RANSOM_ELFEREBUS.A
Ransom:Linux/Erebus.A(Microsoft); Ransom.Erebus(Symantec)
Linux


Threat Type: Ransomware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
Dropped by other malware, Downloaded from the Internet
This malware is a variant of the ransomware family EREBUS and was discovered to be involved in an attack against South Korean webhosting company NAYANA. Users affected by this malware may find their personal files and documents encrypted and thus rendered useless.
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It connects to certain websites to send and receive information. It deletes itself after execution.
It encrypts files with specific file extensions. It drops files as ransom note.
TECHNICAL DETAILS
429,144 bytes
ELF
Yes
13 Jun 2017
Connects to URLs/IPs, Steals information, Encrypts files
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
- {malware path}\./{5f58d6f0-bb9c-46e2-a4da-8ebc746f24a5}//log.log ← log file
- \var\tmp\.{Hash}.conf ← config file
Other Details
This Ransomware connects to the following website to send and receive information:
- {BLOCKED}.{BLOCKED}.224.128/24
It does the following:
- It encrypt files with the following filenames:
- ibdata0
- ibdata1
- ibdata2
- ibdata3
- ibdata4
- ibdata5
- ibdata6
- ibdata7
- ibdata8
- ibdata9
- ib_logfile0
- ib_logfile1
- ib_logfile2
- ib_logfile3
- ib_logfile4
- ib_logfile5
- ib_logfile6
- ib_logfile7
- ib_logfile8
- ib_logfile9
- It creates a CRON task to automatically execute itself every hour:
- /etc/cron.hourly/96anacron
- It creates a fake Bluetooth service to automatically execute itself every start-up:
- /etc/rc.d/init.d/bluetooth
- /etc/rc.d/rc2.d/S25bluetooth
- /etc/rc.d/rc3.d/S25bluetooth
- /etc/rc.d/rc4.d/S25bluetooth
- /etc/rc.d/rc5.d/S25bluetooth
- It gathers the following information which it sends to its remote server:
- Private Key
- Public Key
- Malware install path
- Operating System
- Operating System version and architecture
- Timezone
- Language
- Network Adapter
- IP Address
- MAC Address
It deletes itself after execution.
Ransomware Routine
This Ransomware encrypts files with the following extensions:
- .1cd
- .3dm
- .3ds
- .3fr
- .3g2
- .3gp
- .3pr
- .7z
- .7zip
- .aac
- .ab4
- .abd
- .accdb
- .accde
- .accdr
- .accdt
- .ach
- .acr
- .act
- .adb
- .adp
- .ads
- .agdl
- .ai
- .aiff
- .ait
- .al
- .aoi
- .apj
- .arw
- .ascx
- .asf
- .asm
- .asp
- .aspx
- .asx
- .atb
- .avi
- .awg
- .back
- .backup
- .backupdb
- .bak
- .bank
- .bay
- .bdb
- .bgt
- .bik
- .bin
- .bkp
- .blend
- .bmp
- .bpw
- .bz
- .bz2
- .c
- .cdb
- .cdf
- .cdr
- .cdr3
- .cdr4
- .cdr5
- .cdr6
- .cdrw
- .cdx
- .ce1
- .ce2
- .cer
- .cfg
- .cfn
- .cgm
- .cib
- .class
- .cls
- .cmt
- .config
- .contact
- .cpi
- .cpp
- .cr2
- .craw
- .crt
- .crw
- .cs
- .csh
- .csl
- .css
- .csv
- .dac
- .dat
- .db
- .db3
- .db_journal
- .dbf
- .dbx
- .dc2
- .dcr
- .dcs
- .ddd
- .ddoc
- .ddrw
- .dds
- .def
- .der
- .des
- .design
- .dgc
- .dit
- .djvu
- .dng
- .doc
- .docm
- .docx
- .dot
- .dotm
- .dotx
- .drf
- .drw
- .dtd
- .dwg
- .dxb
- .dxf
- .dxg
- .edb
- .eml
- .eps
- .erbsql
- .erf
- .exf
- .fdb
- .ffd
- .fff
- .fh
- .fhd
- .fla
- .flac
- .flb
- .flf
- .flv
- .flvv
- .fpx
- .fxg
- .gif
- .gray
- .grey
- .groups
- .gry
- .gz
- .h
- .hbk
- .hdd
- .hpp
- .html
- .ibank
- .ibd
- .ibz
- .idx
- .iif
- .iiq
- .incpas
- .indd
- .info
- .info_
- .ini
- .jar
- .java
- .jnt
- .jpe
- .jpeg
- .jpg
- .js
- .json
- .kc2
- .kdbx
- .kdc
- .key
- .kpdx
- .kwm
- .laccdb
- .lck
- .ldf
- .lit
- .lock
- .log
- .lua
- .lz
- .lz4
- .lzma
- .m
- .m2ts
- .m3u
- .m4p
- .m4v
- .mab
- .mapimail
- .max
- .mbx
- .md
- .mdb
- .mdc
- .mdf
- .mef
- .mfw
- .mid
- .mkv
- .mlb
- .mmw
- .mny
- .moneywell
- .mos
- .mov
- .mp3
- .mp4
- .mpeg
- .mpg
- .mrw
- .msf
- .msg
- .myd
- .nd
- .ndd
- .ndf
- .nef
- .nk2
- .nop
- .nrw
- .ns2
- .ns3
- .ns4
- .nsd
- .nsf
- .nsg
- .nsh
- .nvram
- .nwb
- .nx2
- .nxl
- .nyf
- .oab
- .obj
- .odb
- .odc
- .odf
- .odg
- .odm
- .odp
- .ods
- .odt
- .ogg
- .oil
- .omg
- .orf
- .ost
- .otg
- .oth
- .otp
- .ots
- .ott
- .p12
- .p7b
- .p7c
- .pab
- .pages
- .pas
- .pat
- .pbf
- .pcd
- .pct
- .pdb
- .pdd
- .pef
- .pem
- .pfx
- .php
- .pif
- .pl
- .plc
- .plus_muhd
- .pm
- .pm!
