Identity has become the primary attack surface in modern enterprises. As organisations expand across cloud platforms, SaaS ecosystems, and distributed workforces, attackers increasingly exploit human behaviour, misconfiguration, and fragmented controls. Nearly 60% of breaches involve a human element — including error, misuse, or social engineering, according to the 2025 Verizon Data Breach Investigations Report (DBIR).
Insider risk, credential misuse, and AI‑generated phishing now converge to create a boundaryless threat environment where a single compromised identity can trigger operational, financial, and reputational damage.
Identity at the core of modern cybersecurity.
The December 2025 Gartner® Identity & Access Management Summit brought together thousands of security leaders and practitioners. As per our understanding, it underscores a clear industry shift: identity is now the organising principle of modern cybersecurity, not a supporting control.
This theme: Identity at the Core, highlighted how organisations are re‑architecting security around identity visibility, identity intelligence, and identity‑driven response. Sessions emphasised that enterprises are struggling most with the response stage of the updated NIST 2.0 Cybersecurity Framework, where identity compromise is often the earliest indicator of an attack.
The event also showcased the rapid emergence of Agentic AI, with demonstrations illustrating how AI‑driven identity intelligence is reshaping detection, response, and automation across human, non‑human, and AI‑agent identities. Across keynotes and analyst sessions, one message was consistent: organisations need Identity Visibility and Intelligence Platforms (IVIP) that unify signals across identity providers, cloud platforms, and access controls.
Risky behaviour, events, errors, and tactics.
Identity's scope is widening, and threats are evolving with AI. This brings new risk levels to organisations, impacting their security posture, escalating errors by humans, machine identities and AI agents, and introducing new attack vectors.
1. Insider risk weakens enterprise security.
Insider incidents continue to rise as employees, contractors, machine identities (such as API keys, certificates, secrets, OAuth tokens, and service accounts), and even AI agents gain broader access to sensitive systems. Most insider events are unintentional; including misdirected data, unsafe sharing, or credential exposure, yet the consequences are significant: data loss, compliance violations, and operational disruption.
Industries with high data sensitivity, such as financial services, healthcare, government, and education, face the greatest exposure due to complex access models and large user populations.
Without identity‑centric visibility organisations struggle to detect early behavioural anomalies or privilege misuse, especially when insiders unknowingly become conduits for external attackers.
2. Errors by humans, non‑human identities, and AI agents.
Human error continues to be one of the most common contributors to identity‑related incidents. Misconfigurations, weak authentication practices, and accidental data exposure frequently open the door to attackers, especially in hybrid and cloud‑first environments. Organisations face escalating costs from downtime, incident response, regulatory penalties, and customer churn. But in the AI era, errors are no longer limited to humans.
Non‑human identity errors
Machine identities, service accounts, and API keys now outnumber human identities by a wide margin. These identities often have:
- No behavioural baselines
- Excessive or persistent privileges
- Hard‑coded credentials
- Limited monitoring
A single misconfigured service account can grant attackers persistent access to cloud workloads, CI/CD pipelines, or sensitive data repositories.
AI‑agent errors
As organisations adopt autonomous and semi‑autonomous AI agents, new risks emerge:
- AI agents making incorrect access decisions
- Agents interacting with systems beyond intended scope
- AI-driven automation amplifying misconfigurations
- AI agents being manipulated through prompt injection or data poisoning
Gartner predicts that “By 2027, AI agents will reduce the time it takes to exploit account exposures by 50%.” Autonomous AI agents are emerging as a new insider-like threat, capable of accelerating account misuse, exploiting weak authentication, and operating at a scale that challenges organisations’ security readiness.
Therefore, identity protection must account for:
- Human identities: individual users and their associated user identities
- Machine identities: non-human identities such as service accounts, API keys, certificates, and other automated credentials
- AI agents: autonomous systems that interact with applications and data, each with unique risks and failure modes
These identity types require continuous monitoring, intent validation, and guardrails to prevent cascading failures.
3. AI‑generated attacks mimic human behaviour.
AI‑generated phishing and business email compromise (BEC) campaigns now mimic internal language, workflows, and executive communication with alarming accuracy. Attackers target individuals with the highest access value: finance teams, IT admins, HR, and executives, making the human factor the most exploited entry point.
