Ransomware Recap: Notable New Ransomware and the Aftershocks of Major Outbreaks
 This week the conversation is still about the two ransomware responsible for the widespread chaos that affected organizations across the globe—WannaCry and Petya. WannaCry was detected in early May, but there were recent outbreaks in countries across Asia and in Australia. Meanwhile, the repercussions of Petya are still being felt. Experts are dissecting the details and trying to find the motivation behind this attack, as well as who is still vulnerable.
This week the conversation is still about the two ransomware responsible for the widespread chaos that affected organizations across the globe—WannaCry and Petya. WannaCry was detected in early May, but there were recent outbreaks in countries across Asia and in Australia. Meanwhile, the repercussions of Petya are still being felt. Experts are dissecting the details and trying to find the motivation behind this attack, as well as who is still vulnerable.
Other notable ransomware of the week
The downloader hashes for Karo ransomware (detected by Trend Micro as RANSOM_KARO.A) were actually included in a Github repository for Petya-related IOCs, but Karo is a unique threat on its own. It is a MSIL-compiled (which needs a .NET framework in order to work) and obfuscated file that typically arrives in a macro-enabled document that uses a Powershell downloader code. This isn’t the first ransomware to use this technique, and we’ve previously discussed why more and more attackers are abusing Powershell.
Using the de4dot tool, which is an open source .NET deobfuscator and unpacker, we also found that it has anti-sandbox features:
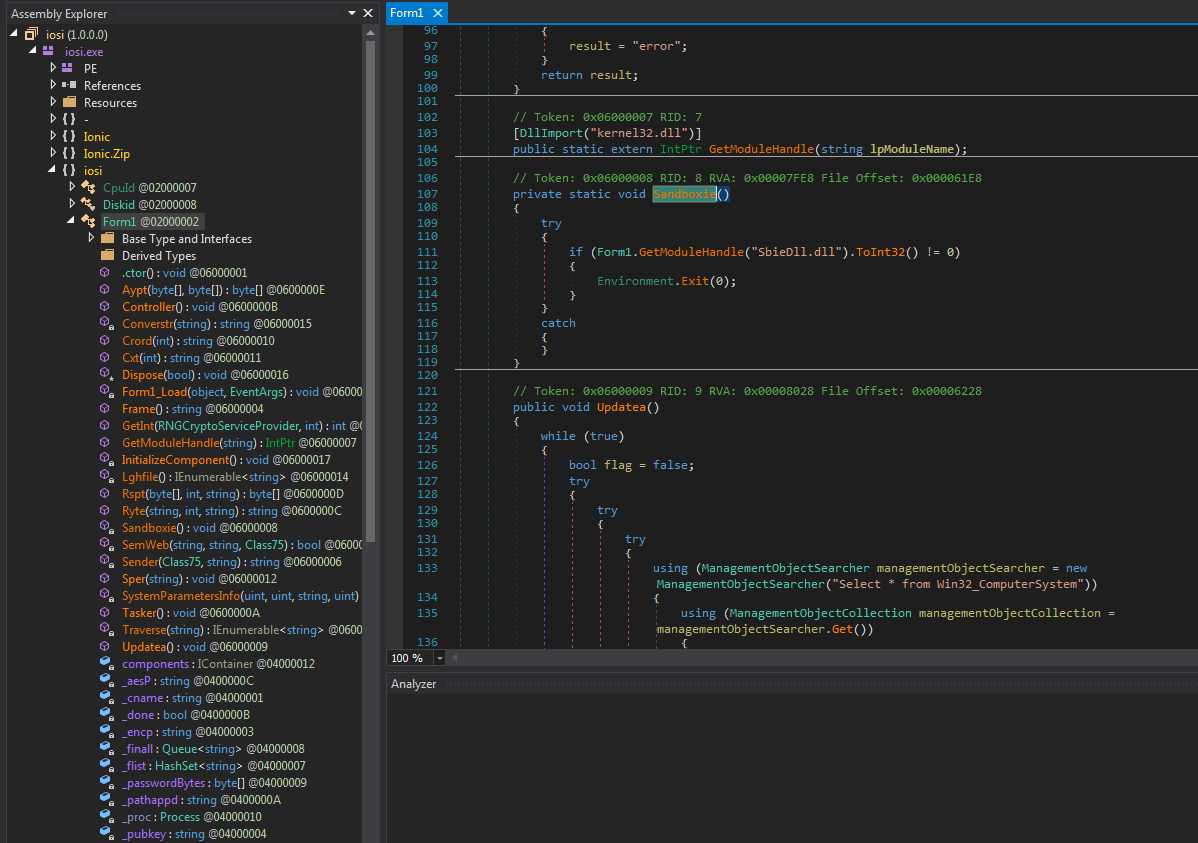
Figure 1. Snippet of code from Karo
There are a few other notable ransomware to come out over the past week. Recently the infamous crypto-ransomware SamSam (detected as RANSOM_SAMAS) has been more active. Reports show that it now demands a substantial ransom from its victims, as much as 12 BTC—roughly US$31,600—to decrypt multiple devices.
