The State of Ransomware: 2020’s Catch-22
A ransomware infection can put organizations in difficult situations. The damage that WannaCry and Petya have caused has made people more wary, leading to stricter and more consistent security measures against a constant threat. Developments in ransomware over the past year have made dealing with ransomware not only difficult but also a delicate matter. Aside from the continuing trend of big-game or targeted attacks, ransomware operators have also come to rely on the cost of data breaches and double extortion to corner their victims into complying with their demands.
It’s essential to understand how the current versions of ransomware came about so that organizations can learn to steer clear of such traps. Using case studies and examples, we examine the ransomware variants that populated 2020 in hopes of creating a guide for dealing with future attacks.
Evolution of ransomware
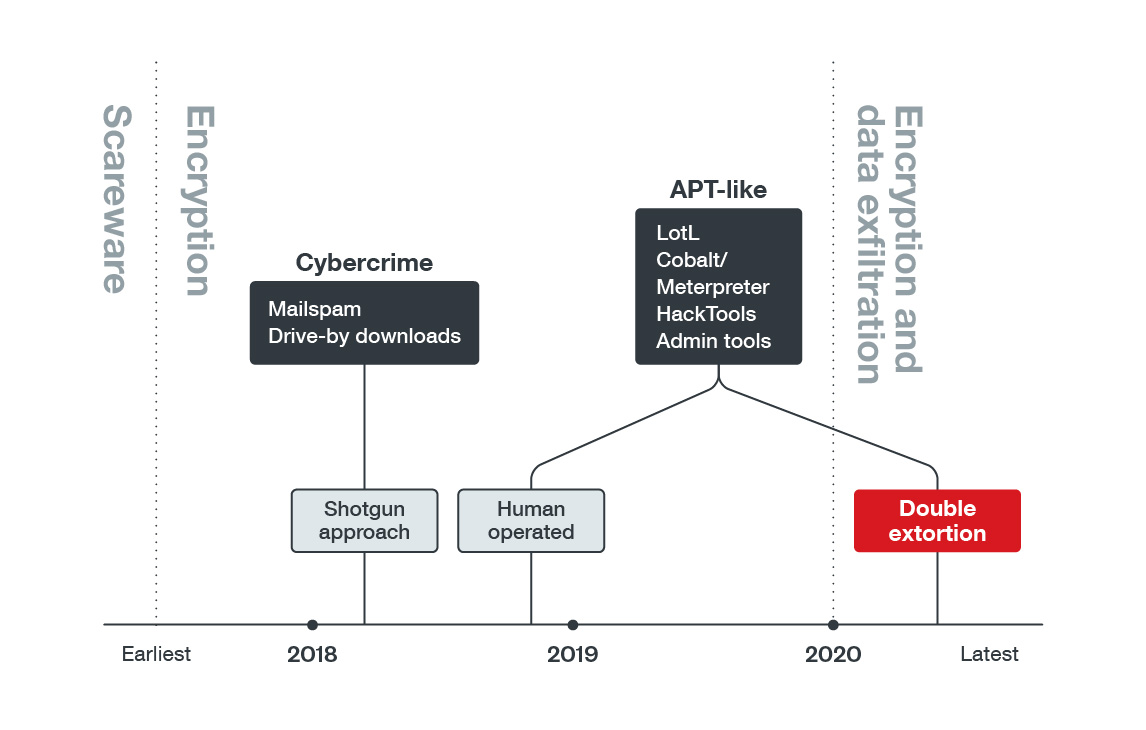
When ransomware created a niche for itself in the cyberthreat landscape, it was categorized as scareware, similar to FAKEAVs that used fake scan results to frighten victims into paying for bogus antivirus software. Slowly, more successful ransomware families progressed into something more threatening as they began to encrypt files. But even these tactics lost their edge over time. Organizations adapted. People realized that simple security measures like regular backup practices can significantly reduce a ransomware attack’s damage. In addition, ransomware actors had a “shotgun” approach (indiscriminately distributing their malware) that allowed antivirus providers to develop solutions to defend against them. In a sense, ransomware notoriety diminished from a hazard to a nuisance. Unfortunately, this was only temporary.
