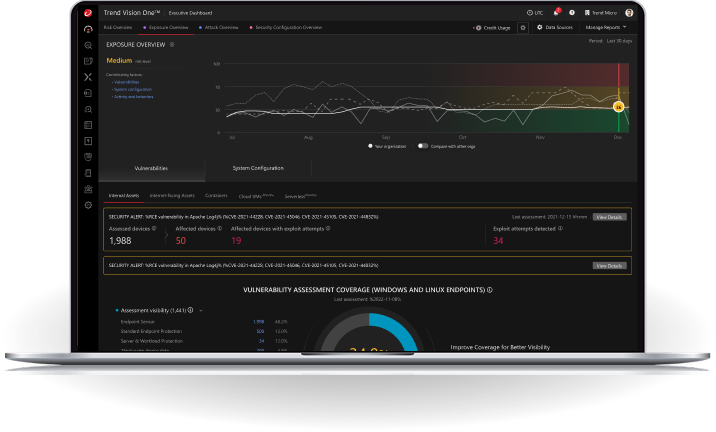
Results for
Security assessment completed
Risk status:
Congratulations! Your domain is at low cyber risk. Maintaining that great security posture is even easier with Cyber Risk Exposure Management.
Your domain could use a little cybersecurity love. Cyber Risk Exposure Management provides you with more context and continuous visibility over all assets.
Your domain is at high risk of becoming a breach entry point. Prioritise remediation and stay secure with Cyber Risk Exposure Management.