Malware
XDR or Managed XDR: extend your team with 3000 threat researchers and 30+ years of cyber security leadership
In recent years, our economy and industries have become omni-connected. Businesses operate in a global economy and are part of an extensive eco-system. With new business models, new types of competition and new cyber risks emerging, businesses fight to earn the trust of existing and new customers every day.
In recent years, our economy and industries have become omni-connected. Businesses operate in a global economy and are part of an extensive eco-system. With new business models, new types of competition and new cyber risks emerging, businesses fight to earn the trust of existing and new customers every day.
Steven Heyde, Regional Director Benelux
To create a competitive edge, the way IT infrastructure is delivered to the business changes at a fast pace. Mobile devices, BYOD, teleworking, cloud applications and cloud computing, DevSecOps, hybrid cloud infrastructures, adoption of SaaS applications (BOX, legal transfer, webmail, …). All these changes also reshaped the world in which the cybercriminals operate and seek new opportunities for their business.
With a growing threat landscape, a widening attack surface, and the increasing sophistication of attacks, threat detection and response have become increasingly challenging for enterprise security teams. At the same time enterprises today are challenged to find and maintain the right skills in their security teams to manage all the risks and deal with all these threats to the business.
A strategic security plan that transcends isolated feature-driven security projects embracing XDR will help you to meet multiple challenges, and here we can help you.
Detection & Response
Detection and response should be part of a complete cyber security strategy. Attacks remain undetected for too long and attackers use the increased attack surface to their advantage by jumping from one environment to another in multi-stage attacks. These different attack layers not only make the attack complex, but they can bypass a traditional protection-based approach. Incorporating detection & response in your cyber security strategy can give you that extra piece of visibility and context you need to discover and stop cybercriminals from moving laterally through your network unnoticed.
While most organizations deploy multiple security solutions, serious threats continue to avoid protection and even detection because data is collected and analyzed in silos. Doing threat analysis requires the SOC or threat analysis team to bring all this data together to understand the full context of an incident and to perform cross-layer security detection and response. Compare it to trying to solve a murder case without knowing the crime scene and you only have the murder weapon, but no fingerprints or any other information.
Beyond Endpoint security – greater context for greater understanding
Although endpoint protection controls are crucial for the security of your users, data and IT assets, over the past 30 years we have seen that threats follow the changes in IT infrastructure. Managing risk and getting visibility across the digitally transformed infrastructure lead to the introduction of detection and response capabilities across the entire enterprise.
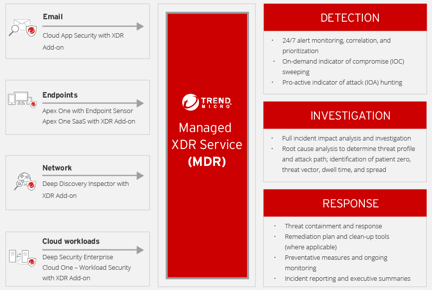
This is what Trend Micro XDR offers. It provides visibility across not just endpoints but also e-mail, servers, cloud workloads and networks, applying AI and expert security analytics to correlate and identify potential threats. This results in fewer, higher fidelity alerts for stretched IT security teams to deal with.
Leadership across layers for Best XDR
The question remains where you place your bets in building a future-proof cyber security strategy. What is the right balance between budget, tooling and vendors for your organization knowing that your people and processes remain key? Who is (are) the vendor(s) that should be part of your cyber security strategy?
First of all, seek superior threat expertise, intelligence and analytics. Look for a vendor that offers solutions with market leading capabilities in all layers where you want to raise your security posture. You have to look beyond the endpoint and analyze the XDR capabilities on mail, server, hybrid cloud workloads and network. You are looking to build a vendor partnership that will support you, the needs of your security teams and your ever-evolving IT infrastructure. You will want to trust this vendor for the security focus and expertise he has demonstrated over the past years and you will trust him to be there in the years ahead.
When you find this partner, have a look at their managed XDR service as it will boost the detection and response capabilities of your security team. It will enable them to identify and deal with prioritized risks. Together with your security integrator of choice this strategy can lead to a true long-lasting partnership.
Please reach out to analyze the possibilities for your organization.