Exploit Kits: Past, Present and Future
 View research paper: The Evolution of Exploit Kits
View research paper: The Evolution of Exploit Kits
Exploit kits are a fast-growing online threat that cybercriminals seem to have favored in the last few years to execute Web-based attacks to distribute malware. Exploit kits are old tools released by Russian programmers dating back to 2006. As seen in the diagram below, exploit kits have continuously grown in numbers from 2006 to 2013. The market seemingly changed and took a significant dip however in 2014. The rise of exploit kits in underground markets push exploit kit developers to improve the stealth and efficiency of their products and services. Currently, there are 70 different exploit kits found in the wild, taking advantage of more than a hundred vulnerabilities.
What is an Exploit Kit?
Exploit kits are programs or more often scripts that exploit vulnerabilities in programs or applications. The most prevalent exploits are browser exploits that enable the download of malicious files. Exploits introduce code to victims’ computers that then downloads and executes a malicious file. Several kits have since been developed and sold or rented out like commercial products in underground markets. The easiest hack toolkit made available in the crimeware market on record was seen sometime in 2006.
A typical exploit kit usually provides a management console, several vulnerabilities targeted to different applications, and several add-on functions that make it easier for a cybercriminal to launch an attack.

The following research paper discusses the following:
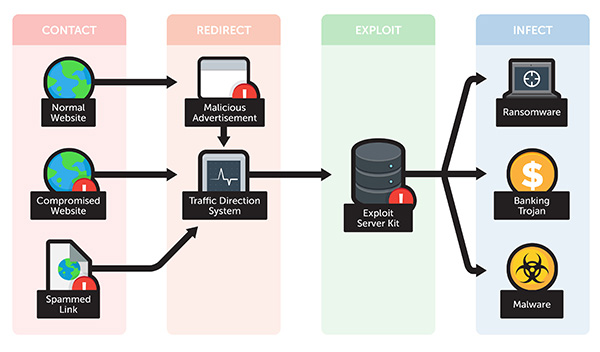
- Exploit Kit Attack Scenario – there are four stages that illustrate how a typical attack scenario happens. Detailed below, the stages include contact, redirect, exploit, and finally, infect.
- Overview of 2014 Exploit Kit Activity – this section discusses the exploit kit trends traced back from 2006 to 2014, including its threat distribution.
Exploit Kits are presently one of the most popular types of Web attack toolkits thriving in the cybercriminal underground market, and we predict that exploit kits will be more prevalent in 2015. Internet Explorer, Adobe Flash, and Adobe Reader are the most common software targeted by cybercriminals. Exploit kits pose serious security risks to all computer users ranging from private users to corporate networks. As such, it is critical to know and understand how exploit kits work, where they came from, what are the current trends, and how to defend against them.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- When AI Becomes a Zero-Day Machine: What Public Sector Organizations Need to Know
- A Data-Driven View of Cyber Risk Structure: How Attack Pressure and Exposure Shape Damage
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation