Trojan.HTML.PHISH.SMTPTCVBB
Other:SNH-gen [Phish] (AVAST)
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
Downloaded from the Internet, Dropped by other malware
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It does not have any propagation routine.
It does not have any backdoor routine.
TECHNICAL DETAILS
15,237 bytes
HTML, HTM
No
30 May 2025
Connects to URLs/IPs, Displays windows, Steals information
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Propagation
This Trojan does not have any propagation routine.
Backdoor Routine
This Trojan does not have any backdoor routine.
Rootkit Capabilities
This Trojan does not have rootkit capabilities.
Information Theft
This Trojan gathers the following account information:
- Specific Email
- Input Password
Stolen Information
This Trojan sends the gathered information via HTTP POST to the following URL:
- https://{BLOCKED}z.lk/script.php
- which sends the following information using the "data" parameter:
- username → victim's email address
- password → input password
- to → {BLOCKED}onway404@gmail.com (attacker's email address}
- subject → "{Empty string}" (on 1st submission) | " - Second Try" (on 2nd submission)
- which sends the following information using the "data" parameter:
- However, as of this writing, the said site is inaccessible.
Other Details
This Trojan does the following:
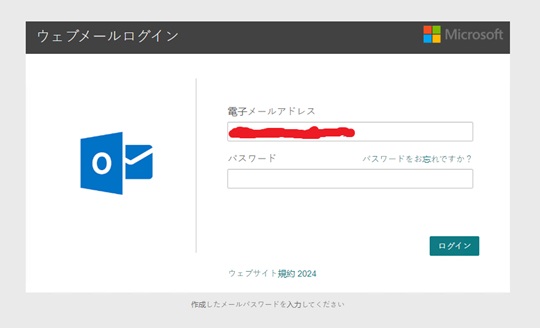
- It disguises itself as a login page to deceive the user into providing their password:
- It connects to the following URLs to display images and load resources inside the webpage:
- https://{BLOCKED}oogleapis.com/css?family=Roboto:100,400,500,700
- https://{BLOCKED}uery.com/jquery-3.5.1.min.js
- https://{BLOCKED}ckspace.com/favicon.ico
- https://{BLOCKED}n.msauth.net/shared/1.0/content/images/microsoft_logo_564db913a7fa0ca42727161c6d031bef.svg
- https://{BLOCKED}eraccess.com/full/3309609.jpg
hyperlink that contains the following legitimate URL:- https://{BLOCKED}elp.rackspace.com/l/identify-suspicious-email
- After the initial load, the current URL in the address bar is replaced with a spoofed URL that includes the parameters scriptID, cookies, and token, formatted as follows:
- {Current URL}?scriptID={ScriptId}&cookies={Cookies}&token={Token}
where:- ScriptId → random number between 0 and 999,999,999,999,998
- Cookies → Base64-encoded random number
- Token → random number
- {Current URL}?scriptID={ScriptId}&cookies={Cookies}&token={Token}
- It changes the page title into the following:
- Rackspace Webmail: Hosted Email for Business
- After the 1st login attempt, it displays the following fake error message:
- 入力したパスワードが正しくありません → translates to: "The password you entered is incorrect."
then reloads the page with the following URL:- {Spoofed URL}&sec_p=09304 → indicating the page is in 2nd login attempt
- 入力したパスワードが正しくありません → translates to: "The password you entered is incorrect."
- After the 2nd login attempt, it redirects to the following legitimate URL:
- http://google.jp
It does not exploit any vulnerability.
SOLUTION
9.800
19.428.05
26 Jun 2024
19.429.00
27 Jun 2024
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as Trojan.HTML.PHISH.SMTPTCVBB. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.


