- About Trend Micro
- Newsroom
Newsroom
Research, News, and Perspective
Author: Abdelrahman Esmail (Sr. Engineer), Sunil Bharti (Senior Threat Researcher)
Using gRPC and HTTP/2 for Cryptominer Deployment: An Unconventional Approach
In this blog entry, we discuss how malicious actors are exploiting Docker remote API servers via gRPC/h2c to deploy the cryptominer SRBMiner to facilitate their mining of XRP on Docker hosts.
Oct 22, 2024
Author: Sunil Bharti (Senior Threat Researcher), Ranga Duraisamy (Vulnerability Researcher)
Attackers Target Exposed Docker Remote API Servers With perfctl Malware
We observed an unknown threat actor abusing exposed Docker remote API servers to deploy the perfctl malware.
Oct 21, 2024
Gartner 2024 CNAPP Market Guide Insights for Leaders
As businesses increasingly pivot to cloud-native applications, the landscape of cybersecurity becomes ever more challenging.
Oct 18, 2024
DevOps Resource Center
CISO Resource Center
Media Contacts
Pick your region:
- USA
- AMEA
- Europe
- Latin America
- Japan
- Taiwan
Discover Trend Micro
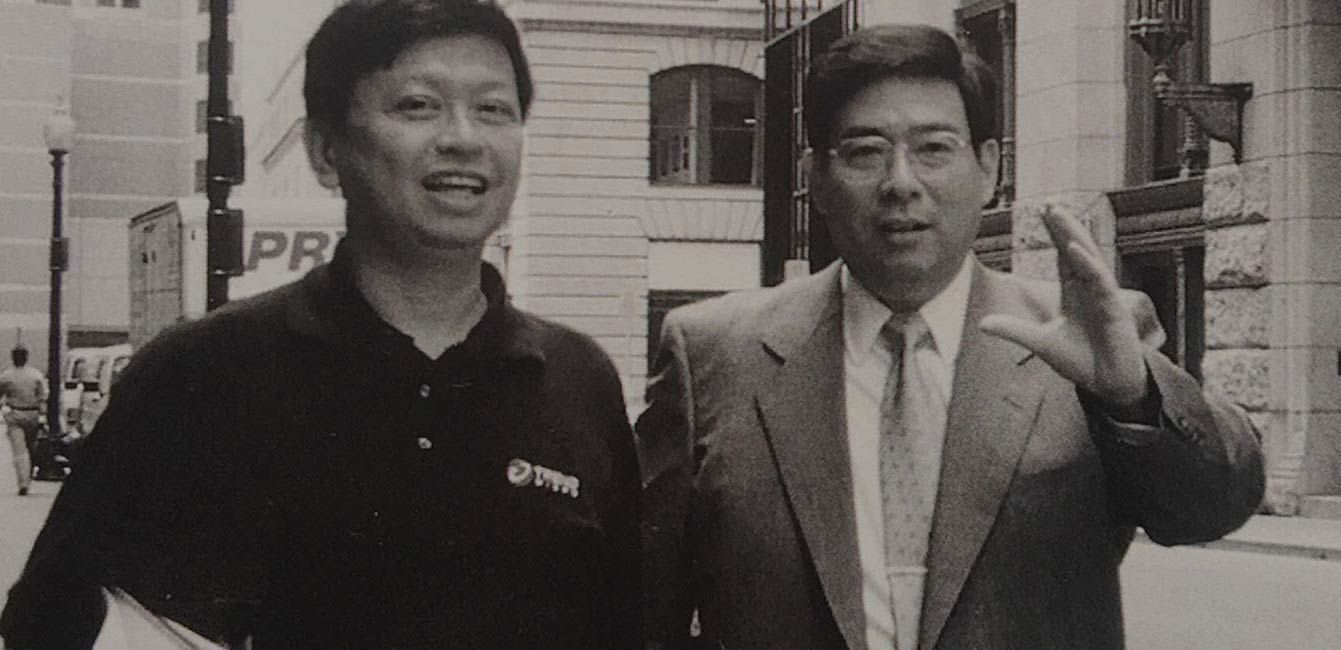
The history, people, and values behind the company.
Connect with us


