The ransomware attack on the major fuel supply company Colonial Pipeline recently made headlines. The incident has been attributed to the DarkSide threat actor, once again thrusting the group’s name into the spotlight. With this, it would not be surprising to find threat actors taking advantage of this incident for their own socially-engineered campaigns.
Several companies in the energy and food industry have recently received threatening emails supposedly from DarkSide. In this email, the threat actor claims that they have succesfully hacked the target’s network and gained access to sensitive information, which will be disclosed publicly if a ransom of 100 bitcoins (BTC) is not paid.
However, the content used on the emails has led us to believe that they did not come from the said threat group, but from an opportunistic low-level attacker trying to profit off the current situation around DarkSide ransomware activities.
The content of the emails used in the campaign
The email campaign started on June 4, hitting a few targets every day. Emails with threatening content were sent to selected companies’ generic email addresses. Here is a sample of the email text:
The Bitcoin wallet at the end of the email is always the same for every target. As of writing, the said wallets have not received or sent any Bitcoin payment. No actual attack has been traced back to the emails, and no new targets have been spotted.
More than just emails
In addition to sending targeted emails to companies, we learned that the same attacker has also filled contact forms on several companies’ websites.
The content sent through the web forms has been the same as the one in the emails. In one case, we were able to get the sender’s IP address, 205[.]185[.]127[.]35, which happens to be a Tor network exit node.
Energy and food industries as attractive targets
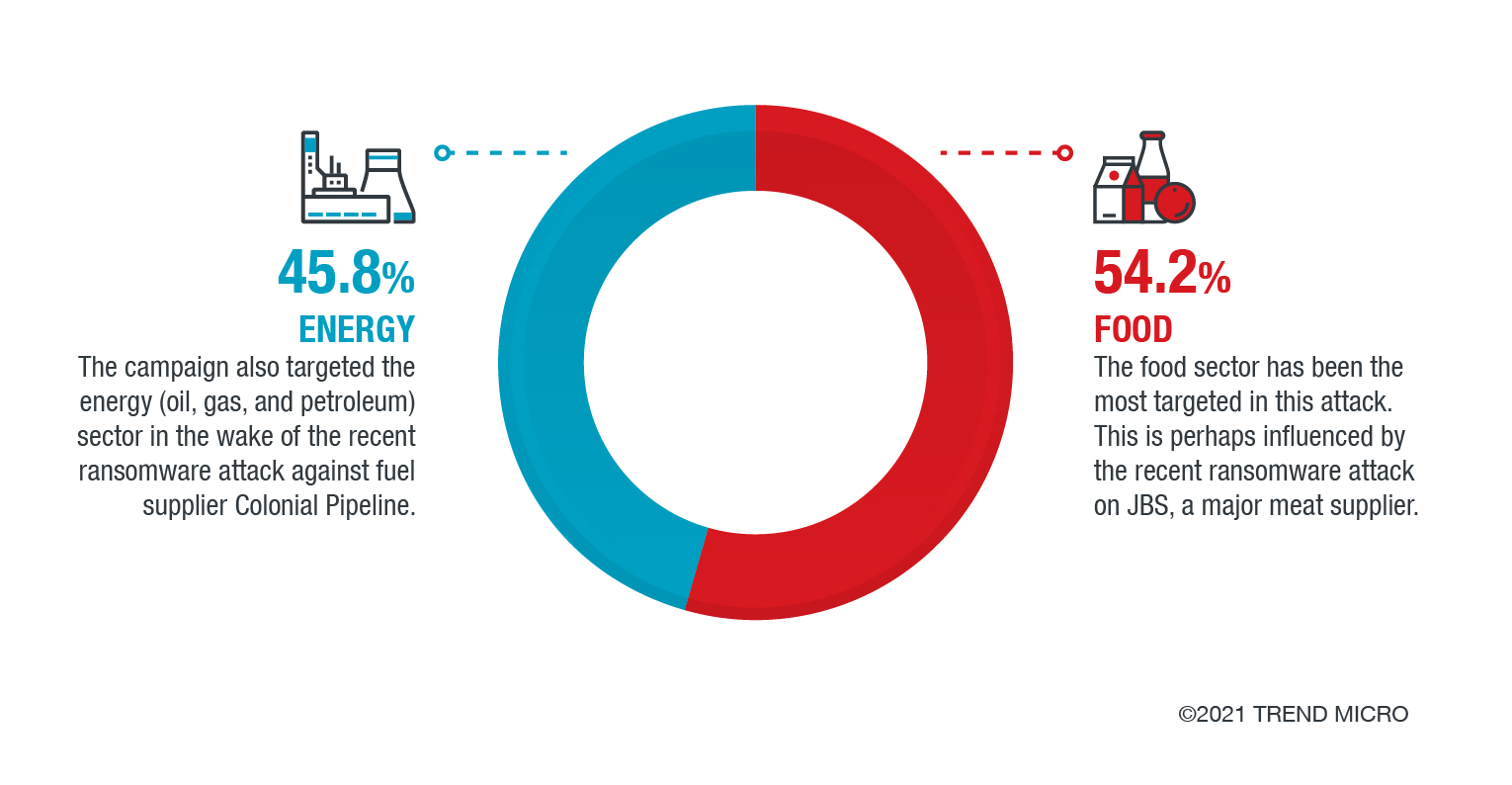
Based on the telemetry data, it seems the threat actor is only interested in the energy (oil, gas, and/or petroleum) and the food industries; in fact, all of their targets belong to these sectors.
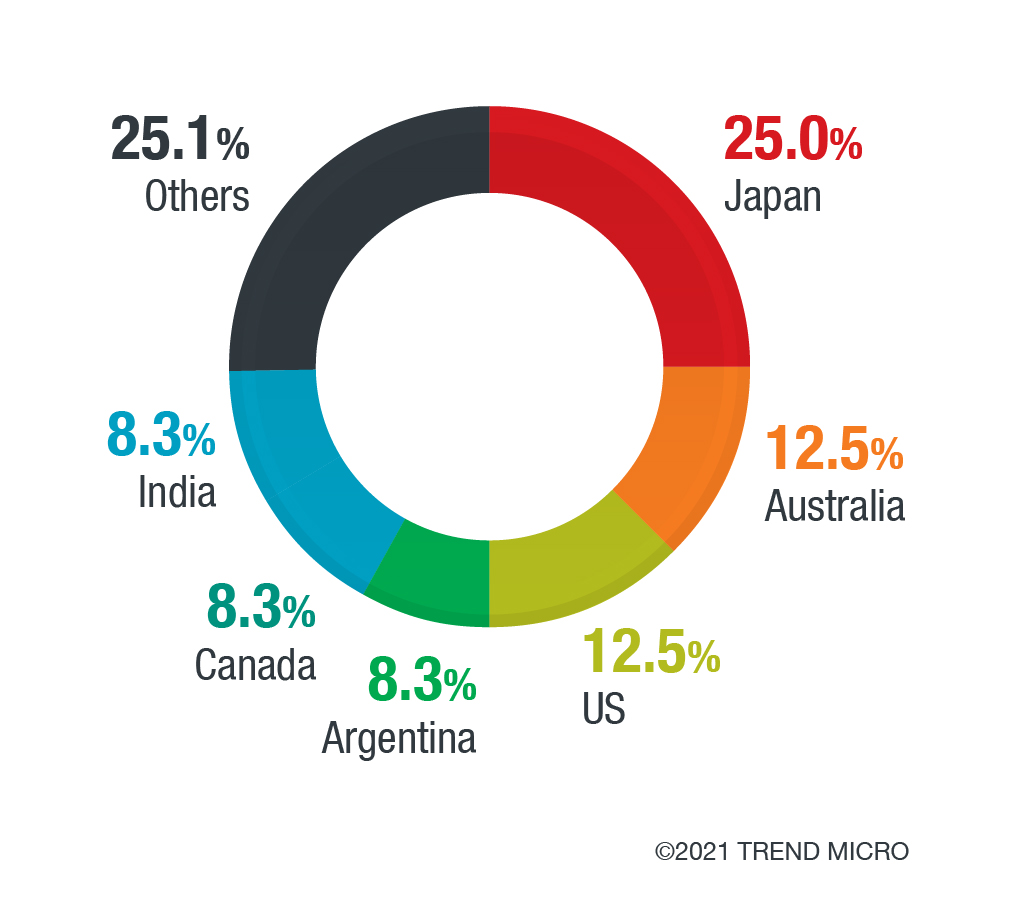
The campaign affected Japan the most, followed by several other countries: Australia, the US, Argentina, Canada, India. The rest of the affected countries include China, Colombia, Mexico, Netherlands, Thailand, and the UK.
