HTML_BLOCKER.K
Windows 2000, Windows Server 2003, Windows XP (32-bit, 64-bit), Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Others
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This malware is related to the fake Flash player scams that targeted users in Turkey. It is used to send the Facebook messages with the link to the video.
To get a one-glance comprehensive view of the behavior of this Others, refer to the Threat Diagram shown below.
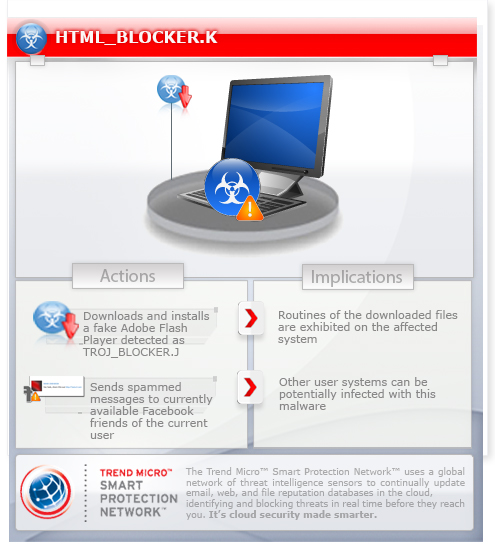
This malware may be downloaded by other malware/grayware from remote sites. It executes when a user accesses certain websites where it is hosted. It may be downloaded from remote sites by other malware.
TECHNICAL DETAILS
Arrival Details
This malware may be downloaded by the following malware/grayware from remote sites:
- http://www.{BLOCKED}p.us/user.php
It executes when a user accesses certain websites where it is hosted.
It may be downloaded from remote site(s) by the following malware:
- JS_BLOCKER.J
NOTES:
It makes the current user follow certain accounts when the following social networking sites are accessed:
- twitter.com
- ask.fm
It spams messages to currently available Facebook friends of the current user.
The message contains the following:
{malicious link} - shortened URL obtained from http://www.{BLOCKED}r.in/dropbox/up.php
Title: {Friend's Name} :Yaziklar olsun izlerken içim gitti ya.
The message displays the following image:

It chooses from the following for its message body:
- "Canli yayinda giyilecek elbisemi Allah askina bu! " + {random alphanumeric characters}
- " is gercekten iyice cigrindan cikti ne olacak boyle bilmiyorum!" + {random alphanumeric characters}
- "Bunlar da hakli hic bir yetenegi olmayan insanlar sonucta bunlar!" + {random alphanumeric characters}
- " Bunlari kontrol eden kurum RTUK! gor artik bunlar ve bi cozum uret!" + {random alphanumeric characters}
- "Valla bunlarda kisilik falan kalmamis kardesim" + {random alphanumeric characters}
- "Kardesim coluk cocugumuz var bunlar iyice bozdu!" + {random alphanumeric characters}
- "Birakin artik bu isleri bizler akillandik yemiyoruz bu numaralari!" + {random alphanumeric characters}
- "Ben izledim kendimden utandim. sizde bir bakin sunlara" + {random alphanumeric characters}
- "Yeter biktik beee! Biz boyle izlemek istemiyoruz!" + {random alphanumeric characters}
- "Yaa arkadaslar bunlari kontrol eden bir kurum yokmu! " + {random alphanumeric characters}
- "Reyting ugruna her gun neler goruyoruz vallahi yazik!" + {random alphanumeric characters}
- "Bizim orf adetlerimizle hic bagdasmayan seyler bunlar!" + {random alphanumeric characters}
- "D\xFCn\'den Beri Ugra\u015Ft\u0131g\u0131m tek \u015Eey bu Video \u0130zleyin."
- "Mutlaka \u0130zleyin g\xFCnlerdir ugra\u015F\u0131orum."
- "Videomu \u0130zleyen Herkeze Te\u015Fekk\xFCrler."
- "En Sevdi\u011Fim Arkada\u015Flar\u0131m :)"
- "Ben Bu Videoyu yapmak i\xE7in g\xFCnlerimi verdim kimse izlemior."
- "Yeni y\u0131l\u0131n\u0131z kutlu olsun arkada\u015Flar :) :D"
- "2013 y\u0131l\u0131nda arkada\u015Flar\u0131m ile ge\xE7irdi\u011Fim en g\xFCzel anlar"
- "Benim videomu birtek noal baba izlesin dilek diledim"
- "Simdide \u0130nanmayinda Goreyim :)"
- "Herkez Cesaret Edemez .."
- "\u0130ste Size Bahsettigim Sirrim :)"
- "Cok Utaniyorum Ama Birde Siz \u0130zleyin L\xFCtfen"
- "Ne Kadar Cilgin Bir \u0130nsanim Ben."
- "Nasilda Tatliyim Ama.."
- "Dostlarimin Destegi Olmasaydi Gidemezdim.."
- "Destek Veren Tum Dostlarimi Kutluyorum"
- "Yetenek Sizsiniz T\xFCrkiye\'ye Kat\u0131ld\u0131m. \u0130zlerseniz Sevinirim"
- "Bunu Yapacag\u0131m Aklima Gelmezdi :)"
- "Destek Veren T\xFCm Arkadaslarima Tesekk\xFCr Ederim"
- "Sonunda Bunuda Yaptim ya Helal Olsun Bana"
- "Kim Derdiki Televizyona Cikacag\u0131m ?"
- "Taniyanlar Ne Kadar Cilgin Oldugumu Bilir :)"
Once a user clicks the malicious link in the message, the browser will open the following webpage:
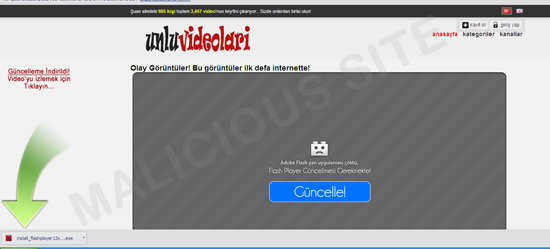
The webpage tricks users to download and install a fake Adobe Flash Player update saved as the following:
- {user-defined download directory}\install_flashplayer13x32_23msa_aaa.aih.exe - detected as TROJ_BLOCKER.J
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Close all opened browser windows
Step 3
Remove malware/grayware files dropped/downloaded by HTML_BLOCKER.K
- TROJ_BLOCKER.J
Step 4
Scan your computer with your Trend Micro product to delete files detected as HTML_BLOCKER.K. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


