- About Trend Micro
-
- Careers
- History, Vision, Values
- Industry Recognition
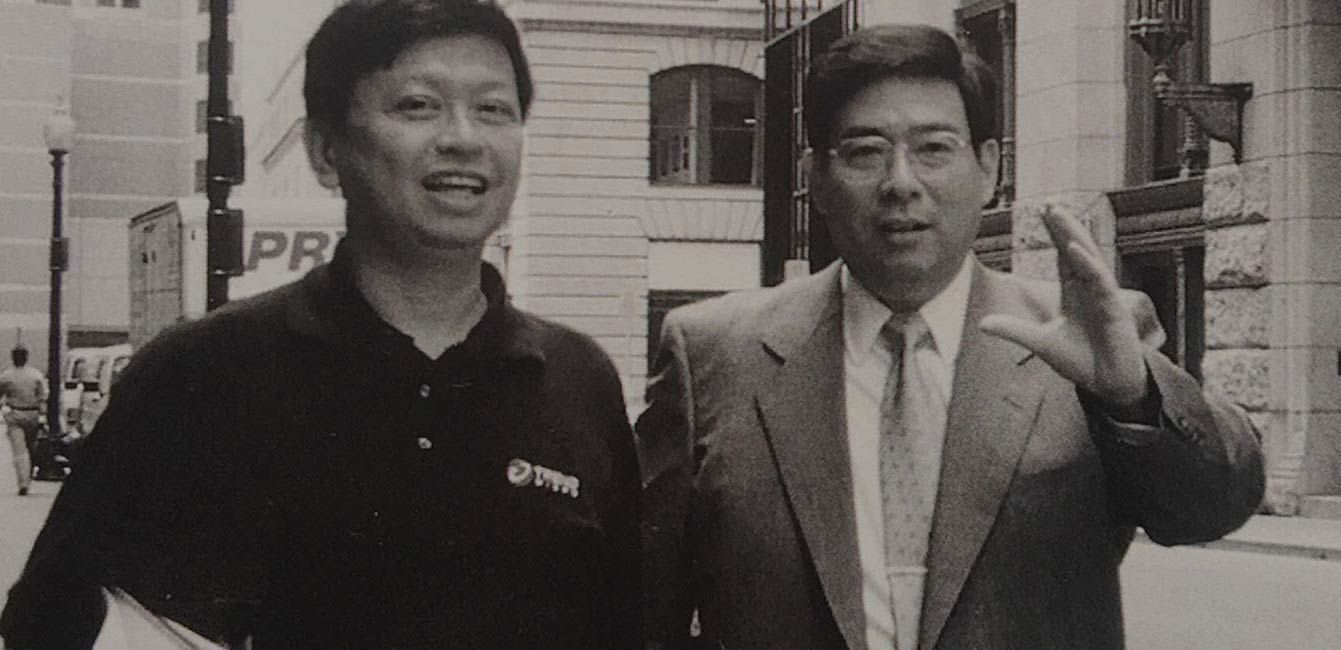
- Leaders
- Why Trend Micro
- Events
- Global Threat Research
- Corporate Social Responsibility
- Legal
- Diversity and Inclusion
- Trust Center
- Customer Stories
- Leading Experts
- Webinars
- Human Connections
- Webinars for customers
- Newsroom
- Healthcare
- Telecoms
- Financial Services
- Industry Insights Cards
- roles
- Retail
- End of Support
- Competitive Intelligence
Newsroom
Research, News, and Perspective
Author: Sara Atie (Product Marketing Manager)
QR Codes: Convenience or Cyberthreat?
Security awareness and measures to detect and prevent sophisticated risks associated with QR code-based phishing attacks (quishing)
Jul 23, 2024
Why NDR is Key to Cyber 'Pest Control'
Intruders are drawn to enterprise IT environments the way mice are attracted to houses. And once either kind of invader is inside, they can be hard to get out. Network detection and response (NDR) lets you trace intruders’ pathways to find out where they’re coming in—and seal the gaps.
Jul 22, 2024
Trend Experts Weigh in on Global IT Outage Caused by CrowdStrike
On July 19, 2024, a large-scale outage emerged affecting Windows computers for many industries across the globe from financial institutions to hospitals to airlines. The source of this outage came from a single content update from CrowdStrike.
Jul 19, 2024
DevOps Resource Center
Securing Application Staging & Production Environments
Is your staging environment secure? Explore the importance of assessing its security. Then, learn techniques and best practices to keep it, your other environments, and your company’s data safe from unauthorized access and data breaches.
Jan 09, 2024
Which DevOps Skills are the Hardest to Learn?
DevOps professionals face expansive challenges, from learning complex technologies to developing and honing interpersonal skills. Read on to discover some of the most difficult skills the role demands.
Nov 22, 2023
Top 10 DevOps Blunders and How to Sidestep Them
Integrating the necessary DevOps practices, tools, and cultures in an organization is difficult, even for experts. Learn how to recognize these challenges and transform them into valuable lessons when navigating the world of DevOps.
Nov 09, 2023
CISO Resource Center
Worldwide 2023 Email Phishing Statistics and Examples
Explore the need for going beyond built-in Microsoft 365 and Google Workspace™ security based on email threats detected in 2023.
Jun 20, 2024
Guide to Better Extended Threat Detection and Response (XDR)
Discover how XDR can enhance threat detection and response to improve a SecOps team’s efficiency and outcomes.
Jun 03, 2024
Author: David Chow (Chief Technology Strategy Officer)
A Necessary Digital Odyssey of RPA and AI/ML at HUD
Explore two RPA and AI/ML use cases at HUD during the operational challenges of the longest US Government shutdown, a rigid legacy IT environment, and complex federal regulations.
Mar 13, 2024
Media Contacts
Pick your region:
- USA
- AMEA
- Europe
- Latin America
- Japan
- Taiwan
Discover Trend Micro
The history, people, and values behind the company.
Connect with us