TrendAI highlights a significant rise in AI‑generated phishing, QR‑based lures, and impersonation attacks that bypass traditional filters.
Cybercriminals now use AI to:
- Impersonate executives
- Generate deepfake audio for urgent requests
- Craft context‑aware phishing emails
- Automate credential harvesting
- Launch multi‑channel social engineering campaigns
AI has dramatically increased the speed, scale, and believability of identity-based attacks. Reactive security and traditional defences cannot keep up with the speed and sophistication of AI-powered attacks.
Fragmented identity visibility creates blind spots.
Security teams struggle with fragmented visibility across identity providers, cloud platforms, hybrid environments, and the siloed identity tools that manage them; such as: IAM (Identity and Access Management systems that authenticate and authorise users), PAM (Privileged Access Management tools that control elevated accounts), and IGA (Identity Governance and Administration solutions that manage identity lifecycle and compliance).
Analysts often cannot see the complete picture of identity activity across:
- On-premises directories
- Cloud identity providers
- SaaS applications
- Machine identities
- AI agents
This fragmentation creates blind spots where attackers hide, especially during lateral movement or privilege escalation. As organisations lack unified visibility across identity systems, this makes it difficult to detect coordinated identity‑driven attacks:
Security teams are buried in identity alerts.
As a shared role in organisations – IT admins, security operations, and compliance collaboratively looking after identity security. Identity‑related alerts have surged, but most lack context. Analysts are forced to triage chronologically rather than by risk, making it difficult to distinguish between isolated incidents and coordinated attacks. This overwhelming volume creates dangerous blind spots where critical threats can be missed.
Alert fatigue is now an identity problem, not just a SOC problem.
Slow and manual containment gives attackers time.
When identity compromise occurs, response is slow and fragmented. Security analysts must coordinate across multiple systems to perform basic actions like:
- Account lockouts
- Credential resets
- Session terminations
- Privilege revocation
This manual process gives attackers precious time to escalate privileges or exfiltrate data. Identity incidents require automated containment, not manual workflows.
Shift to proactive human risk management
Organizations increasingly recognise that identity is the foundation of modern cybersecurity, requiring a shift from reactive tactics to proactive, intelligence‑driven protection. By combining unified visibility with AI‑powered insights, security teams can anticipate identity threats before they escalate.
Prevent identity threats before they strike.
Security teams must prioritise identity risks across their entire attack surface to focus on the most critical exposures. With complete visibility, they can uncover hidden attack paths, understand how identities interact across endpoints, cloud services, and SaaS applications, and prevent compromise before it occurs. Strengthened by the TrendAI Vision One platform, security teams gain continuous assessments that reveal high‑impact vulnerabilities early. Admins and SecOps can look beyond traditional asset discovery and analyse accounts, identities, and behaviours—visualising in real time how incidents spread, what they affect, and who is at risk.
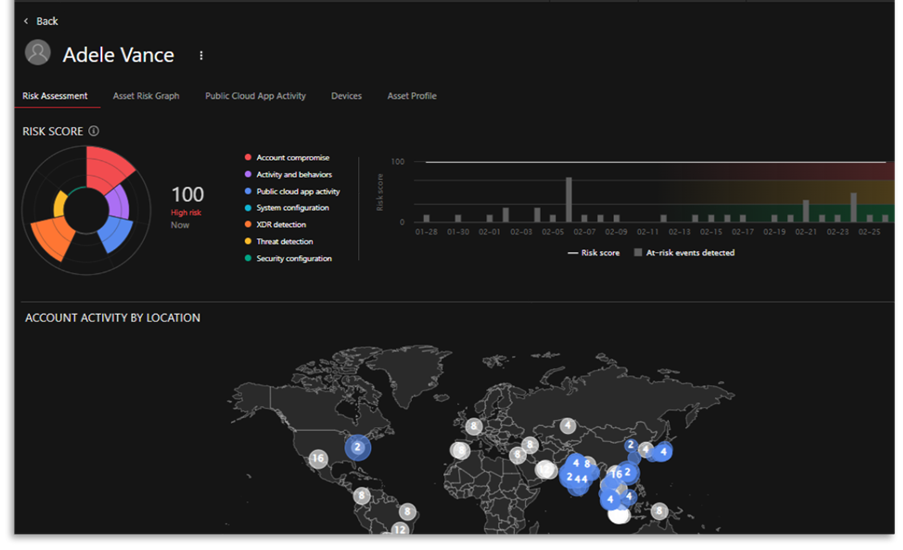
Figure: In-depth Identity Profiles
Unified visibility across Entra ID, Active Directory, Google, Okta, CyberArk, and OpenLDAP helps uncover misconfigurations, privilege issues, dormant accounts, risky behaviours, and emerging AI‑agent anomalies.