Many new ransomware families emerged in 2016, and in 2017 WannaCry/Wcry wreaked havoc across the globe. In response to these massive ransomware attacks, organizations strengthened their defenses. By 2018, ransomware development seemed to have slowed down as cryptocurrency miners overtook ransomware in terms of detection and new ransomware families decreased. However, we soon learned that the trend only signified a major turning point for ransomware. That same year, Ryuk appeared and set a new standard.
Ryuk was among the first documented ransomware that operated like a targeted attack. It used Trickbot and its modules to propagate and install PowerShell Empire. It also used PowerShell and WMI extensively for lateral movement. By 2019, ransomware attacks have taken on a more targeted approach, which became the norm entering 2020. We will discuss Ryuk and RansomExx attacks as two of our chosen case studies that demonstrate this trend in 2020 in a later section.
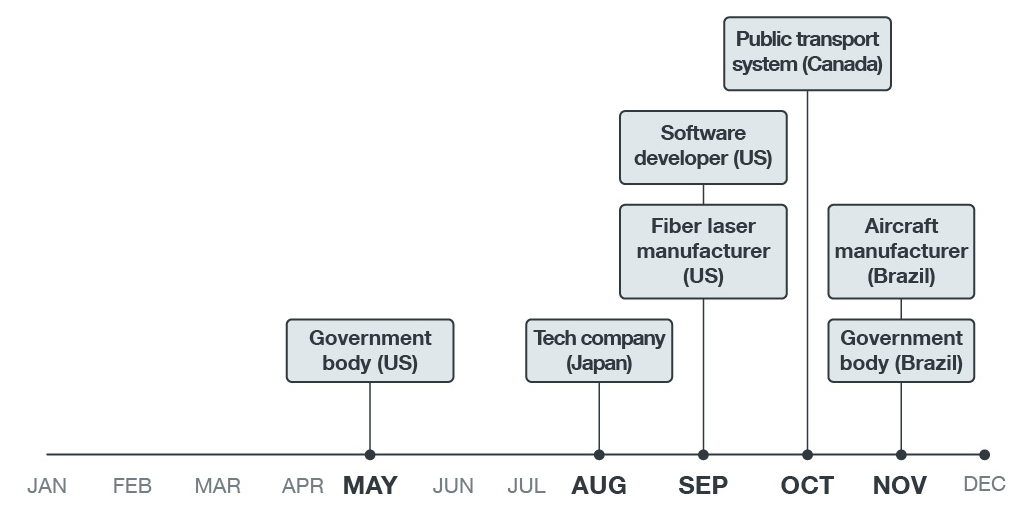
Figure 1. Timeline showing ransomware’s evolution
Overview of ransomware in 2020
The year seemed conducive to the development of new ransomware to a narrowing range of targets. Overall, we saw an increase of new ransomware families, from 95 in 2019 to 127 in 2020, despite the decreased detection of ransomware-related components.
