TROJ_RECOLOAD.A
TrojanSpy:Win32/Ursnif.HM (Microsoft)
Windows


Threat Type: Spyware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
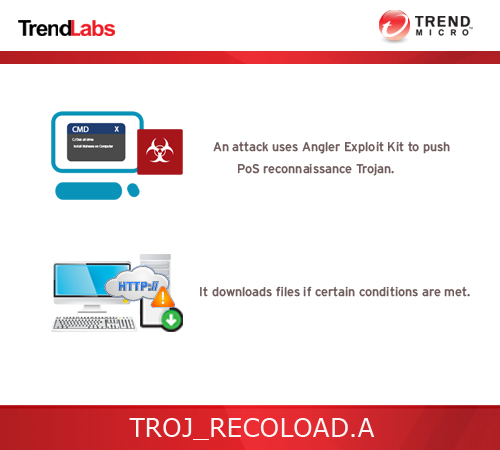
This Point-of-Sales (PoS) reconnaissance malware checks if the infected system is part of a PoS network or if it is a PoS machine. An attack uses Angler Exploit Kit to spread this PoS malware. In addition, it also employs Adobe Flash vulnerabilities covered in CVE-2015-0336 and CVE-2015-3104 respectively as entry point to the system.
To get a one-glance comprehensive view of the behavior of this Spyware, refer to the Threat Diagram shown below.
TECHNICAL DETAILS
Arrival Details
This spyware may be downloaded from the following remote sites:
- http://{BLOCKED}rrathenwil.eu/us
- http://audi.{BLOCKED}cedproject.xyz/pjDQO7VZSNg9dmQIFz70F0jcRLvDSyyWMKApHpIm1Y4kN_6I.py
Download Routine
This spyware connects to the following website(s) to download and execute a malicious file:
- http://{C&C server}?user={encoded user and computer name}&id=13&ver=115&os={OS information}&os2={OS Version}&host={boolean}&k={random value}&type={depending on case}
It saves the files it downloads using the following names:
- %User Temp%\{random}.exe
- %User Temp%\{random}.dll
(Note: %User Temp% is the user's temporary folder, where it usually is C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local\Temp on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
NOTES:
The {C&C server} can be any of the following:
- {BLOCKED}ipsmachoister.org
- {BLOCKED}arflonstexcb.org
- {BLOCKED}agshipeizehn.net
Looking at the end part of the URI, the parameter type depends on the following cases:
Case 1:
type=0555 and type=0922
If it finds the following URLs in the URL cache:
- choiceadvantage.com
- uhauldealer.com
- secure-booker.com
- teletracker.com
- wupos.westernunion.com
- pay1.plugnpay.com
- secure.paymentech.com/iterminal/
or
If it finds Verifone in the data of the following registry:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall
DisplayName
Case 2:
type=0666 and type=0922
If it finds the following strings in the output of the net view command:
- POS
- STORE
- SHOP
- SALE
Case 3:
type=0505
If the conditions above are not met.
The type in the URI determines which malware is downloaded to the infected system.
It employs the following anti-analysis techniques:
- It checks if there is section named .bss in its own image.
- It checks if the following modules are loaded in its process:
- dbghelp.dll
- api_log.dll
- dir_watch.dll
- pstorec.dll
- vmERROR.dll
- wpespy.dll
- PrxDrvPE.dll
- PrxDrvPE64.dll
- It checks any of the following user names match the one being used by the affected user:
- MALTEST
- TEQUILABOOMBOOM
- SANDBOX
- VIRUS
- MALWARE
- It checks if the following function is included in kernel32.dll:
- wine_get_unix_file_name
- It checks if any the following processes of analysis tools is running:
- wireshark.exe
- dumpcap.exe
- Tcpview.exe
- OllyDbg.exe
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Close all opened browser windows
Step 4
Restart in Safe Mode
Step 5
Search and delete these files
- %User Temp%\{random}.exe
- %User Temp%\{random}.dll
Step 6
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TROJ_RECOLOAD.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