- .pmi
- .pmj
- .pml
- .pmm
- .pmo
- .pmr
- .pnc
- .pnd
- .png
- .pnx
- .pot
- .potm
- .potx
- .ppam
- .pps
- .ppsm
- .ppsm
- .ppsx
- .ppt
- .pptm
- .pptm
- .pptx
- .prf
- .ps
- .psafe3
- .psd
- .pspimage
- .pst
- .ptx
- .pwm
- .py
- .qba
- .qbb
- .qbm
- .qbr
- .qbw
- .qbx
- .qby
- .qcow
- .qcow2
- .qed
- .qtb
- .r3d
- .raf
- .rar
- .rat
- .raw
- .rdb
- .rm
- .rtf
- .rvt
- .rw2
- .rwl
- .rwz
- .s3db
- .safe
- .sas7bdat
- .sav
- .save
- .say
- .sd0
- .sda
- .sdb
- .sdf
- .sh
- .sldm
- .sldx
- .sql
- .sqlite
- .sqlite-shm
- .sqlite-wal
- .sqlite3
- .sqlitedb
- .sr2
- .srb
- .srf
- .srs
- .srt
- .srw
- .st4
- .st5
- .st6
- .st7
- .st8
- .stc
- .std
- .sti
- .stm
- .stw
- .stx
- .svg
- .swf
- .sxc
- .sxd
- .sxg
- .sxi
- .sxm
- .sxw
- .tar
- .taz
- .tbb
- .tbn
- .tbz
- .tex
- .tga
- .tgz
- .thm
- .tif
- .tlg
- .tlx
- .txt
- .usr
- .vbox
- .vdi
- .vhd
- .vhdx
- .vmdk
- .vmsd
- .vmx
- .vmxf
- .vob
- .wab
- .wad
- .wallet
- .war
- .wav
- .wb2
- .wma
- .wmf
- .wmv
- .wpd
- .wps
- .x11
- .x3f
- .xis
- .xla
- .xlam
- .xlk
- .xlm
- .xlr
- .xls
- .xlsb
- .xlsm
- .xlsx
- .xlt
- .xltm
- .xltx
- .xlw
- .xml
- .ycbcra
- .yuv
- .zip
It avoids encrypting files with the following strings in their file path:
- bin
- boot
- dev
- etc
- lib
- lib64
- proc
- run
- sbin
- srv
- sys
- tmp
- usr
- var
- .gem
- .bundle
- .nvm
- .npm
It renames encrypted files using the following names:
- {random filename}.ecrypt
It drops the following file(s) as ransom note:
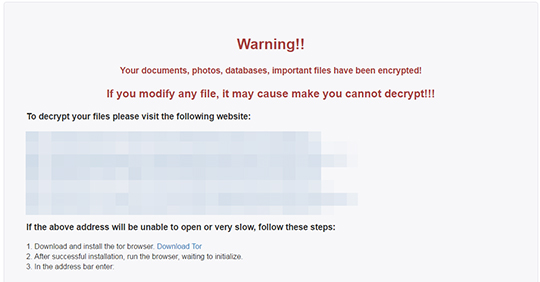
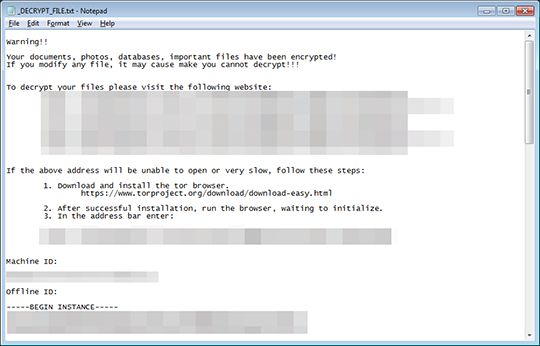
- {folder of encrypted files}\_DECRYPT_FILE.txt
- {folder of encrypted files}\_DECRYPT_FILE.html
- {folder of encrypted files}\index.html
SOLUTION
9.850
13.470.08
14 Jun 2017
13.471.00
15 Jun 2017
Step 1
Scan your computer with your Trend Micro product to delete files detected as RANSOM_ELFEREBUS.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 2
Restore encrypted files from backup.
Did this description help? Tell us how we did.


