Ransom.Linux.AGENDA.YXDKOT
Ransom:Linux/Qilin.A!MTB (MICROSOFT)
Linux


Threat Type: Ransomware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
Downloaded from the Internet, Dropped by other malware
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It encrypts files with specific file extensions. It encrypts files found in specific folders. It drops files as ransom note. It avoids encrypting files with the following file extensions.
TECHNICAL DETAILS
1,386,992 bytes
ELF
No
15 Nov 2023
Encrypts files
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware adds the following processes:
- If the system has sufficient memory resources:
- for I in $(esxcli storage filesystem list |grep 'VMFS-5' |awk '{print $1}'); do vmkfstools -c 10M -d eagerzeroedthick $I/eztDisk; vmkfstools -U $I/eztDisk; done
- for I in $(esxcli storage filesystem list |grep 'VMFS-6' |awk '{print $1}'); do vmkfstools -c 10M -d eagerzeroedthick $I/eztDisk; vmkfstools -U $I/eztDisk; done
- Otherwise:
- for I in $(esxcli storage filesystem list |grep 'VMFS-5' |awk '{print $1}'); do vmkfstools -c 10M -d eagerzeroedthick $I/eztDisk > /dev/null; vmkfstools -U $I/eztDisk > /dev/null; done
- for I in $(esxcli storage filesystem list |grep 'VMFS-6' |awk '{print $1}'); do vmkfstools -c 10M -d eagerzeroedthick $I/eztDisk > /dev/null; vmkfstools -U $I/eztDisk > /dev/null; done"
- esxcfg-advcfg -s 32768 /BufferCache/MaxCapacity
- esxcfg-advcfg -s 20000 /BufferCache/FlushInterval
- esxcli vm process list
- esxcli vm process kill -t force -w %llu
- vim-cmd vmsvc/getallvms
- vim-cmd vmsvc/snapshot.removeall %llu > /dev/null 2>&1
Other Details
This Ransomware does the following:
- It avoids terminating the following processes:
- kvm
- qemu
- xen
- It is capable of modifying the motd content.
It accepts the following parameters:
- -d | --debug → Enable debug mode (logging level set to DEBUG, disables backgrounding)
- --dry-run → Perform scan for files to be processed. Does not modify them.
- -h | --help → Display list of commands
- -l | --log-level {number} → Set logging level. Values are from 0 for FATAL up to 5 for DEBUG
- --no-df → Ignore configured white-/black- lists of directories
- --no-ef → Ignore configured white-/black- lists of extensions
- --no-ff → Ignore configured white-/black- lists of files
- --no-proc-kill → Disables process kill
- -R | --no-rename → Disables rename of completed files
- --no-snap-rm → Disables snapshot deletion
- --no-vm-kill → Disables VM kill
- -p | --path {string} → Specifies top-level directory for files search
- --password {string} → Password for startup
- -r | --rename → Enables rename of completed files (default)
- -t | --timer {number} → Enabled timed delay before encryption (seconds)
- -w | --whitelist → Use whitelists for inclusion instead of blacklists for exclusion (default behavior)
- -y | --yes → Assume answer 'yes' on all questions (script mode)
Ransomware Routine
This Ransomware encrypts files with the following extensions:
- 3ds
- 3g2
- 3gp
- 7z
- aac
- abw
- ac3
- accdb
