Spam Attack Leverages Boston Marathon Bombing
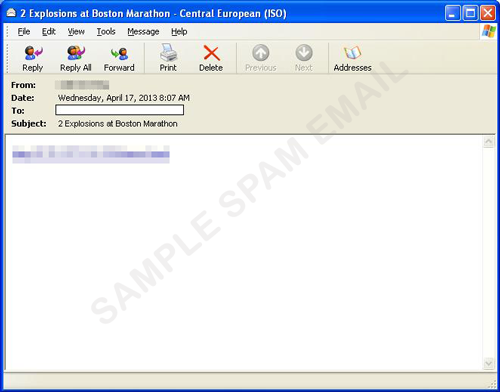
The April 2013 Boston Marathon bombing was a tragedy that shook the world, but for cybercriminals, it's only another lure for their malicious activities. We recently discovered a spam campaign that takes advantage of the media buzz and social outrage about the event. The spammed mail sports the subject '2 explosions at Boston Marathon' sports a single hyperlink in its body. Should the recipient click the link supplied in the spammed email, it will redirect into a page featuring embedded videos of the event. During the redirection, it will connect to a malicious URL to automatically download malicious files and then execute them.
The downloaded malware hides path directories on any USB drives attached to the affected system and replaces them with an .LNK file. This file then executes the downloaded malware whenever the user tries to open a particular folder or path.
Users are once again reminded to always be vigilant and to anticipate threats like these whenever news events break out. The spammed mails and the malware payloads are already detected and blocked by Trend Micro.
Further analysis of the first spam campaign mentioned in this blog post has indicated that while it uses exploits, it does not specifically use the Blackhole Exploit Kit.
- ENGINE:7.0
- PATTERN:9804
