OSX_SLORDU.A
OSX.Slordu (Symantec), Backdoor.OSX.Belfibod.a (Kaspersky), OSX/Slordu-A (Sophos), OSX/Stealer.B (AVG), OSX/XSLCmd.A (ESET)
Mac OS X


Threat Type: Backdoor
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This malware variant is designed to compromise Apple OS X systems. It drops files for its keylogging routine in order to steal information from the affected system.
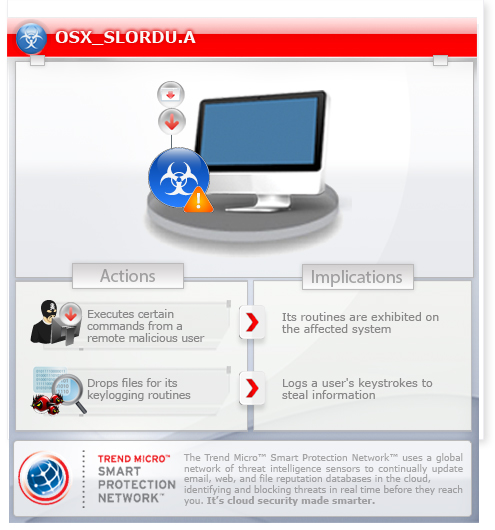
To get a one-glance comprehensive view of the behavior of this Backdoor, refer to the Threat Diagram shown below.
This backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It executes commands from a remote malicious user, effectively compromising the affected system.
It logs a user's keystrokes to steal information.
It deletes the initially executed copy of itself.
TECHNICAL DETAILS
Arrival Details
This backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This backdoor drops the following copies of itself into the affected system:
- /Library/Logs/clipboardd
- $HOME/Library/LaunchAgents/clipboardd
It drops the following file(s)/component(s):
- $HOME/.fontset/pxupdate.ini
- $HOME/.fontset/chkdiska.dat
- $HOME/.fontset/chkdiskc.dat
It creates the following folders:
- $HOME/.fontset
- $HOME/Library/Logs/BackupData
It terminates the execution of the copy it initially executed and executes the copy it drops instead.
Autostart Technique
This backdoor drops the following files:
- /Library/LaunchAgents/com.apple.service.clipboardd.plist
- $HOME/Library/LaunchAgents/com.apple.service.clipboardd.plist
Backdoor Routine
This backdoor executes the following commands from a remote malicious user:
- Upload a file to the C&C server
- Download a file
- Start a remote shell
- Enumerate the contents of a directory
- Delete a file
- Uninstall itself
- Capture screenshot
- Get the following information:
- OS name
- OS version
- Host name
- User name
- Home directory
- Contents of the /Applications folder
- Update configuration file
It connects to the following URL(s) to send and receive commands from a remote malicious user:
- {BLOCKED}.{BLOCKED}.110.38:8000
Dropping Routine
This backdoor drops the following file(s), which it uses for its keylogging routine:
- $HOME/Library/Logs/BackupData/{year}{month}{day}_{hour}{minute}_{second}_keys.log
Information Theft
This backdoor logs a user's keystrokes to steal information.
Other Details
This backdoor deletes the initially executed copy of itself
SOLUTION
NOTES:
Step 1
Terminate the malware process. To terminate the malware process, open a Terminal window and perform the following:
Enter the following command:
- ps -A
In the Terminal window, search for a line similar to the following:
- {number} ?? {time} /Library/Logs/clipboardd
- {number} ?? {time} $HOME/Library/LaunchAgents/clipboardd
Take note of the number since the number is the malware process ID (PID). For each malware process ID, enter the following command:
- kill {malware PID}
Step 2
Delete the Malware Directories. To delete the malware directories, open a Terminal window and type the following commands:
- rm -R $HOME/.fontset
- rm -R $HOME/Library/Logs/BackupData
Step 3
Deleting the Malware Files. To delete the malware files, open a Terminal window and type the following commands:
- rm /Library/LaunchAgents/com.apple.service.clipboardd.plist
- rm $HOME/Library/LaunchAgents/com.apple.service.clipboardd.plist
Step 4
Scan your computer with your Trend Micro product to delete files detected as OSX_SLORDU.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
- To open a Terminal window, double-click Applications > Utilities > Terminal in Finder.
- To close the Terminal application, press ⌘ (Command) + Q.
Note that not all files and folders are installed on your computer during this malware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files or folders, please proceed to the next step.
Did this description help? Tell us how we did.