- ai
- aif
- aiff
- amr
- apk
- app
- asf
- asx
- atom
- avi
- bak
- bat
- bmp
- bup
- bz2
- cab
- cbr
- cbz
- cda
- cdr
- chm
- class
- cmd
- conf
- cow
- cpp
- cr2
- crdownload
- cs
- csv
- cue
- cur
- dat
- db
- dbf
- dds
- deb
- der
- desktop
- dmg
- dng
- doc
- docm
- dot
- dotm
- dotx
- dpx
- drv
- dtd
- dvi
- dwg
- dxf
- eml
- eps
- epub
- f4v
- fnt
- fon
- gam
- ged
- gif
- gpx
- gz
- h264
- hdr
- hpp
- hqx
- htm
- html
- ibooks
- ico
- ics
- iff
- image
- img
- indd
- iso
- jar
- java
- jfif
- jpe
- jpeg
- jpf
- jpg
- js
- json
- jsp
- key
- kml
- kmz
- log
- m4a
- m4b
- m4p
- m4v
- mcd
- mdbx
- mht
- mid
- mkv
- ml
- mobi
- mov
- mp3
- mp4
- mpa
- mpeg
- mpg
- msg
- nes
- numbers
- odp
- ods
- odt
- ogg
- ogv
- otf
- ova
- ovf
- pages
- parallels
- pcast
- pct
- pdb
- pds
- pef
- php
- pkg
- pl
- plist
- png
- pptm
- prproj
- ps
- psd
- ptx
- py
- qcow
- qcow2
- qed
- qt
- r3d
- ra
- rar
- rm
- rmvb
- rtf
- rv
- rw2
- sh
- shtml
- sit
- sitx
- sketch
- spx
- sql
- srt
- svg
- swf
- tar
- tga
- tgz
- thmx
- tif
- tiff
- torrent
- ttf
- txt
- url
- vdi
- vhd
- vhdx
- vmdk
- vmem
- vob
- vswp
- vvfat
- wav
- wbmp
- webm
- webp
- wm
- wma
- wmv
- wpd
- wps
- xhtml
- xlsm
- xml
- xspf
- xvid
- yaml
- yml
- zip
- zipx
It encrypts files found in the following folders:
- /backup
- /data
- /home
- /kvm
- /media
- /mnt
- /opt/virtualbox
- /srv
- /tmp
- /usr/home
- /usr/local/www
- /var/lib/cassandra
- /var/lib/couchdb
- /var/lib/docker
- /var/lib/elasticsearch
- /var/lib/influxdb
- /var/lib/libvirt
- /var/lib/mongodb
- /var/lib/mysql
- /var/lib/neo4j
- /var/lib/postgresql
- /var/lib/redis
- /var/lib/riak
- /var/lib/vmware
- /var/lib/xen
- /var/mail
- /var/opt/xen
- /var/run/sr-mount
- /var/spool/mail
- /var/vm
- /var/www
It avoids encrypting files with the following strings in their file name:
- basemisc.tgz
- boot.cfg
- bootpart.gz
- features.gz
- imgdb.tgz
- initrd
- jumpstrt.gz
- onetime.tgz
- state.tgz
- useropts.gz
- vmlinuz
It avoids encrypting files with the following strings in their file path:
- /bin/
- /boot/
- /dev/
- /etc/
- /healthd/
- /lib/
- /lib64/
- /mbr/
- /proc/
- /run/
- /sys/
- /vdtc/
- /vmware/lifecycle/
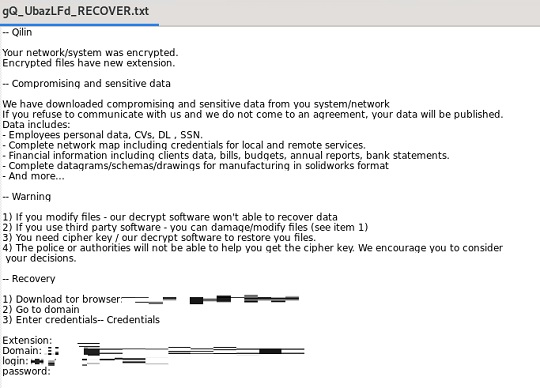
It appends the following extension to the file name of the encrypted files:
- gQ_UbazLFd
It drops the following file(s) as ransom note:
- {Path to Encrypted File}/gQ_UbazLFd_RECOVER.txt
It avoids encrypting files with the following file extensions:
- b00
- b01
- b02
- b03
- b04
- b05
- b06
- b07
- b08
- b09
- t00
- t01
- t02
- t03
- t04
- t05
- t06
- t07
- t08
- t09
- v00
- v01
- v02
- v03
- v04
- v05
- v06
- v07
- v08
- v09
SOLUTION
9.800
18.830.03
20 Nov 2023
18.831.00
21 Nov 2023
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
- Troj.ELF.TRX.XXELFC1DFF044
Step 2
Scan your computer with your Trend Micro product to delete files detected as Ransom.Linux.AGENDA.YXDKOT. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Step 3
Restore encrypted files from backup.
Did this description help? Tell us how we did.