ViACrypt (detected by Trend Micro as RANSOM_ VIACRYPT) is a newer, potentially harmful ransomware that uses RSA-1024 algorithm to encrypt files and has a Latvian ransom note. Meanwhile, a Hidden Tear variant (detected by Trend Micro as RANSOM_HIDDENTEARBATTLEFIELD) is masquerading as an installer for the first-person shooter game Battlefield to trick gamers into installing it.
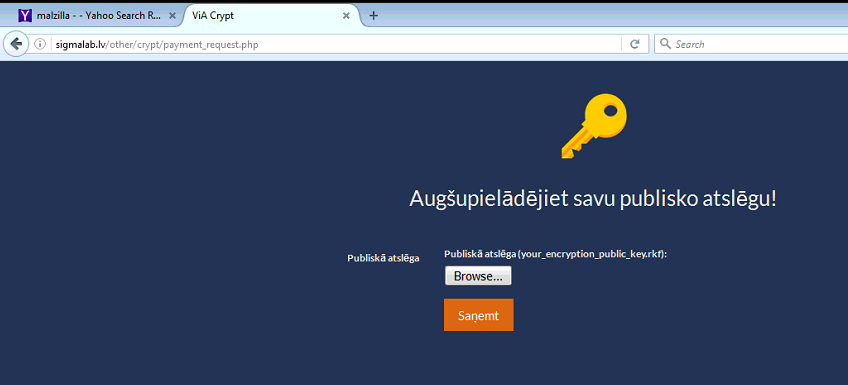
Figure 2. ViACrypt ransom note
The ransomware Gank (detected by Trend Micro as RANSOM_GANK), which appends the extension .ganklocked onto files it encrypts, is also notable. There is also the recently discovered ABCScreenlocker (detected by Trend Micro as RANSOM_ABCSCREENLOCKER), which simply locks the user out of his device.
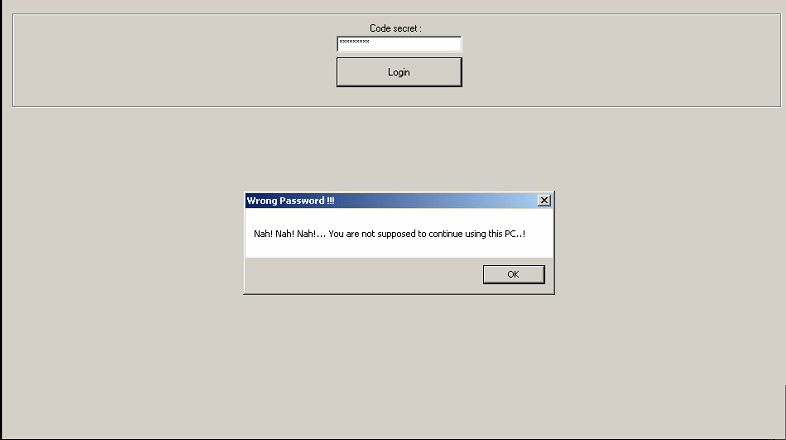
Figure 3. ABCScreenlocker image
At the heels of these outbreaks, Microsoft released its contribution to protecting users from ransomware. Their recent Windows 10 Insider Preview Build introduces a new controlled folder access feature that “monitors the changes that apps make to files in certain protected folders. If an app attempts to make a change to these files, and the app is blacklisted by the feature, you’ll get a notification about the attempt.” Users can add certain folders that they want to protect, and also allow specific apps through the feature.
Enterprises and all users should use best practices and be proactive in protecting systems against ransomware.
Ransomware Solutions
Enterprises can benefit from a multi-layered, step-by-step approach in order to best mitigate the risks brought by these threats. Email and web gateway solutions such as Trend Micro™ Deep Discovery™ Email Inspector and InterScan™ Web Security prevents ransomware from ever reaching end users. At the endpoint level, Trend Micro Smart Protection Suites deliver several capabilities like high-fidelity machine learning, behavior monitoring and application control, and vulnerability shielding that minimizes the impact of this threat. Trend Micro Deep Discovery Inspector detects and blocks ransomware on networks, while Trend Micro Deep Security™ stops ransomware from reaching enterprise servers—whether physical, virtual, or in the cloud.
For small businesses, Trend Micro Worry-Free Services Advanced offers cloud-based email gateway security through Hosted Email Security. Its endpoint protection also delivers several capabilities such as behavior monitoring and real-time web reputation in order detect and block ransomware.
For home users, Trend Micro Security 10 provides strong protection against ransomware by blocking malicious websites, emails, and files associated with this threat.
Users can likewise take advantage of our free tools such as the Trend Micro Lock Screen Ransomware Tool, which is designed to detect and remove screen-locker ransomware; as well as Trend Micro Crypto-Ransomware File Decryptor Tool, which can decrypt certain variants of crypto-ransomware without paying the ransom or the use of the decryption key.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Ransomware Spotlight: Agenda
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™
- Forecasting Future Outbreaks: A Behavioral and Predictive Approach to Proactive Cyber Risk Management
- Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One