BREX_KILIM.LL
Trojan:JS/Kilim.O (Microsoft)
Windows


Threat Type: Others
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
Downloaded from the Internet
This malware is a malicious plugin for Chrome browsers. It runs a code when users browse Facebook, enabling the plugin to control navigation.
To get a one-glance comprehensive view of the behavior of this Others, refer to the Threat Diagram shown below.
This Others may be unknowingly downloaded by a user while visiting malicious websites. It may be manually installed by a user.
TECHNICAL DETAILS
65,673 bytes
JS
Yes
21 Aug 2014
Arrival Details
This Others may be unknowingly downloaded by a user while visiting malicious websites.
It may be manually installed by a user.
NOTES:
The malicious Google Chrome plugin is composed of the following files:
- manifest.json
background.js
The file manifest.json will direct Google Chrome where to load background.js.
It prevents the removal of the malicious plugin. If users open a tab to chrome://extensions to check for malicious browser extensions, the plugin will close this tab immediately.
It removes the security option from HTTP response header. This security option is typically used to avoid cross-site scripting attacks. The plugin removes this as it will will inject script that does not belong to Facebook.
It runs a JavaScript code when users visit Facebook. When users go on Facebook, the plugin will run a JavaScript code into the tab where the site is open. Doing so will allow the cybercriminals to control the users’ accounts; users will unwillingly follow, "like", or subscribe to Facebook accounts as dictated by the cybercriminals behind this attack. These commands are performed automatically by the included JavaScript code. The affected users’ friends will also see these actions on their feed and may possibly inadvertently install the plugin as well.
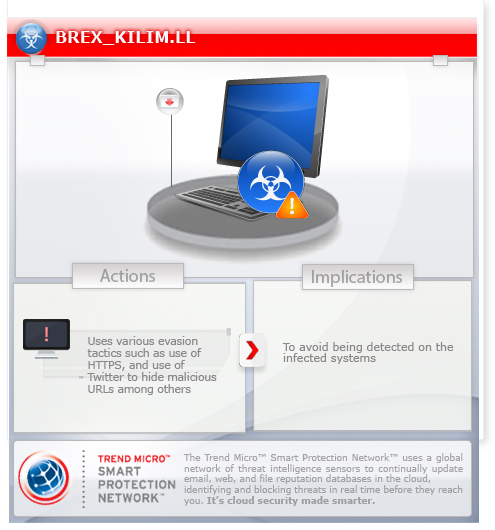
Evasion Tactics
The malicious extensions employ the following evasion methods:
- Use of malicious multi-script files that work together. The malicious behavior is separated into multiple files. If each script file is analyzed independently, the overall malicious behavior may not be spotted and the files may be (mistakenly) thought to be clean
- Encoded JavaScript content to avoid easy analysis and detection
- Use of HTTPs and a known, good domain to host malicious JavaScript
- Use of Twitter to hide malicious URLs.A malicious plugin runs a JavaScript into the user’s browser tab and downloads content from a Twitter user’s profile. The cybercriminals use the affected Twitter user’s profile content to hide the malicious URL that the plugin connects to. Once cybercriminals change the profile content, they can change the behavior of the malicious plugin.
- Use of fake file extensions to mislead analysis
SOLUTION
9.700
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as BREX_KILIM.LL. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.

