RANSOM_HDDCRYPTOR.F
Win32/Filecoder.DCryptor.A (NOD32), W32/Filecoder_DCryptor.A!tr (Fortinet)
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This ransomware does not only target resources in network shares such as drives, folders, and files but locks the drive as well. It does this by combining both legitimate and malicious tools.
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
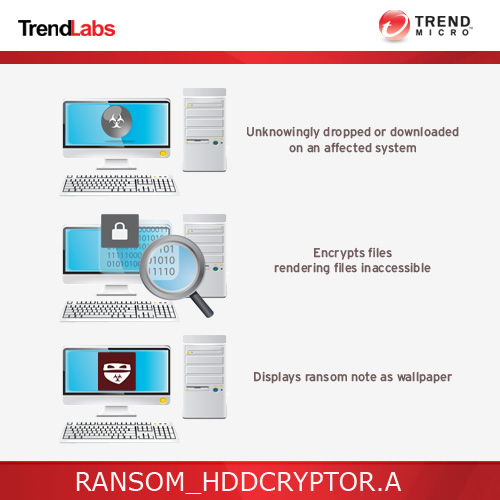
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan drops the following files:
- %System Root%\Users\ABCD\dcapi.dll
- %System Root%\Users\ABCD\dccon.exe
- %System Root%\Users\ABCD\dcrypt.exe-Disk Cryptor
- %System Root%\Users\ABCD\dcrypt.sys
- %System Root%\Users\ABCD\log_file.txt - Log of malware activities
- %System Root%\Users\ABCD\Mount.exe
- %System Root%\Users\ABCD\netpass.exe-Network Password Recovery Software
- %System Root%\Users\ABCD\netuse.txt - used to store information about network users
- %System Root%\Users\ABCD\netpass.txt - used to store user passwords
- %System%\drivers\dcrypt.sys
(Note: %System Root% is the Windows root folder, where it usually is C:\ on all Windows operating system versions.. %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.)
It adds the following processes:
- For Windows XP:
- %System%\cmd.exe schtasks /create /tn DefragmentService /TR \"cmd.exe /c net use >> C:\Users\ABCD\netuse.txt\" /sc DAILY
- %System%\cmd.exe schtasks /run /TN DefragmentService
- %System%\cmd.exe schtasks /delete /TN DefragmentService /F
- %System%\cmd.exe /c C:\Users\ABCD\netpass.exe /stab C:\Users\ABCD\netpass.txt
- For Non-XP Windows version:
- %System%\cmd.exe /c net user /add mythbusters 123456
- %System%\cmd.exe /c net localgroup administrators mythbusters /add
- %System%\cmd.exe /c cmd /c net use >> C:\Users\ABCD\netuse.txt
- %System%\cmd.exe /c C:\Users\ABCD\netpass.exe /stab C:\Users\ABCD\netpass.txt
- %System Root%\Users\ABCD\dcinst.exe -setup
(Note: %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.. %System Root% is the Windows root folder, where it usually is C:\ on all Windows operating system versions.)
Autostart Technique
This Trojan adds and runs the following services:
- DefragmentService
Other System Modifications
This Trojan adds the following registry keys:
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Services\dcrypt\Instances\
dcrypt
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet002\
Services\DefragmentService
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Services\dcrypt
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Services\dcrypt\Instances
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Services\dcrypt\config
It adds the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Services\dcrypt\Instances
DefaultInstance = "dcrypt"
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Services\dcrypt\Instances\
dcrypt
Altitude = "87150"
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Control\Class\{71A27CDD-812A-11D0-BEC7-08002BE2092F}
LowerFilters = "dcrypt"
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Control\Class\{4D36E965-E325-11CE-BFC1-08002BE10318}
UpperFilters = "dcrypt"
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Services\dcrypt\config
Flags = "1408"
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Services\dcrypt\config
Hotkeys = "0"
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Services\dcrypt\config
sysBuild = "846"
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet002\
Services\DefragmentService
DisplayName = "DefragmentService"
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet002\
Services\DefragmentService
ImagePath = "{malware path} {parameter}"
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet002\
Services\DefragmentService
Start = "2" SERVICE_AUTO_START
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet002\
Services\DefragmentService
Type = "16"
Other Details
This Trojan does the following:
- Reboots the system to successfully install the Disk Cryptor
- After reboot, it will execute the following:
- %System Root%\Users\ABCD\Mount.exe {parameter}
- %System Root%\Users\ABCD\dccon.exe -boot -setmbr hd0
- %System Root%\Users\ABCD\dccon.exe -encrypt pt{0-9}-p {parameter}
- It uses the tool %System Root%\Users\ABCD\dccon.exe to encrypt the disk drive and modify the Master Boot Record to display the ransom note.
