable to what they would need to defend their organizations against state-sponsored actors or a penetration test with an unlimited scope.
Most of the victims who do pay the ransom, pay fast
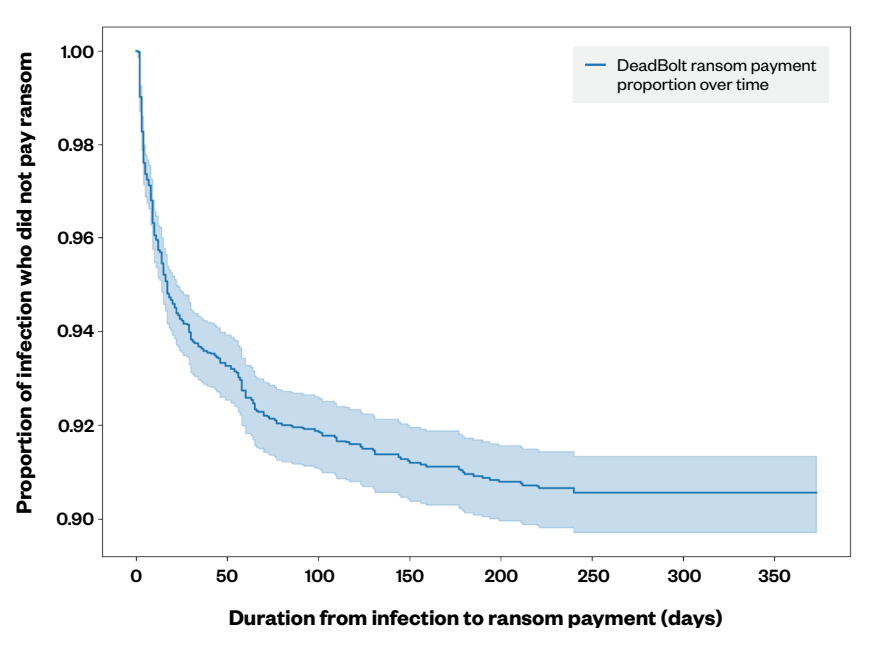
One of the case studies in this research examines the DeadBolt ransomware, which showed that over half of DeadBolt’s paying victims conceded to their demands within 20 days, while 75% did so within 40 days (Figure 3). Restoration time is a major consideration for corporate-level ransomware victims, and it’s important to note that if a victim’s critical systems are affected by an attack — especially if income depends on these systems — it’s likely that the victim will pay the ransom quickly.
By looking at the speed with which ransoms are paid in ransomware cases, our researchers found that data encryption in cyberattacks takes place not long before these financial transactions are detected in the blockchain. This kind of data can therefore prove useful to defenders when correlating ransom payments to ransomware binary samples or data leaks.
Cryptocurrency has changed the way malicious actors monetize their attacks — one of ransomware’s many milestones as it continues to grow more advanced. Organizations will need a comprehensive defense strategy if they are to stay ahead of the trends and developments in the ransomware landscape. To stay vigilant, it is also recommended that they implement the following best security practices:
- Enable multifactor authentication (MFA) to prevent attackers from performing lateral movement inside a network.
- Follow the 3-2-1 rule when backing up important files by creating three backup copies using two different file formats, with one of these copies stored in a separate location.
- Patch and update systems regularly, as this helps deter malicious actors from exploiting any software vulnerabilities in operating systems and applications
Organizations can also benefit from the use of multilayered detection and response solutions such as Trend Micro Vision One™, which provides powerful XDR capabilities that collect and automatically correlate data across multiple security layers — email, endpoints, servers, cloud workloads, and networks — to prevent attacks via automated protection while ensuring that no significant incidents go unnoticed. Trend Micro Apex One™ also provides next-level automated threat detection and response to protect endpoints against advanced issues, like human-operated ransomware.
For the full report on how data-science approaches can help cybersecurity professionals and industry leaders assess the risk of ransomware attacks on their business, read our research paper, “What Decision-Makers Need to Know About Ransomware Risk.”

