TROJ_RANSOM.AQB
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Trojan
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This Trojan infects the Master Boot Record (MBR) of an affected system. It restarts the system afterwards and shows a ransom message, urging users to pay an amount in order to reverse the effect.
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.

This Trojan infects the MBR of the system it affects. Once executed, the malware copies the original MBR and overwrites it with its code.
It displays a certain message that tells the user that the system is locked and they must pay through an electronic payment service in order to have their systems unlocked.
Should the user pay the required amount of money, the attacker sends them a code to unlock the system. The OS resumes loading and the infected MBR removed.
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan drops the following copies of itself into the affected system and executes them:
- %User Temp%\x2z8.exe
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003.)
It drops the following non-malicious file:
- %User Temp%\fpath.txt
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003.)
NOTES:
This Trojan infects the MBR of the affected system. Once executed, this malware copies the original MBR and overwrites it with its code.
After writing its code, it automatically restarts the system to let the infection take effect. When the system restarts, the users see the following message:
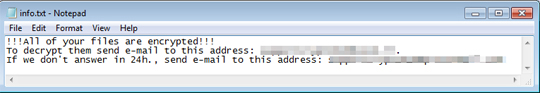
The message on the screen prompts the users that the system is blocked and ask to pay 920 hryvnia (UAH) via QIWI, an electronic payment service, to a purse number (12 digits) - 380682699268. It also writes that after the payment is sent, the user is given a code to unlock the system.
If the user pays for the code, the OS resumes loading and the infected MBR is removed. The infected MBR is detected by Trend Micro as BOOT_RANSOM.AQB.
SOLUTION
Step 1
Restore your system’s Master Boot Record (MBR)
To restore your system's Master Boot Record (MBR):
- Insert your Windows Installation CD into your CD-ROM drive or the USB flash drive then restart your computer.
- Press the restart button of your computer.
- When prompted, press any key to boot from the CD.
- When prompted on the Main Menu, type r to enter the Recovery Console.
(For Windows 2000 users: After pressing r, type c to choose the Recovery Console on the repair options screen.) - When prompted, type your administrator password to log in.
- Once logged in, type the drive that contains Windows in the command prompt that appears, and then press Enter.
- Type the following then press Enter:
fixmbr {affected drive}
(Note: The affected drive is the bootable drive that this malware/grayware has affected. If no device is specified, the MBR will be written in the primary boot drive.) - Type exit to restart the system.
Step 2
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 3
Remove malware files dropped/downloaded by TROJ_RANSOM.AQB
- BOOT_RANSOM.AQB
Step 4
Search and delete this file
There may be some component files that are hidden. Please make sure you check the Search Hidden Files and Folders checkbox in the More advanced options option to include all hidden files and folders in the search result. %User Temp%\fpath.txt
Step 5
Scan your computer with your Trend Micro product to delete files detected as TROJ_RANSOM.AQB. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 6
Identify files detected as TROJ_RANSOM.AQB, then restore the Master Boot Record and delete malware files using Recovery Console
Did this description help? Tell us how we did.


