The cybersecurity landscape changed significantly in the first half of 2022. In our midyear roundup, we examine these changes and their effects on business operations as well as what you need to know about staying protected from online attacks.
In part one of the series, we talked about the growing attack surface and how actors have become more sophisticated. In this second instalment, we put ransomware and cloud environments into the spotlight. We also discuss other notable vulnerabilities that have wreak havoc in the first half of the year.
Big Game-Hunting Ransomware Families
With operations spread across many countries, it's not surprising that ransomware is becoming increasingly popular. This new strain has been targeting organizations with large financial capabilities—so far 50 companies have been hit in just over two months in early 2022. The operators behind this attack are looking for access credentials from major networks.
Black Basta originated in April 2022, when a user with the name Black Basta posted on some major underground forums that they were looking for corporate network access credentials for organizations in the United States, Canada, United Kingdom, Australia, and New Zealand. The user also mentioned that they were offering a share of the profits to any potential partners.
Currently, information on the scope and structure of the malicious actor’s operation is limited. Given Black Basta’s initial advertisement, however, it is likely that the group uses stolen credentials to gain access to its victim’s systems. It then proceeds to perform its encryption routine, First by deleting shadow copies via vssadmin.exe and then booting the device in safe mode. It then deletes the service called Fax, creates a new one using the malware’s path, and adds it to the registry for persistence.
Finally, it shuts down and reboots the target’s machine in Safe Mode with Networking using the compromised service to encrypt files. One of the notable characteristics of Black Basta is that its ransom note is hard-coded into the malware, suggesting that its operators could be using unique binaries for each of its victims.
Software Vulnerabilities Threaten to Disrupt the Operations of Business
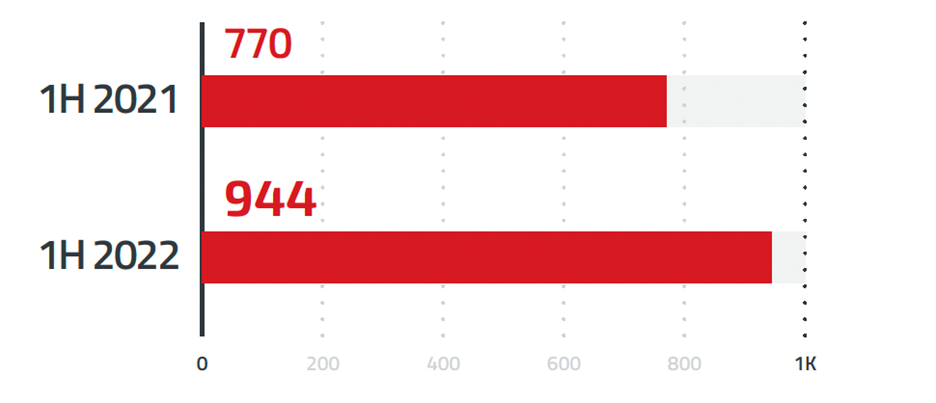
The number of vulnerabilities published by CVE increased in the first half of 2022, with 12,380 records compared to 9,420 during the same period last year. This trend was also seen through Trend Micro ZDI. There was an increase from 770 Advisories issued between January 1st and June 30th 2021. Now, there are 944 total security alerts available via this program since the midyear of 2022 alone.
Vulnerabilities with a high-severity rating made up the greatest portion (68%) of published vulnerabilities. Critical- and medium-severity bugs saw large increases, while only critical issues experienced a decrease from last year's data collection period. This suggest that organizations should employ an efficient risk-based approach that focuses on those affecting their environment before verifying whether they have public proof available for these types respectively within the wild using resources such as Cybersecurity and Infrastructure Security Agency’s (CISA) Known Exploited Vendor list.
2021 also saw the rise of CVE-2021-44228 (also known as Log4Shell), a vulnerability that affected the Java-based logging library, Apache Log4j. The disclosure of Log4Shell shook the cybersecurity landscape due to the ubiquity of the software it affected and its integration into different systems. This made it difficult for organizations to determine how they were affected. The first half of 2022 saw more vulnerabilities affecting critical enterprise software, with perhaps the most notable being the Spring4Shell vulnerability.
In April 2022, we saw Spring4Shell being used in an attack in the wild. One of these attempts involved exploiting a vulnerability to deploy cryptocurrency mining malware on targeted machines where an encrypted payload was executed using a string of checks. This fetches a script designed to download and execute a cryptocurrency miner on the infected machine.
Newly Discovered Vulnerabilities Threaten the DDS Standard
The Data Distribution Service (DDS) is a middleware technology that serves as the connectivity standard for enabling secure real-time information exchange and rapid integration of industrial Internet of Things (IIoT) devices. DDS allows industry professionals to develop modules within their applications, which can then be used by other companies without installing install extra hardware or software.
In January 2022, Trend Micro Research, TXOne Networks, ZDI, in collaboration with ADLINK Labs and Alias Robotics published an entry discussing DDS from a cybersecurity perspective. The article lists 13 new vulnerabilities for the six most common implementations of this system with implications that affect more than just those who use it directly but also Robot Operating System 2 (ROS 2). ROS 2 is, by default, used in robotics or automation projects using Dual-Density Storage technology as middleware. This means any successful exploit could lead to significant consequences on these types of systems.
Notable Vulnerabilities
Some of the noteworthy vulnerabilities we discovered and analyzed in the first half of 2022 affected platforms other than Windows. In April 2022, we released a blog entry about our discovery and analysis of CVE-2022-22639, a vulnerability in suhelperd, a helper daemon process for the macOS Software Update that contains the class SUHelper.
Linux and Unix users are being targeted in a new exploit that affects both operating systems and takes advantage of an old flaw. This vulnerability, known as “Dirty Pipe” can be used by hackers to elevate their privileges on the host system (tooser), has been around since 2008 when version 5.8 came out. Only recently did developers discover its potential for wreaking havoc among even trusted environments.
The WSO2 platform is a popular solution for integrating APIs and applications, but it appears that its effectiveness may be threatened by CVE 2022-2946472. The exploit of this flaw, which does not require user interaction or administrative privileges, can allow attackers to penetrate networks belonging to those affected systems.
There have been exploit attempts targeting CVE-2022-29464 published on GitHub back in April. Shortly after, the Metasploit module for affected environments has been updated to include a new exploit attempt that installs Cobalt Strike beacons and other malware as part of the attack routine.
Old Issues, Unconventional Attacks Plague Cloud Environments
The trend of organizations moving at least part of their infrastructure into the cloud is expected to continue in coming years, with Gartner forecasting that public-cloud spending alone will reach nearly $500 billion in 2022.
While widespread adoption of the cloud has made many businesses run more efficiently, it has also made cloud-based systems an attractive target for malicious actors looking to expand the regular scope of their operations.
Traditionally, the most efficient method of cryptocurrency mining involved using expensive machines with powerful GPUs. Other types of cryptocurrency mining, such as CPU-based mining, can also be profitable, but only at scale where sheer numbers can make up for the difference in performance. Since most users do not have high-end graphical powerhouses at their disposal, some groups have begun focusing their efforts on quantity over quality by relying instead on compromising cloud instances for cryptocurrency-mining operations.
In our research into cloud-based cryptocurrency mining, we investigated the primary threat actors that inhabit this space and determined the five most prominent groups and how they conduct their operations:
- Outlaw is a threat actor that prefers to stick to the tools and techniques it knows, with relatively little change in its operations over the years. Outlaw’s preferred targets include IoT devices and Linux cloud servers, which it compromises by exploiting known vulnerabilities or performing brute-force Secure Shell (SSH) attacks.
- TeamTNT is a group we’ve covered extensively over the past couple of years. The threat actor is known for being active in social media, going as far as replying to researchers who have analyzed their attacks. TeamTNT has evolved quickly over a short period, making it one of the most technically proficient threat actors focused on cryptocurrency mining.
- Kinsing, at least in terms of online presence, can be considered an antithesis to TeamTNT since the group does not maintain any noticeable presence on social media or even in underground forums. However, it shares some similarities with its rival in terms of its ability to quickly adapt and evolve its operational kit.
- 8220 is a group that has been a frequent exploiter of vulnerabilities, primarily those that affect the Oracle WebLogic Server. After a relatively quiet 2020, we observed that the group became much more active in 2021, with approximately 10 times the activity levels in the previous year. The threat actor has also been known to compete with Kinsing for the same resources, with the two often kicking each other out from compromised machines to install their own cryptocurrency miners.
- Kek Security is a relatively new group that has been garnering attention due to its sophistication and penchant for integrating new exploits into its attacks. Kek Security is also continuously developing its malware, with some of its more recent additions providing better obfuscation capabilities to evade. detection and prevent researcher analysis.
The last and final part of our series talks about how malicious actors take advantage, of misconfiguration which remains a headache for most organizations.

