TSPY_ZBOT.YYKE
Windows 2000, Windows Server 2003, Windows XP (32-bit, 64-bit), Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Spyware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This ZBOT variant is related to a spam run in which its technique involves spammed messages containing .MSG attachment that contains a .ZIP file attached.
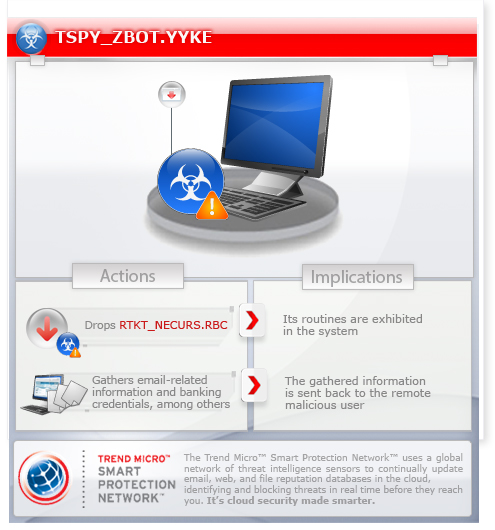
To get a one-glance comprehensive view of the behavior of this Spyware, refer to the Threat Diagram shown below.
This spyware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites. It may be downloaded by other malware/grayware from remote sites.
It steals certain information from the system and/or the user.
It deletes itself after execution.
TECHNICAL DETAILS
Arrival Details
This spyware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It may be downloaded by the following malware/grayware from remote sites:
- TROJ_UPATRE.YYKE
Installation
This spyware drops the following file(s)/component(s):
- %System%\drivers\{random filename 2}.sys - detected as RTKT_NECURS.RBC
(Note: %System% is the Windows system folder, which is usually C:\Windows\System32.)
It drops the following copies of itself into the affected system:
- %User Temp%\{random folder name}\{random filename 1}.exe
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local\Temp on Windows Vista and 7.)
It drops the following non-malicious file:
- %AppDataLocal%\{random filename 3}.{random extension}
(Note: %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local on Windows Vista and 7.)
It creates the following folders:
- %User Temp%\{random folder name}
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local\Temp on Windows Vista and 7.)
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- Local\{GUID}
- Global\{GUID}
It injects codes into the following process(es):
- explorer.exe
Autostart Technique
This spyware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
{random filename 1} = "%User Temp%\{random folder name}\{random filename 1}.exe"
It registers its dropped component as a system service to ensure its automatic execution at every system startup. It does this by creating the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{random filename 2}
DisplayName = "{random filename 1}.exe"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{random filename 2}
ErrorControl = "0"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{random filename 2}
Group = "Boot Bus Extender"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{random filename 2}
ImagePath = "%System%\drivers\{random filename 2}.sys"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{random filename 2}
Start = "0"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{random filename 2}
Tag = "1"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{random filename 2}
Type = "1"
It registers its dropped component as a system service to ensure its automatic execution at every system startup. It does this by creating the following registry keys:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{random filename 2}
Other System Modifications
This spyware adds the following registry keys:
HKEY_CURRENT_USER\Software\Microsoft\
{random}
It creates the following registry entry(ies) to bypass Windows Firewall:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SharedAccess\Parameters\
FirewallPolicy\StandardProfile\AuthorizedApplications\
List
%Windows%\explorer.exe = "%Windows%\explorer.exe:*:Enabled:Windows Explorer"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SharedAccess\Parameters\
FirewallPolicy\StandardProfile\GloballyOpenPorts\
List
{random port 1}:UDP = "{random port 1}:UDP:*:Enabled:UDP {random port 1}"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SharedAccess\Parameters\
FirewallPolicy\StandardProfile\GloballyOpenPorts\
List
{random port 2}:TCP = "{random port 2}:TCP:*:Enabled:TCP {random port 2}"
Download Routine
This spyware connects to the following URL(s) to download its configuration file:
- http://{random generated URL}
Information Theft
This spyware steals the following information:
- Data on cookie files (URLs)
- Email-related information such as account names, email addresses, passwords, server data, and server port
- Email information stored in the user’s Windows Address Book (WAB) file
- Online banking credentials
- Personal digital cerificates
Other Details
This spyware deletes itself after execution.
NOTES:
This spyware attempts to download its configuration file by connecting to randomly generated URL.
The configuration file may contain URLs where it downloads an updated copy of itself and where it sends its gathered information.
It may also contain URLs of its target online banking and finance-related sites from where it steals the information.
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 4
Restart in Safe Mode
Step 5
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft
- {random}
- {random}
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services
- {random filename 2}
- {random filename 2}
Step 6
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- {random filename 1} = "%User Temp%\{random folder name}\{random filename 1}.exe"
- {random filename 1} = "%User Temp%\{random folder name}\{random filename 1}.exe"
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\AuthorizedApplications\List
- %Windows%\explorer.exe = "%Windows%\explorer.exe:*:Enabled:Windows Explorer"
- %Windows%\explorer.exe = "%Windows%\explorer.exe:*:Enabled:Windows Explorer"
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\GloballyOpenPorts\List
- {random port 1}:UDP = "{random port 1}:UDP:*:Enabled:UDP {random port 1}"
- {random port 1}:UDP = "{random port 1}:UDP:*:Enabled:UDP {random port 1}"
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\GloballyOpenPorts\List
- {random port 2}:TCP = "{random port 2}:TCP:*:Enabled:TCP {random port 2}"
- {random port 2}:TCP = "{random port 2}:TCP:*:Enabled:TCP {random port 2}"
Step 7
Search and delete this folder
- %User Temp%\{random folder name}
Step 8
Search and delete these files
- %AppDataLocal%\{random filename 3}.{random extension}
Step 9
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TSPY_ZBOT.YYKE. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 10
The following created registry key(s) cannot be identified by the user since there are no reference values in the created key. The only way it can be identified is by comparing the present keys with a backup of the system registry. Note that the said key(s) do not have to be deleted since it won't be harmful to the system:
- HKEY_CURRENT_USER\Software\Microsoft\{random}
Did this description help? Tell us how we did.