- After encryption, it will execute the following command:
%System%\cmd.exe /C ping 1.1.1.1 -n 1 -w 3000 > Nul & sc delete DefragmentService & Del "{malware path}\{malware name}.exe" & taskkill /im Mount.exe & Del ""%System Root%\User\ABCD\Mount.exe"" & Del ""%System Root%\User\ABCD\netpass.txt"" & Del ""%System Root%\User\ABCD\netuse.txt"" & Del ""%System Root%\User\ABCD\netpass.exe"" & net user /del mythbusters & shutdown /f /r /t 0 x - It requires atleast any one parameter for it to execute successfully.
(Note: %System Root% is the Windows root folder, where it usually is C:\ on all Windows operating system versions.. %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.)
NOTES:
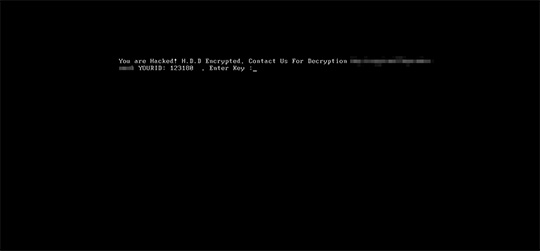
After another reboot, it displays the following ransom note at boot up:
SOLUTION
Step 1
Restore your system's Master Boot Record (MBR)
To restore your system's Master Boot Record (MBR):
• On Windows 2000, XP, and Server 2003:
- Insert your Windows Installation CD into your CD drive then restart your computer.
- When prompted, press any key to boot from the CD.
- On the Main Menu, type r to enter the Recovery Console.
(Note for Windows 2000: After pressing r, type c to choose the Recovery Console on the repair options screen.) - Type the number that corresponds to the drive and folder that contains Windows (usually C:\WINDOWS) and press Enter.
- Type your Administrator password and press Enter.
- In the input box, type the following then press Enter:
fixmbr {affected drive} - Type exit and press Enter to restart the system normally.
• On Windows Vista, 7, and Server 2008:
- Insert your Windows Installation DVD into the DVD drive, then press the restart button on your computer.
- When prompted, press any key to boot from the DVD.
- Depending on your Windows Installation DVD, you might be required to choose the installation language. On the Install Windows window, choose your language, locale, and keyboard layout or input method. Click Repair your computer.
- Select Use recovery tools that can help fix problems starting Windows. Select your installation of Windows. Click Next.
- If the Startup Repair window appears, click Cancel, Yes, then Finish.
- In the System Recovery Options menu, click Command Prompt.
- In the Command Prompt window, type the following then press Enter:
BootRec.exe /fixmbr - Type exit and press Enter to close the Command Prompt window.
- Click Restart to restart your computer normally.
• On Windows 8, 8.1, and Server 2012:
- Insert your Windows Installation DVD in the DVD drive, then restart your computer.
- When prompted, press any key to boot from the DVD.
- Depending on your Windows Installation DVD, you might be required to select the keyboard layout. Then on the Windows Setup window, choose your language, locale, and input method. Click Next, then click Repair your computer.
- Click Troubleshoot>Advanced Options>Command Prompt.
- In the Command Prompt window, type the following then press Enter:
BootRec.exe /fixmbr - Type exit and press Enter to close the Command Prompt window.
- Click Continue to restart the system normally.
Step 2
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Restart in Safe Mode
Step 5
Disable this malware service
- DefragmentService
Step 6
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services
- dcrypt
- dcrypt
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet002\Services
- DefragmentService
- DefragmentService
Step 7
Search and delete this file
- %System Root%\Users\ABCD\dcapi.dll
- %System Root%\Users\ABCD\dccon.exe
- %System Root%\Users\ABCD\dcrypt.exe
- %System Root%\Users\ABCD\dcrypt.sys
- %System Root%\Users\ABCD\log_file.txt
- %System Root%\Users\ABCD\Mount.exe
- %System Root%\Users\ABCD\netpass.exe
- %System Root%\Users\ABCD\netuse.txt
- %System Root%\Users\ABCD\netpass.txt
- %System%\drivers\dcrypt.sys
Step 8
Restart in normal mode and scan your computer with your Trend Micro product for files detected as RANSOM_HDDCRYPTOR.F. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


