TSPY_ZBOT.XXT
W32/Zbot.AZD (F-Prot); PWS:Win32/Zbot (Microsoft) ; Troj/Zbot-AGE (Sophos)
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Spyware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This spyware makes use of bogus emails purportedly from Facebook stating that the user's machine is sending spam messages and advises to run the attached tool to prevent the spamming.
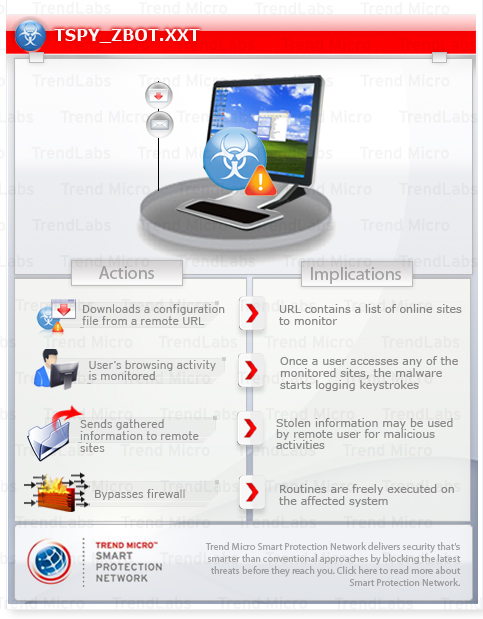
To get a one-glance comprehensive view of the behavior of this Spyware, refer to the Threat Diagram shown below.
This spyware inserts JavaScript (JS) code in the Web pages to retrieve user names, passwords, and security codes used in a two-factor authentication in order to transact from within the website.
This spyware arrives as an attachment to email messages spammed by other malware/grayware or malicious users. It may be dropped by other malware. It may be unknowingly downloaded by a user while visiting malicious websites.
It may be injected into processes running in memory.
It attempts to steal information, such as user names and passwords, used when logging into certain banking or finance-related websites.
TECHNICAL DETAILS
Arrival Details
This spyware arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
It may be dropped by other malware.
It may be unknowingly downloaded by a user while visiting malicious websites.
Installation
This spyware drops the following files:
- %Application Data%\{random1}\{random}.exe - copy of itself
- %Application Data%\{random2}\{random} - contains encrypted data
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Windows\Profiles\{user name}\Application Data on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Application Data on Windows NT, and C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, XP, and Server 2003.)
It injects itself into the following processes running in the affected system's memory:
- explorer.exe
- taskhost.exe
- taskeng.exe
- Dwm.exe
- wscntfy.exe
- ctfmon.exe
- rdpclip.exe
It creates the following folders:
- %Application Data%\{random1}
- %Application Data%\{random2}
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Windows\Profiles\{user name}\Application Data on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Application Data on Windows NT, and C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, XP, and Server 2003.)
It may be injected into processes running in memory.
Autostart Technique
This spyware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
{GUID of mount point of %Windows%} = %Application Data%\{random1}\{random}.exe
Other System Modifications
This spyware adds the following registry keys as part of its installation routine:
HKEY_CURRENT_USER\Software\Microsoft\
{random}
It creates the following registry entry(ies) to bypass Windows Firewall:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SharedAccess\Parameters\
FirewallPolicy\StandardProfile\AuthorizedApplications\
List
%WINDOWS%\EXPLORER.EXE = %WINDOWS%\EXPLORER.EXE:*:Enabled:Windows Explorer
Information Theft
This spyware monitors the Internet Explorer (IE) activities of the affected system, specifically the address bar or title bar. It recreates a legitimate website with a spoofed login page if a user visits banking sites with the following strings in the address bar or title bar:
- http*chase.com/js_tmp/*
- http://armskeyboard.com/java/
- http*bankofamerica.com/js_tmp/*
- http://armskeyboard.com/java/
- http*wellsfargo.com/js_tmp/*
- http://armskeyboard.com/java/
- https://sitekey.bankofamerica.com/sas/sas-docs/js/verifyImage.js
- https://sitekey.bankofamerica.com/sas/*
- http*chase.com*
- https://onlineeast#.bankofamerica.com/cgi-bin/ias/*/GotoWelcome
