TSPY_BANKER.DYR
Trojan:Win32/Malagent!gmb (Microsoft), Backdoor.Win32.Dyreza.d (Kaspersky), Win32/Battdil.C (ESET), W32/Dyreza.C!tr.bdr (Fortinet), Win32:Malware-gen (Avast)
Windows


Threat Type: Spyware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
Dropped by other malware
This malware is the Dyre banking Trojan, also known as “Dyreza."
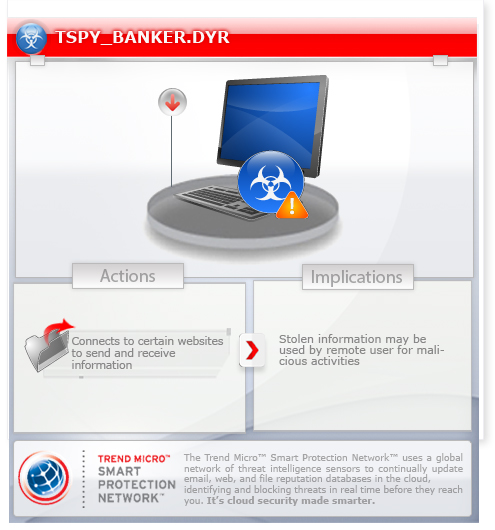
To get a one-glance comprehensive view of the behavior of this Spyware, refer to the Threat Diagram shown below.
This Spyware may be dropped by other malware.
It may be injected into processes running in memory.
It connects to certain websites to send and receive information.
TECHNICAL DETAILS
Varies
DLL
Yes
09 Sep 2014
Steals information, Connects to URLs/IPs
Arrival Details
This Spyware may be dropped by other malware.
Installation
This Spyware drops the following file(s)/component(s):
- %Application Data%\whr458da.db - configuration file
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Roaming on Windows Vista, 7, and 8.)
It injects itself into the following processes running in the affected system's memory:
- chrome.exe
- firefox.exe
- iexplore.exe
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- Global\cdv5b74f5y7
It may be injected into processes running in memory.
Other Details
This Spyware connects to the following URL(s) to get the affected system's IP address:
- http://BLOCKED}hazip.com
It connects to the following website to send and receive information:
- {BLOCKED}.{BLOCKED}34.142.186:443
- {BLOCKED}.{BLOCKED}55.183.98:443
- {BLOCKED}.{BLOCKED}65.249.224:443
- {BLOCKED}.{BLOCKED}65.212.188:443
- {BLOCKED}.{BLOCKED}65.194.117:443
- {BLOCKED}.{BLOCKED}7.71.122:443
- {BLOCKED}.{BLOCKED}.236.54:443
- {BLOCKED}.{BLOCKED}65.204.210:443
- {BLOCKED}.{BLOCKED}.250.88:443
- {BLOCKED}.{BLOCKED}.220.166:443
- {BLOCKED}.{BLOCKED}65.204.223:443
- {BLOCKED}.{BLOCKED}65.237.178:443
- {BLOCKED}.{BLOCKED}65.237.144:443
- {BLOCKED}.{BLOCKED}65.237.145:443
- {BLOCKED}.{BLOCKED}65.237.145:443
NOTES:
It may update its configuration file and obtain entities to target through the C&C servers specified in the default configuration file.
SOLUTION
9.700
11.139.00
10 Sep 2014
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Search and delete this file
- %Application Data%\whr458da.db
Step 4
Scan your computer with your Trend Micro product to delete files detected as TSPY_BANKER.DYR. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.


