Security for Entertainment IoT
 View Infographic: Security for Entertainment IoT
View Infographic: Security for Entertainment IoT
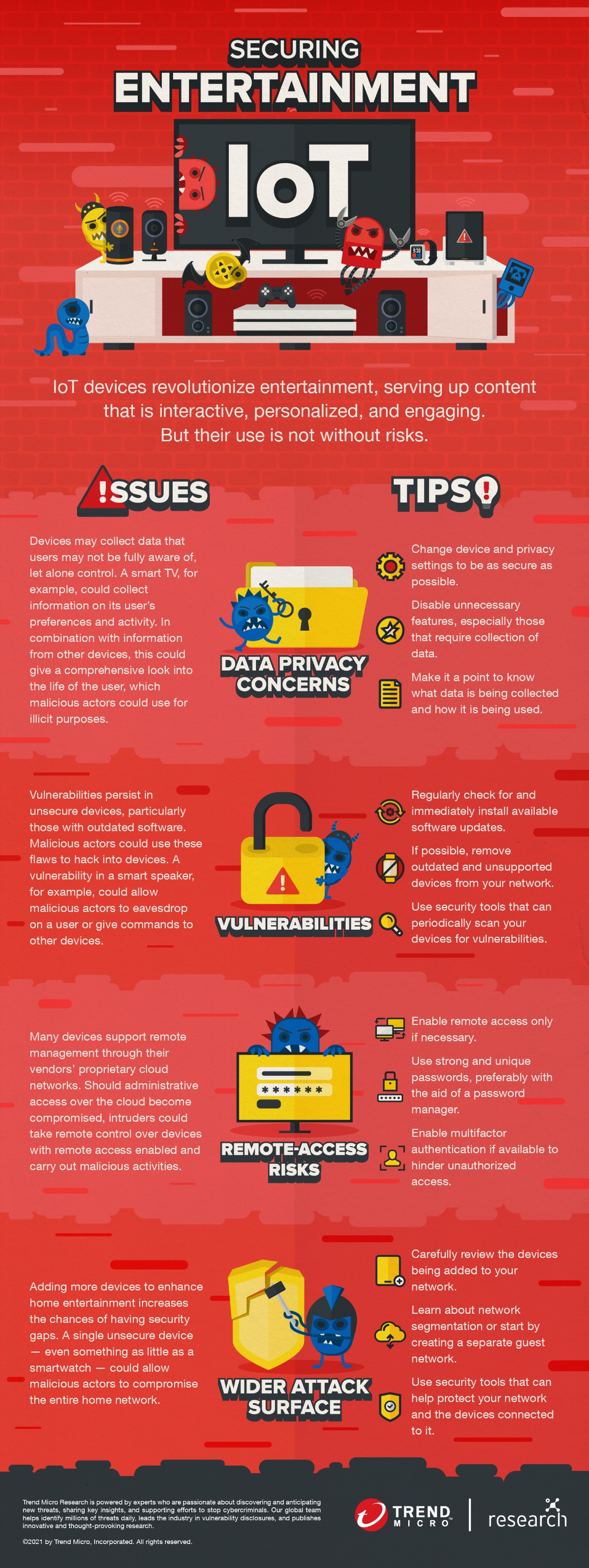
How many devices around you are connected to the internet? Perhaps you have a TV that streams your favorite shows and movies, a voice-activated speaker at your beck and call, and even a game console featuring virtual-reality technology. Such devices are manifestations of the capabilities of the internet of things (IoT). Indeed, the IoT has revolutionized — among many other industries — media and entertainment, as most tellingly seen and experienced at home.
Thanks to the power of the IoT, entertainment is now not only personalized but also more accessible than ever before. Sophisticated sensors help devices listen to, detect, and otherwise pick up commands and other factors, so that media content can be more engaging and interactive even within the confines of a living room. This is a more than welcome development especially in a time when most people are sheltered in place and media consumption indoors is the best and often only option.
As convenient as these entertainment IoT devices are, though, users should not be distracted from the risks these devices could bring to their homes. A hacked device, for example, could allow malicious actors to steal sensitive information, infect other devices on the network, or use sensors to monitor activities within the household. Users would therefore be well served to secure their IoT environments, so as to be able to fully enjoy the benefits of these devices.
With additional insights from Vit Sembera.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Sockpuppeting: How a Single Line Can Bypass LLM Safety Guardrails
- It’s By Design: The Use-After-Free of Azure Cloud
- Guarding LLMs With a Layered Prompt Injection Representation
- From Anarchy to Authority: Closing the Governance Gap in Agentic AI
- Unconventional Attack Surfaces: Identity Replication via Employee Digital Twins

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation