
Ransomware attackers have ways to avoid cybersecurity measures, but you can protect your business. Some of the tactics to reduce your risk of infection include backups, user training, quarantining suspicious emails, and content filtering.
Table of Contents
Should you pay the ransom?
Cybersecurity researchers disagree as to whether you should pay. The FBI opposes paying the ransom. Some victims pay and gain access to their files; others pay and never receive a key. In the case of Petya, developers created the software with no method to decrypt data.
Overall, experts suggest cutting losses and not paying the ransom. Yet data loss can have a huge impact on your organization, and the amount of ransom hackers demand is increasing. Petya developers originally asked for $300 in bitcoins. Newer ransomware versions ask for hundreds of thousands of dollars in cryptocurrency. The ransomware business model exists only because the malicious actors behind it continue to be paid. If payment was taken off the table, the ransomware business model would collapse.
Paying the ransom does not guarantee you will get the private key to restore your data. Instead, protect your files by using protective measures in your day-to-day operations. In case of an attack, you can return files to their original state. This is why backups are critical to recovery from an attack.
Protective measures
- Backups
- User training
- Quarantining suspicious emails
- Content filtering
Train users to detect ransomware
User training greatly reduces infection risk. A ransomware attack usually starts with a malicious email. Users can be trained to identify cyber threats including ransomware, phishing, and social engineering. Users trained to identify malicious messages are less likely to open an infected attachment.
Hackers sometimes use social engineering in their attacks. Social engineering is when an attacker targets specific users on the network who have higher privileges. The attackers bet that these users have more critical data on local storage or have access to business critical systems and infrastructure. This increases the chance that the business will pay the ransom.
Keep software patched and updated
Make sure firmware, anti-malware applications, operating systems, and third-party software have the latest patch installed. New ransomware versions come out regularly, and software updates ensure that your anti-malware recognizes newer threats.
WannaCry is an example of an operating system threat. It incorporated EternalBlue, an exploit developed by the United States National Security Agency (NSA). It leveraged a weakness in the Windows operating system Server Message Block (SMB) protocol. Microsoft published patches to stop WannaCry 30 days prior to the infections. Without the patches, Windows operating systems are vulnerable.
More recently we’ve seen ZeroLogon being used in ransomware attacks.
Always have backups
The best way to recover from ransomware is to restore data from a backup. Backups bypass the ransom demand by restoring data from a source other than the encrypted files. Hackers know this, so they develop ransomware that scans the network for backup files. After restoring from a backup, you still must remove the ransomware from the network.
An effective way to stop malware from encrypting backup files is to keep a copy of your backups offsite. Cloud backups are the typical choice for businesses that need an offsite backup solution. Using cloud backups, you keep a copy of your files safe from ransomware and other cybersecurity threats.
Detecting ransomware
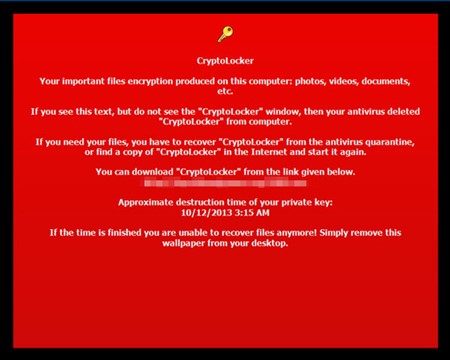
A ransomware attack typically comes from an executable file or a script that downloads the executable file and runs it. Not every ransomware attack is immediate. Some ransomware stays dormant until a specific date. For instance, a type of ransomware named Locker, a CryptoLocker copycat, was silent until midnight May 25, 2015 when it executed its payload.
Network administrators detect ransomware with applications that monitor suspicious network traffic. The applications send notifications when malware renames a large number of files. Anti-malware software protects against thousands of types of ransomware. It contains digital signatures that identify ransomware before it can execute. It does not always catch zero-day attacks – those that target vulnerabilities developers don’t know about yet.
Current anti-malware solutions include artificial intelligence (AI), machine learning and behavior monitoring. These solutions benchmark current file status against changes and file access requests. They alert administrators of suspicious activity so an attack can be resolved early and prevent file encryption and data destruction.
Early detection helps prevention
Effective ransomware prevention requires a combination of good monitoring applications, frequent file backups, anti-malware software, and user training. Although no cyber-defenses reduce risk completely, you can greatly limit the chance attackers will be successful.
Trend Micro Cyber Risk Report - 2025
Ransomware is a form of cyber extortion where attackers encrypt critical data and demand payment for its release. As highlighted in the Trend Micro 2025 Cyber Risk Report, ransomware remains one of the most visible and financially damaging threats to organizations worldwide.
Ransomware operators are no longer relying solely on traditional entry points like phishing emails or exposed RDP ports. Instead, they are exploiting overlooked and emerging vulnerabilities across an organization's digital ecosystem—what cybersecurity experts call the attack surface.
Discover how ransomware threats are evolving and what proactive strategies can help mitigate risk in Trend Micro’s 2025 Cyber Risk Report
How Trend Micro Helps You Stay Ahead of Ransomware Threats
As ransomware continues to be one of the most disruptive threats facing organizations today, the need for a unified, intelligent defense has never been greater. Trend Vision One™ offers a powerful solution that goes beyond traditional security tools—providing extended detection and response (XDR), attack surface risk management, and automated threat mitigation in a single, integrated platform.
With Trend Vision One™, security teams gain centralized visibility across endpoints, email, cloud, and network layers, enabling faster detection and response to ransomware activity. Backed by decades of threat intelligence and powered by Trend Micro’s Cybersecurity AI, the platform helps organizations proactively identify vulnerabilities, reduce exposure, and stop ransomware before it can cause damage.
Frequently Asked Questions (FAQs)
What should you do if you receive a ransomware demand?
Disconnect affected systems, avoid paying ransom, report the incident, notify security teams, preserve evidence, and begin recovery using backups and professional support.
What are the most effective ways to prevent ransomware attacks?
Effective prevention includes strong authentication, regular updates, email filtering, endpoint protection, network segmentation, employee training, and maintaining secure, isolated backups.
How does employee training help prevent ransomware?
Training teaches employees to recognize phishing, avoid unsafe downloads, follow security best practices, report suspicious activity, and reduce overall ransomware risk.
Why are backups important for ransomware protection?
Backups enable fast recovery, avoid ransom payments, minimize downtime, protect critical data, and maintain business continuity after ransomware-related data loss.