Complete identity awareness
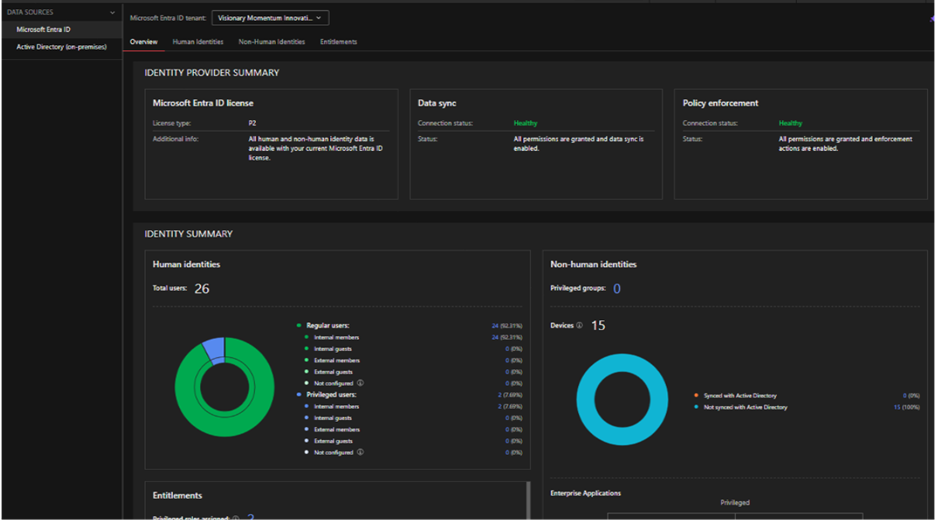
Figure: Identity-focused Inventory
An identity‑focused inventory provides a consolidated view of all identities and activities, building behavioural baselines across endpoints, email, SaaS, and web. This gives security teams actionable insights to strengthen identity posture, uncover vulnerabilities, and limit unnecessary access, building behavioural baselines across assets.
TrendAI Vision One™ delivers Identity Security Posture Management (ISPM) through Cyber Risk Exposure Management (CREM), enabling organisations to identify issues such as over‑privileged accounts, weak authentication policies, misconfigurations, and identity‑layer attack paths.
Alert clarity and risk mitigation
The platform exposes risks such as compromised corporate credentials and factors in contextual identity criticality; whether the user is a system admin, a finance leader, or an intern; to prioritise remediation aligned with Zero Trust principles.
Swift response across any system
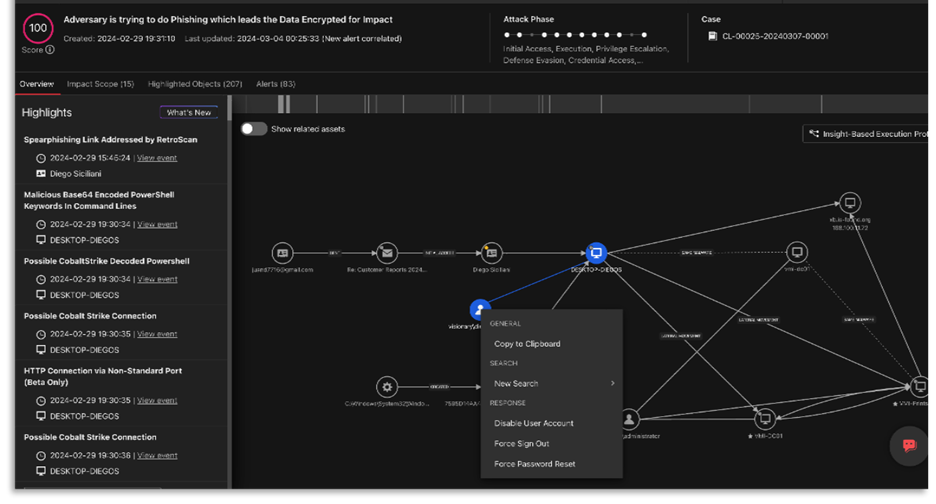
Figure: Automating response and executing containment actions
Security teams can rapidly mitigate identity‑based threats by automating remediation actions across systems, eliminating manual steps, and reducing response time. TrendAI Vision One™ provides powerful Identity Threat Detection and Response (ITDR) capabilities, enriched with endpoint, cloud, network, and email telemetry to detect early signs of account takeover, privilege escalation, lateral movement, and AI‑agent misuse.
