TROJ_CARBERP.A
Windows 2000, XP, Server 2003, Vista, 7


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
Trend Micro has flagged this malware as noteworthy due to the increased potential for damage, propagation, or both, that it possesses. Specifically, it uses techniques that does not need administrator privileges to exhibit its routines. Because of this operating systems, such as Windows Vista and Windows 7, will not be able to detect the file as suspicious. This Trojan may also be a new breed of malware targeting banking and/or financial sites.
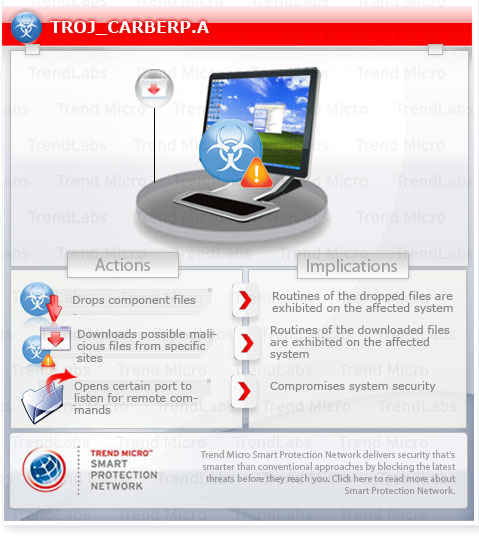
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This Trojan may be downloaded by other malware/grayware/spyware from remote sites. It may be unknowingly downloaded by a user while visiting malicious websites.
However, as of this writing, the said sites are inaccessible.
It also has rootkit capabilities, which enables it to hide its processes and files from the user.
TECHNICAL DETAILS
51,712 bytes
PE
Yes
13 Oct 2010
Compromises system security, Downloads files, Hides files, processes, and registry entries
Arrival Details
This Trojan may be downloaded by other malware/grayware/spyware from remote sites.
It may be unknowingly downloaded by a user while visiting malicious websites.
Installation
This Trojan drops the following component file(s):
- %User Profile%\usernt.dat - configuration file
- %User Temp%\{random characters}.tmp - random component files, such as copy of legitimate Library files
(Note: %User Profile% is the current user's profile folder, which is usually C:\Windows\Profiles\{user name} on Windows 98 and ME, C:\WINNT\Profiles\{user name} on Windows NT, and C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003.. %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003.)
It injects threads into the following normal process(es):
- Explorer.exe
Autostart Technique
This Trojan drops the following file(s) in the Windows User Startup folder to enable its automatic execution at every system startup:
- syscron.exe
Backdoor Routine
This Trojan opens the following port(s) where it listens for remote commands:
- port 80
However, as of this writing, the said sites are inaccessible.
Rootkit Capabilities
This Trojan also has rootkit capabilities, which enables it to hide its processes and files from the user.
Other Details
This Trojan does the following:
- Hooks the following NTDLL.DLL APIs to hide itself and its component files:
- NtQueryDirectoryFile
- NtResume Thread
- Hooks the following WININET.DLL APIs to monitor the Internet browsing activities in the affected system:
- InternetCloseHandle
- HttpSendRequestA
- InternetReadFile
- HttpSendRequestExW
- InternetQueryDataAvailable
- InternetReadFileExW
- InternetReadFileExA
- HttpSendRequestW
- HttpSendRequestExA
- Connects to the following URLs to download configuration files and send and receive commands from its C&C server:
- http://{BLOCKED}.80.146/cfg/MYWITCH:
- http://{BLOCKED}.80.146/grabber.pcp
- http://{BLOCKED}.80.146/task.php?id=MYWITCH{random characters}&task=
- http://{BLOCKED}.60.146/first.php:uid=MYWITCH{unique ID}&os={OS version}&plist={list of running processes}
SOLUTION
8.900
7.538.04
13 Oct 2010
7.539.00
14 Oct 2010
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Restart in Safe Mode
Step 3
Search and delete these files
- %User Profile%\usernt.dat
- %User Startup%syscron.exe
Step 4
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TROJ_CARBERP.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

