TROJ_FAKEAV.EKM
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Trojan may arrive as an attachment to a malicious email. Upon execution, it notifies its server regarding the installation by accessing a certain URL.It then displays fake warning messages.
If the user registers the software, he is redirected to URLs where his credit card information are asked to purchase the product.
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users. It may be unknowingly downloaded by a user while visiting malicious websites.
It deletes the initially executed copy of itself.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
It may be unknowingly downloaded by a user while visiting malicious websites.
Installation
This Trojan drops the following copies of itself into the affected system and executes them:
- %All Users%\Application Data\F4D55F3E0005B4D900017079D151FC4E\F4D55F3E0005B4D900017079D151FC4E.exe
It drops the following files:
- %User Profile%\Desktop\Smart Protection 2012.lnk
- %Start Menu%\Programs\Smart Protection 2012\Smart Protection 2012.lnk
(Note: %User Profile% is the current user's profile folder, which is usually C:\Windows\Profiles\{user name} on Windows 98 and ME, C:\WINNT\Profiles\{user name} on Windows NT, and C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003.. %Start Menu% is the current user's Start Menu folder, which is usually C:\Windows\Profiles\{user name}\Start Menu on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Start Menu on Windows NT and C:\Windows\Start Menu or C:\Documents and Settings\{User name}\Start Menu on Windows 2000, XP, and Server 2003.)
It creates the following folders:
- %All Users%\Application Data\F4D55F3E0005B4D900017079D151FC4E
- %All Users%\Application Data\F4D55F3E0005B4D900017079D151FC4E\F4D55F3E0005B4D900017079D151FC4E
- %Start Menu%\Programs\Smart Protection 2012
(Note: %Start Menu% is the current user's Start Menu folder, which is usually C:\Windows\Profiles\{user name}\Start Menu on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Start Menu on Windows NT and C:\Windows\Start Menu or C:\Documents and Settings\{User name}\Start Menu on Windows 2000, XP, and Server 2003.)
Other System Modifications
This Trojan adds the following registry keys:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Uninstall\
Smart Protection 2012
It adds the following registry entries:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\RunOnce
F4D55F3E0005B4D900017079D151FC4E = "%All Users%\Application Data\F4D55F3E0005B4D900017079D151FC4E\F4D55F3E0005B4D900017079D151FC4E.exe"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Uninstall\
Smart Protection 2012
DisplayName = "Smart Protection 2012"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Uninstall\
Smart Protection 2012
ShortcutPath = ""%All Users%\Application Data\F4D55F3E0005B4D900017079D151FC4E\F4D55F3E0005B4D900017079D151FC4E.exe" Uninstall""
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Uninstall\
Smart Protection 2012
UninstallString = "%All Users%\Application Data\F4D55F3E0005B4D900017079D151FC4E\F4D55F3E0005B4D900017079D151FC4E.exe" Uninstall
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Uninstall\
Smart Protection 2012
DisplayIcon = "%All Users%\Application Data\F4D55F3E0005B4D900017079D151FC4E\F4D55F3E0005B4D900017079D151FC4E.exe,0
Other Details
This Trojan deletes the initially executed copy of itself
NOTES:
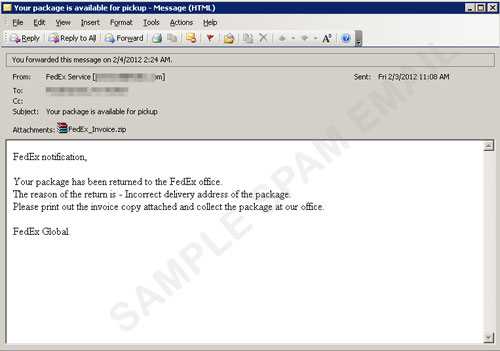
It may arrive as an attachment to a malicious email:
Upon execution, it notifies its server regarding the installation by accessing the URL below:
- http://{BLOCKED}8.{BLOCKED}2.174.135/api/stats/install/?affid={id}&ver={ver}&group=sp
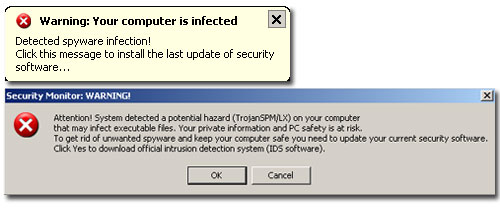
It then displays fake warning messages as shown in the screenshots below:
If the user clicks OK, the Smart Protection GUI appears:
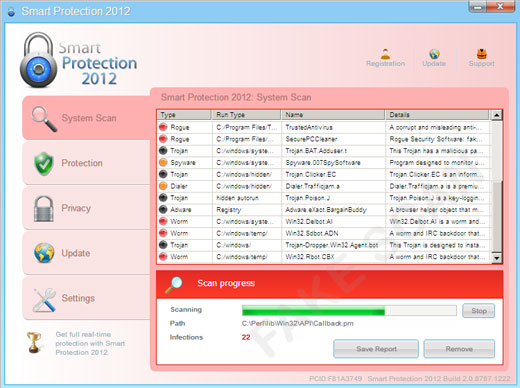
It pretends to scan the system and displays fake infections.
If the user registers the software, he is redirected to the following URLs where his credit card information are asked to purchase the product.
- http://{BLOCKED}8.{BLOCKED}2.170.125/p/?aid=test&lid={id}&affid={affid}&nid={nid}&group=sp
- http://{BLOCKED}8.{BLOCKED}2.170.125/p/ch/?lid={id}&group=sp&nid={nid}&s=4&aaffid={affid}&aid=test
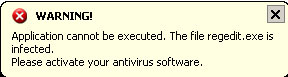
Process Termination
It terminates all executed files and displays the message below:
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Restart in Safe Mode
Step 3
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
- F4D55F3E0005B4D900017079D151FC4E = %All Users%\Application Data\F4D55F3E0005B4D900017079D151FC4E\F4D55F3E0005B4D900017079D151FC4E.exe
- F4D55F3E0005B4D900017079D151FC4E = %All Users%\Application Data\F4D55F3E0005B4D900017079D151FC4E\F4D55F3E0005B4D900017079D151FC4E.exe
Step 4
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Smart Protection 2012Step 5
Search and delete this file
- %User Profile%\Desktop\Smart Protection 2012.lnk
Step 6
Search and delete these folders
- %All Users%\Application Data\F4D55F3E0005B4D900017079D151FC4E
- %Start Menu%\Programs\Smart Protection 2012
Step 7
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TROJ_FAKEAV.EKM. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