Signs that this is not a real DarkSide campaign
The behavior behind this fraud campaign is very different from what DarkSide exhibited in its previous campaigns. DarkSide has always been able to show proof that they obtained stolen sensitive data. They also lead their targets to a website hosted on the Tor network. However, in this campaign, the email does not mention anything about proving that they have indeed obtained confidential or sensitive information.
Also, like most modern ransomware attacks, DarkSide launched the ransomware to paralyze their target’s operations before demanding ransom. Here, there is no encryption of any content on the target network; the actors just send a threat and a ransom demand based on the assertion that they reportedly have the data.
Perhaps the most telling: The actors behind these threats mentioned JBS as the victim of one of their recent publicized attack; the JBS attack was not attributed to DarkSide, but to REvil (aka Sodinokibi).
All in all, this campaign looks amateurish compared to known previous DarkSide activities. The amount requested from every target, 100 BTC, is worth approximately 4 million US dollars. We believe that most companies will not be urged to pay that amount without being shown any real evidence that the network has been compromised and sensitive data is about to leak in public.
Why are they targeting essential sectors?
While the rest of the campaign shows clumsy techniques, it is worth noting that the attacker deliberately selected companies in specific industries for a reason. The decision to handpick these targets are probably influenced by the recent ransomware attacks on JBS and Colonial Pipeline, which belong to the same industries.
Besides being affected in these recent attacks, these industries have also been consistently among the most targeted in the past. In 2020, our cybersecurity roundup report found the food and beverage and the oil and gas industries among the top ten industries most targeted by ransomware.
One of the causes for this might be because these sectors are expected to provide essential goods and/or services on the daily basis. The longer the attack remains unthwarted and the companies’ operations subsequently interrupted, the more the affected organization losses profit and reputation. The shutdown of these services might also cause public uproar and panic, especially when it potentially affects a large number of people.
In the aftermath, an attack’s impact could raise fears about food and/or energy security, triggering panic buying as the public worries about possible spikes in prices that could be caused by the attack.
This is one of the reasons why attackers, real and fake alike, would choose to launch campaigns on essential supply providers: their targets are aware of the far-reaching immediate effects an attack could have, affecting not just the company itself, but a slew of consumers as well. Considering this, the targets would be more likely to cave into the ransom demands. In the campaign we spotted, fortunately no one actually paid, probably due to the questionable details in the email. However, this does not remove the possibility that an attacker with more believable methods could successfully ensnare targets.
In the wake of the apprehension brought about by recent ransomware attacks that affected major companies, organizations should always verify the validity of the threats before taking any action. Better yet, organizations could nip these threats from the bud by using security solutions that block spam and other email-based threats.
Indicators of Compromise
- darkside@99email[.]xyz
- darkside@solpatu[.]space
IP Address
- 205[.]185[.]127[.]35 (Tor exit node)