- https://onlineeast#.bankofamerica.com/cgi-bin/ias/*/GotoCustomerServiceMenu
- https://onlineeast#.bankofamerica.com/cgi-bin/ias/*/GotoWelcome
- https://sitekey.bankofamerica.com/sas/sas-docs/js/commonscript.js
- https://sitekey.bankofamerica.com/sas/maint.do
- https://onlineeast#.bankofamerica.com/cgi-bin/ias/*/CustomerServiceMenuEntryPoint?custAction=75
- https://*ameritrade.com*
- *wescom.org*
- http*countrywide.com*
- http*suntrust.com*
- *scottrade.com*
- *navyfcu.org*
- https://online.citibank.com/US/JPS/portal/Home.do
- https://www#.citizensbankonline.com/*/index-wait.jsp
- https://onlinebanking.nationalcity.com/OLB/secure/AccountList.aspx
- https://www.53.com/servlet/efsonline/index.html*
- https://*hb.growfinancial.org*
- http*chase.com/js_tmp/*
- http://armskeyboard.com/java/
- http*bankofamerica.com/js_tmp/*
- http://armskeyboard.com/java/
- http*wellsfargo.com/js_tmp/*
- http://armskeyboard.com/java/
- https://sitekey.bankofamerica.com/sas/sas-docs/js/verifyImage.js
- https://sitekey.bankofamerica.com/sas/*
- http*chase.com*
- https://onlineeast#.bankofamerica.com/cgi-bin/ias/*/GotoWelcome
- https://onlineeast#.bankofamerica.com/cgi-bin/ias/*/GotoCustomerServiceMenu
- https://onlineeast#.bankofamerica.com/cgi-bin/ias/*/GotoWelcome
- https://sitekey.bankofamerica.com/sas/sas-docs/js/commonscript.js
- https://sitekey.bankofamerica.com/sas/maint.do
- https://onlineeast#.bankofamerica.com/cgi-bin/ias/*/CustomerServiceMenuEntryPoint?custAction=75
- https://*ameritrade.com*
- *wescom.org*
- http*countrywide.com*
- http*suntrust.com*
- *scottrade.com*
- *navyfcu.org*
- https://online.citibank.com/US/JPS/portal/Home.do
- https://www#.citizensbankonline.com/*/index-wait.jsp
- https://onlinebanking.nationalcity.com/OLB/secure/AccountList.aspx
- https://www.53.com/servlet/efsonline/index.html*
- https://*hb.growfinancial.org*
It accesses the following site to download its configuration file:
- http://{BLOCKED}ngmad.com/images/smilies/joke.gif
It attempts to steal information from the following banks and/or other financial institutions:
- Ameritrade
- Bank of America
- Chase
- Citibank
- Citizens
- Fifth Third
- Myspace
- National City
- Navy Federal Credit Union
- Scottrade
- Suntrust
- Wells Fargo
- Wescom Credit Union
Stolen Information
This spyware sends the gathered information via HTTP POST to the following URL:
- http://www.{BLOCKED}al.com/coolstar/coolstar.php
Variant Information
This spyware has the following MD5 hashes:
- 69af20dbad4d042b1f682abdec824374
It has the following SHA1 hashes:
- 5895a5247d69d27c814c71d10f8e24307896e3c5
NOTES:
Other Details
Based on analysis of the codes, it has the following capabilities:
- Inserts JavaScript (JS) code in the Web pages to retrieve user names, passwords, and security codes used in a two-factor authentication in order to transact from within the website.
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Scan your computer with your Trend Micro product and note files detected as TSPY_ZBOT.XXT
Step 3
Restart in Safe Mode
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- {GUID of mount point of %Windows%} = %Application Data%\{random1}\{malware filename}.exe1
- {GUID of mount point of %Windows%} = %Application Data%\{random1}\{malware filename}.exe1
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\AuthorizedApplications\List
- %WINDOWS%\EXPLORER.EXE = %WINDOWS%\EXPLORER.EXE:*:Enabled:Windows Explorer
- %WINDOWS%\EXPLORER.EXE = %WINDOWS%\EXPLORER.EXE:*:Enabled:Windows Explorer
Step 5
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\
- {random}
- {random}
Step 6
Search and delete these folders
Step 7
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TSPY_ZBOT.XXT. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