Predefined playbooks turn manual tasks into one‑click actions—enforcing account lockouts, sign‑outs, password resets, or dynamic access restrictions instantly. Integrated User and Entity Behaviour Analytics (UEBA) and Observed Attack Techniques (OAT) enrich threat context to surface identity‑centric alerts earlier and more accurately. Identity‑first security is the only scalable way to reduce human and AI‑driven risk.
Framework for Proactive Identity Security
Identity sits at the core of a modern security architecture. A proactive, identity-first security approach integrates visibility, threat detection and response, zero trust enforcement, AI protection, and threat intelligence into a unified model.
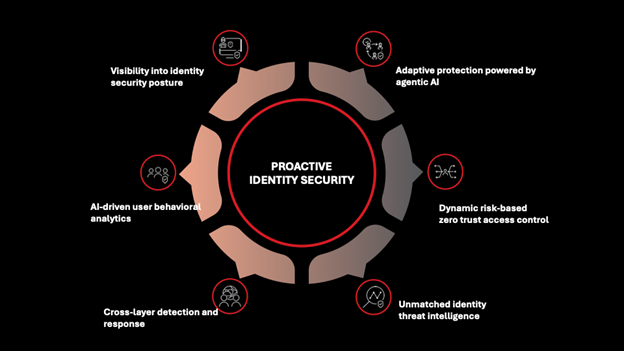
Figure: Proactive identity-first security framework
This framework combines critical identity architecture with advanced capabilities to deliver proactive, adaptive protection. For instance, adaptive identity protection evolves with real-world signals to assess security posture and detect advanced threats like MFA bypass and insider risk.
The AI-powered identity security autonomously analyses intent, predicts attack paths, and recommends or executes mitigation steps. This includes coverage for:
- Human identities: people interacting with systems, including employees, contractors, and their associated user identities
- Machine identities (including service accounts): credentials used by software, workloads, APIs, certificates, and service accounts to authenticate and operate
- AI agents: autonomous systems that make decisions, perform tasks, and interact with data and applications
Zero Trust principles ensure continuous verification and least-privilege access, reducing the blast radius of any compromised identity. Learn more.
What TrendAI Vision One™ Offers
TrendAI Vision One™ Identity Security empowers organisations to lead the future with identity-centric cybersecurity that unifies visibility and awareness, intelligent risk prioritisation, and proactive protection with automated mitigation actions. Built to inspire innovation and eliminate risk, our solution secures human, machine, and AI agent identities so you can advance without compromise.
Gain the comprehensive protection you need in a hybrid, identity‑centric world, allowing you to respond to threats before damage occurs. The adaptive platform automatically discovers every identity and continuously monitors activity across your digital estate, including endpoints, networks, cloud applications, OT/IoT, email, AI applications, and data.
As the only solution delivering this level of unified visibility, proactive risk intelligence, and automated response, TrendAI Vision One™ provides the complete identity‑centric protection modern enterprises need at scale.
- Powered by Cyber Risk Exposure Management, organisations can strengthen identity hygiene, uncover misconfigurations across identity providers, improve identity posture, monitor behaviour in real time, and build stronger security awareness across the enterprise.
- Strengthened with Security Operations, security teams can correlate identity signals with endpoint, cloud, network and email telemetry to detect account takeover, privilege escalation, lateral movement, and AI‑agent misuse—automating remediation at scale.
- Enriched by Email and Collaboration Security, the platform blocks sophisticated phishing, impersonation, account takeover, and credential‑harvesting attacks before they reach users. The AI‑driven correlated intelligence detection proactively identifies and mitigates human risk with greater speed and precision.
Together, these capabilities give enterprises complete visibility, prioritised risk insights, and automated mitigation — enabling visibility and AI intelligence that power identity-first security without compromise.
Thrive in the AI age – securely. Free Trial