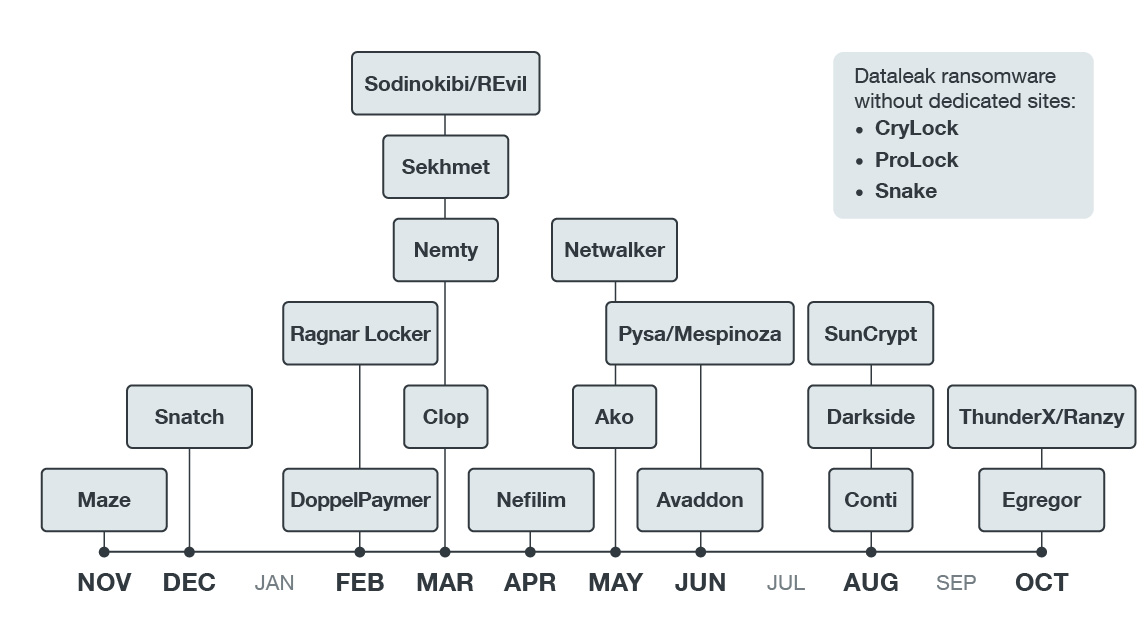
Double extortion stood out as the common ransomware theme in 2020, as data breaches became a significant part of the campaigns. Cybercriminals didn’t just deny access by encrypting their victims’ files; they also started to threaten to expose the files if the target didn’t pay the ransom. It increased the stakes and added pressure for victims to make a deal. This is a real threat, especially for larger organizations that keep sensitive personal and proprietary information. Such attacks could cost organizations more money and tarnish their reputation and brand image.
Maze is an example of a ransomware family that used this tactic and made good of its threat to publicize stolen files. It began operating in 2019 when it conducted several high-profile attacks and even publicly named its victims. In October 2020, it ceased operations only for a new malware Egregor to take its place. Other notable variants used in double extortion campaigns are Nefilim, Sodinokibi, Nemty, RansomEXX, and DoppelPaymer, some of which we will discuss further as case studies.
Figure 2. This timeline (Nov 2019 to Oct 2020) shows that ransomware attacks that involved double extortion happened months apart.
The conditions for double extortions were likely created by the targeted approach that ransomware has adopted. Threat actors utilized familiar tactics, techniques, and procedures (TTPs) no different from other advance persistent threats (APTs) or targeted attacks. In most cases, the attackers already have some level of knowledge about their target’s environment. If their information is lacking, they use hack tools such as network scanners or legitimate administrative tools for reconnaissance. Once they have enough information, they utilize living-off-the-land techniques and compromised accounts to move laterally, search the information that they need, exfiltrate data, and finally, deploy their ransomware. RansomExx is an example of a ransomware variant that utilized several legitimate tools to quickly deploy its final payload
Targeted, human-operated ransomware has been reported for more than a year. However, 2020 saw a wider variety of tools used for various purposes such as reconnaissance and process termination. Campaigns are beginning to look a lot more customized, seeing how they change their techniques according to the environment. A good example is a Sodinokibi attack that used a software’s uninstaller to disable existing applications in the victim’s machines. We further discuss this as our first case study in a later section.
