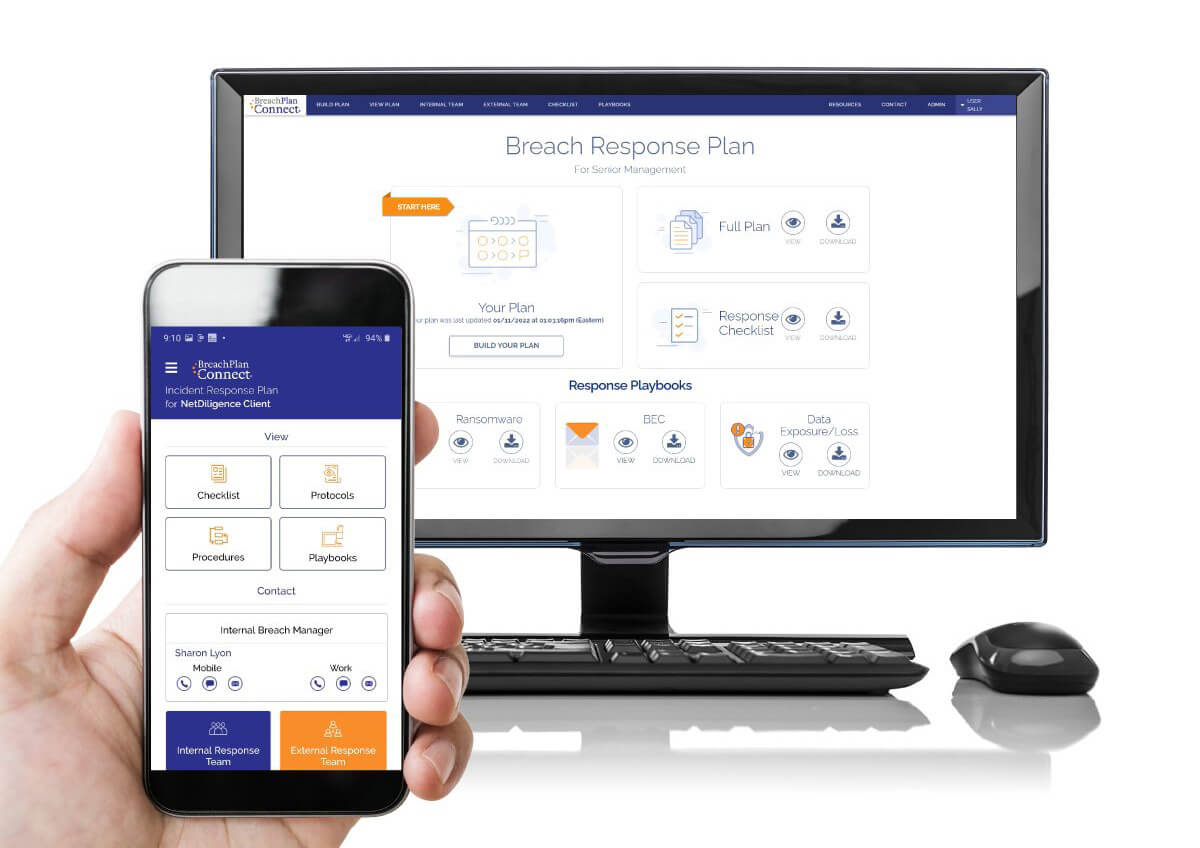
Breach Plan Connect (BPC), powered by NetDilligence®, is a turnkey, pre-written incident response plan solution designed to help organizations oversee and coordinate your organization’s response to a cyber incident.
Companies must have an actionable incident response plan (IRP) to:
Prevent organizational chaos when a breach occurs
Establish and document clear action steps, roles, and responsibilities in the event of a breach
Help minimize the cost of data breach recovery
Help limit the severity of business interruption
Meet your regulatory duties
Start your 30-day free trial of Breach Plan Connect today!
Trend Micro customers receive 30% off the yearly plan price of $3600.
Use discount code: 401620-V
When you register for BPC you’ll have the opportunity to select a Breach Coach.
Trend has partnered with various authorized Breach Coach firms which you can select from or add your own.
You’ll have the opportunity to select your IR vendor of choice along with other key vendors and points of communication for your plan.
Bolster your digital security and privacy with cyber insurance
What is Breach Coach and why do we need one?
A Breach Coach is invaluable to an organization’s cybersecurity preparedness. While any cyber incident will require a knowledgeable expert to triage responses and guide a review of regulatory obligations, a dedicated Breach Coach can seamlessly step into this role already knows your business, its priorities, and its stakeholders. This saves a lot of time—a scarce resource in the event of a cyber incident. Breach Coaches capitalize on that saved time by working with Trend to contain and remediate any unauthorized access issues. Faster remediation gets you back to work sooner rather than later, which saves you money.
What does a Breach Coach do if there's no emergency?
Outside of an emergency cyber scenario, your Breach Coach will focus on proactive ways to best position your organization in the event of an incident in the future. They can speak to your stakeholders and/or employees about technology and cybersecurity best practices, and regularly give specialized presentations to clients called “Tabletop Exercises,” or hypothetical data breach scenarios that allow your stakeholders to practice how they’d respond in the event of a data incident. Additionally, they can assist in customizing your IRP so that your company has easily-accessible resources on:
How to best respond
When to contact certain third-parties
Other steps designed to best shield against any regulatory or other third-party follow-up request or audit