TrojanSpy.Win32.GRANDOREIRO.MLMB
Windows


Threat Type: Trojan Spy
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Trojan Spy arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Arrival Details
This Trojan Spy arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan Spy adds the following mutexes to ensure that only one of its copies runs at any one time:
- FA1EA8E940963B9A3B51F33824D877A8
It terminates itself if it finds the following processes in the affected system's memory:
- ResourceHacker.exe
- JoeTrace.exe
- PCHunter32.exe
- PCHunter64.exe
- ProcessHacker.exe
- procexp.exe
- procexp64.exe
- Wireshark.exe
- filemon.exe
- procmon.exe
- regmon.exe
Information Theft
This Trojan Spy gathers the following data:
- System Information:
- Computername
- Username
- Operating System Version
- IP Address
- Installed Anti Virus Products
- Country
- City
- Region
- Zip Code
- Language
- Geolocation
- Time zone information
- Installed Programs:
- Mail Clients
- Microsoft Outlook
- Software\Clients\Mail
- Anti-Malware Program
- C:\Program Files\Trusteer
- C:\Program Files (x86)\Trusteer
- Banking
- C:\Program Files\Diebold\
- C:\Program Files (x86)\Diebold
- C:\Program Files\Topaz OFD
- C:\Program Files (x86)\Topaz OFD
- Crypto Wallets
- c:\Program Files\Bitcoin
- c:\Program Files (x86)\OPOLODesk
- c:\Program Files\OPOLODesk
- c:\Program Files (x86)\BitBox
- c:\Program Files\BitBox
- c:\Program Files (x86)\Coinomi
- c:\Program Files\Coinomi
- c:\Program Files (x86)\Electrum
- c:\Program Files\Electrum
- c:\Program Files (x86)\Binance
- c:\Program Files\Binance
- Connects to the following URL to retrieve affected system's IP Address
- http[:]/ip-api[.]com/json
Other Details
This Trojan Spy does the following:
- It terminates itself if any of the following are satisfied:
- If the execution is occurring in a Virtual Environment
- If it is executed from the following directory:
- D:\script
- D:\programming
- If the username matches any of the following:
- JOHN-PC
- DESTOP2457
- difusor
- Win-StephyPC3
- WIN-VUA6POUV5U
- WORK
- *~+
- Administrator
- It retrieves the hostname from the following URL
- {BLOCKED}m-az.net However as of this writing, the said URL is inaccessible.
- It requires a successful connection to the C&C server to retrieve the URL responsible for downloading the payload.
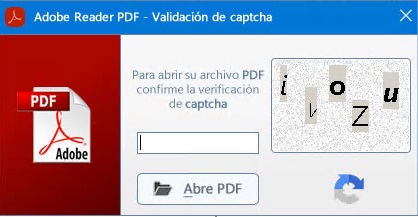
- Completing the captcha is required to execute the malware's routine.
SOLUTION
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
- TROJ.Win32.TRX.XXPE50FFF074
Step 2
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 3
Scan your computer with your Trend Micro product to delete files detected as TrojanSpy.Win32.GRANDOREIRO.MLMB. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.