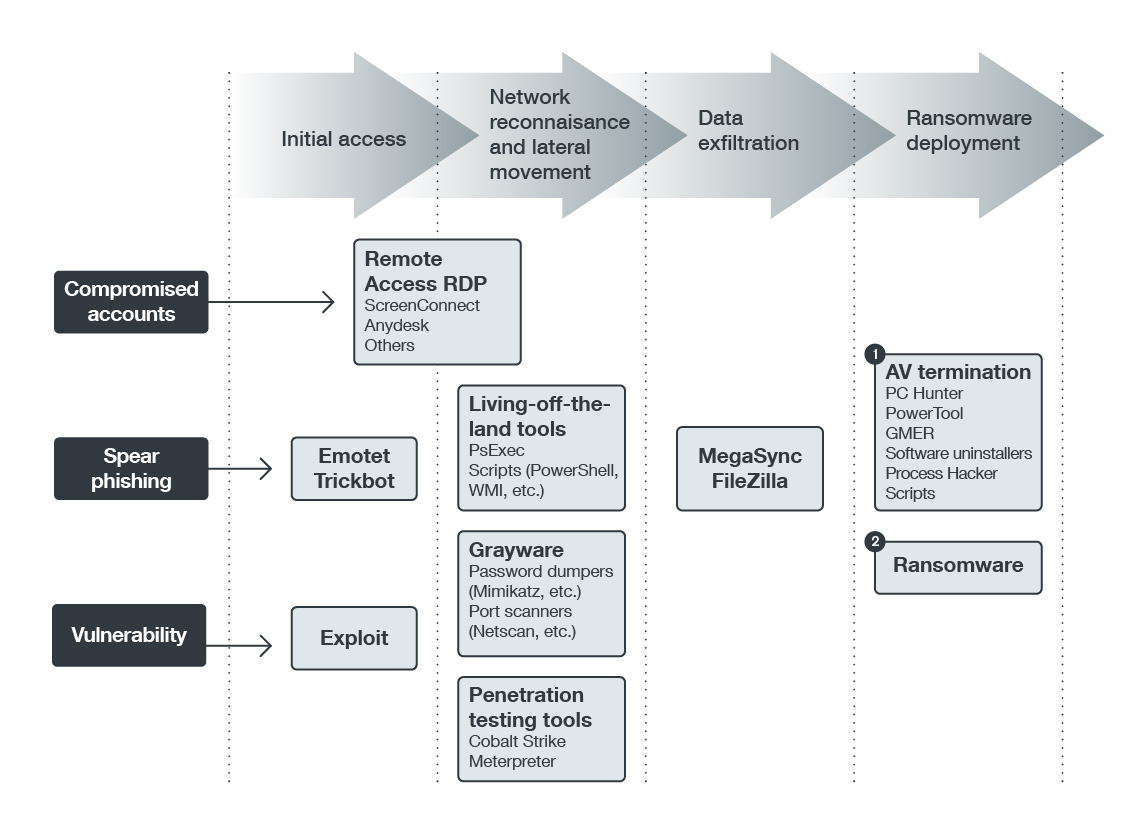
Four stages of ransomware attacks
To better understand the typical ransomware attack process, we break down the stages and components used in today’s campaigns. Ransomware attacks in 2020 can be divided into four stages. Each stage involves tools and techniques customized for specific targets. Figure 3 gives an overview of these stages.
Figure 3: Stages of a ransomware attack in 2020
Initial access. Threat actors can use several methods to penetrate a system’s defenses. Depending on their target, they can use familiar techniques and entry points such as phishing emails, vulnerabilities, or compromised accounts.
- Phishing emails. Examples of ransomware attacks from 2020 that started with phishing emails include Ryuk, Egregor, RansomEXX, and Doppelmayer.
- Vulnerable public-facing software. Ransomware families like Sodinokibi and RansomEXX have been seen consistently using vulnerabilities in remote access tools for their attacks. Common vulnerabilities observed in ransomware attacks from last year include CVE-2019-19781, CVE-2019-11510, and CVE-2019-11510.
- RDP bruteforce attacks. A common tactic for ransomware involved the use of opened and unsecured RDP ports.
- Stolen accounts. These are typically found in underground forums from other data exfiltration campaigns. Other ransomware operators also sell the accounts from the data they exfiltrated from previous attacks.
Network reconnaissance and lateral movement. Using hack tools, open-source tools, and pen-testing tools such as Cobalt Strike, Mimikatz, PowerSploit, and Pyxie attackers can compromise domain controllers and gain access to as many systems as possible. In doing so, attackers create an inventory of the target’s network. Depending on the attacker’s operations, they can either sell the inventory in an underground forum with the winning bidder getting access and deploying their ransomware of choice, or proceed directly to the next stage and deploy a ransomware themselves.
Data exfiltration. This part is essential for the double extortion scheme and is the significant addition to these steps. Before encrypting the victim’s files, the ransomware operator would first steal important data that can be used as leverage against the victim. This can be further broken down into two steps:
- Sensitive information is exfiltrated for extortion (e.g., proprietary information, intellectual property, and PII).
- Stolen information is uploaded to the cloud or to remote FTP locations. The commonly used tools are 7-zip, Megasync, WinSCP, custom scripts, vsftpd, and Rclone.
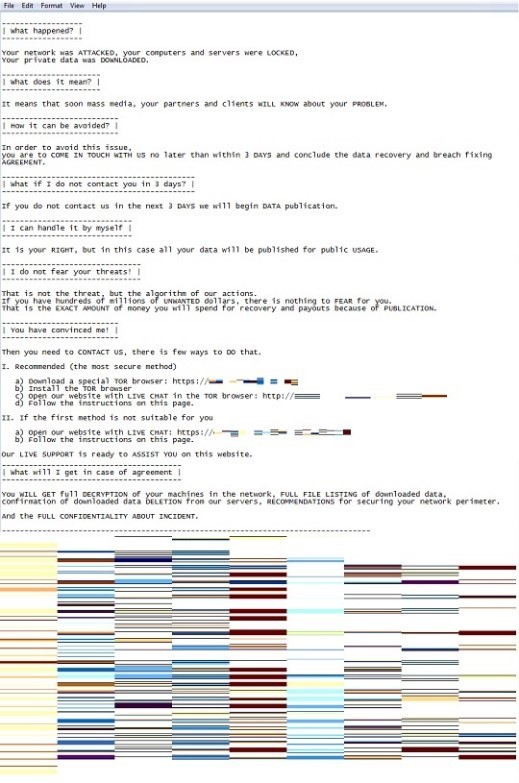
Ransomware deployment. With data stolen, they can proceed with deploying and running the chosen ransomware. Defenses, running processes, and services are taken down to ensure effective ransomware deployment. Attackers also delete their footprints by deleting event logs. The ransomware is deployed and executed remotely using tools like PsExec, Group Policy, WMI, and Custom Scripts. Once the files have been encrypted, the operators declare their demands via a ransom note.
We have observed that ransomware attacks typically span from days to weeks. In the next section, we use case studies and examples to illustrate how these stages play out in real scenarios and what components are typically used by different ransomware variants.
Figure 4. Ransom note threatening the publication of stolen information from an Egregor attack
Case study 1: Sodinokibi
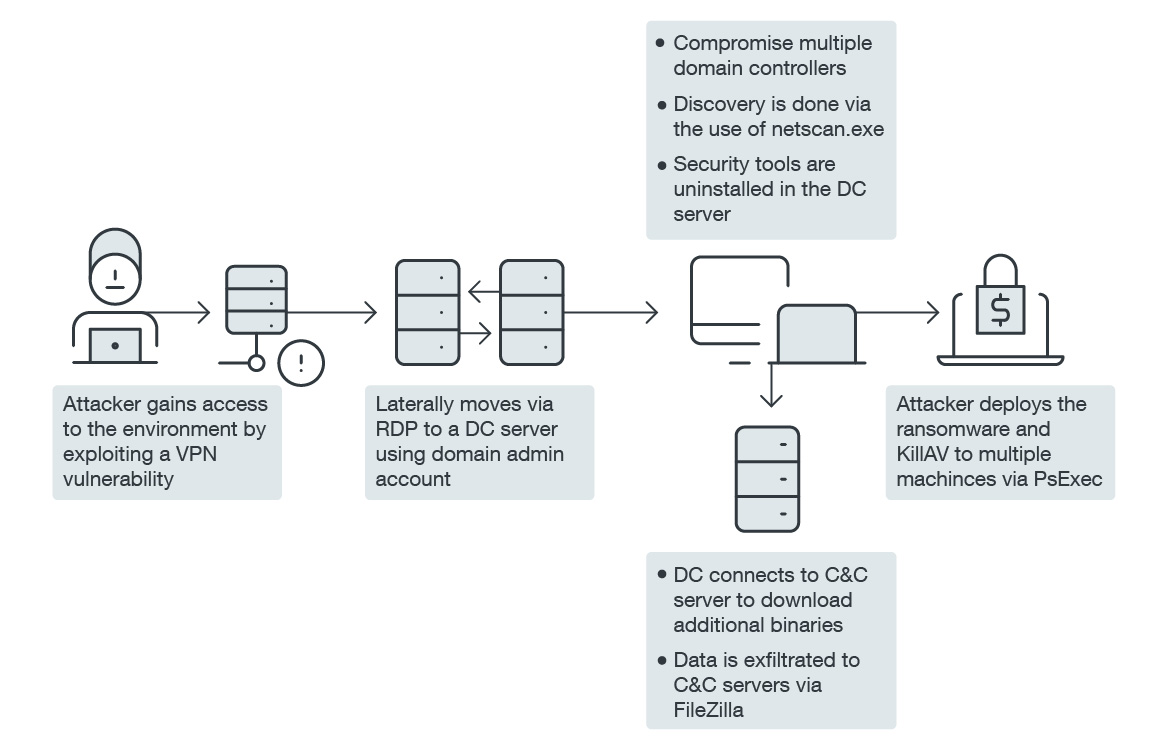
Figure 5. Sodinokibi infection chain
The infection source is unclear in the investigations, but based on established information about Sodinokibi, the actors could have used a VPN vulnerability. We also identified several compromised administrator accounts that were used consistently in all remote logons via RDP. These were used to gain access to other machines and move laterally across the network.
NetScan was used to obtain information about the victim’s network devices, such as shared folders, IP addresses, and user accounts. We’ve seen evidence that this admin tool already existed in their environment for more than a year, but it could have been used legitimately at first. We don’t have any evidence to say otherwise.
On the third day, FileZilla was installed. It is a free and open-source FTP client that allows the transfer of files. In this case, it appears that it was used to send out stolen data to the attackers. They must have gathered enough information about the company within two to three days since we did not see the FileZilla execution until two days before the ransomware was deployed. Normally, ransomware actors would quietly move around the network first to find whatever information they can before starting to encrypt the files.
PsExec was another tool used. It was used to propagate copies and remotely execute the ransomware and other files across the network. It is a legitimate Windows Sysinternals tool commonly used by administrators but it has also been abused by several threat actors. Scheduled tasks were also created in some machines to start the AV uninstaller and ransomware upon reboot.
What’s noteworthy about this attack?
AV-termination. While AV-termination is not new and not unique to this attack, it is interesting to see the use of an uninstaller program for a specific software used by the victim company. This suggests a high level of knowledge and awareness of the victim’s environment and shows the level of customization used in the attack.
In other ransomware attacks, various applications were used to disable security software. The most common ones used this year were Process Hacker, PowerTool, GMER, and PC Hunter.
Data exfiltration. We believe FileZilla was used for data exfiltration because there were several artifacts seen within the timeline of the FileZilla installation, suggesting that the attackers were trying to find PIIs For example, after the compromised account was logged in, folders with labels “{Company} Clients,” “Finance Meetings,” and “Invoices” were accessed. In addition, the terms “ssn” and “personal” were searched.
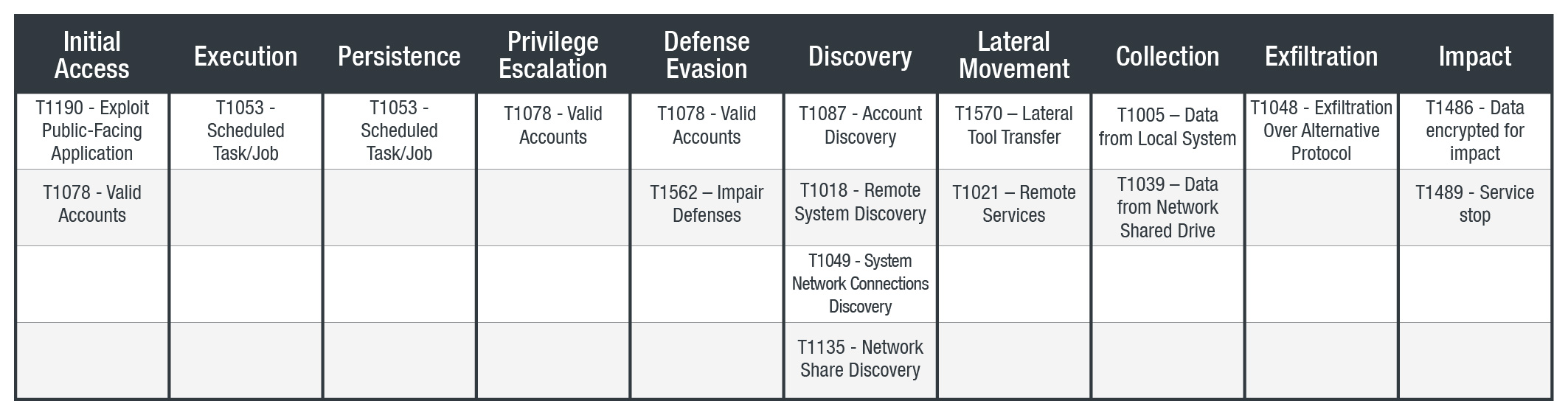
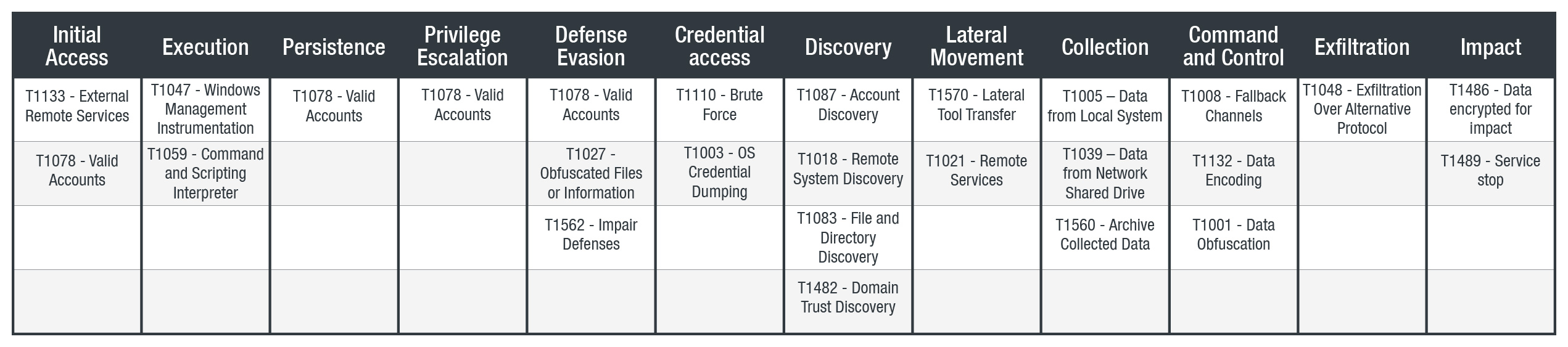
Table 1. Tactics and techniques used by Sodinokibi
Case study 2: Nefilim
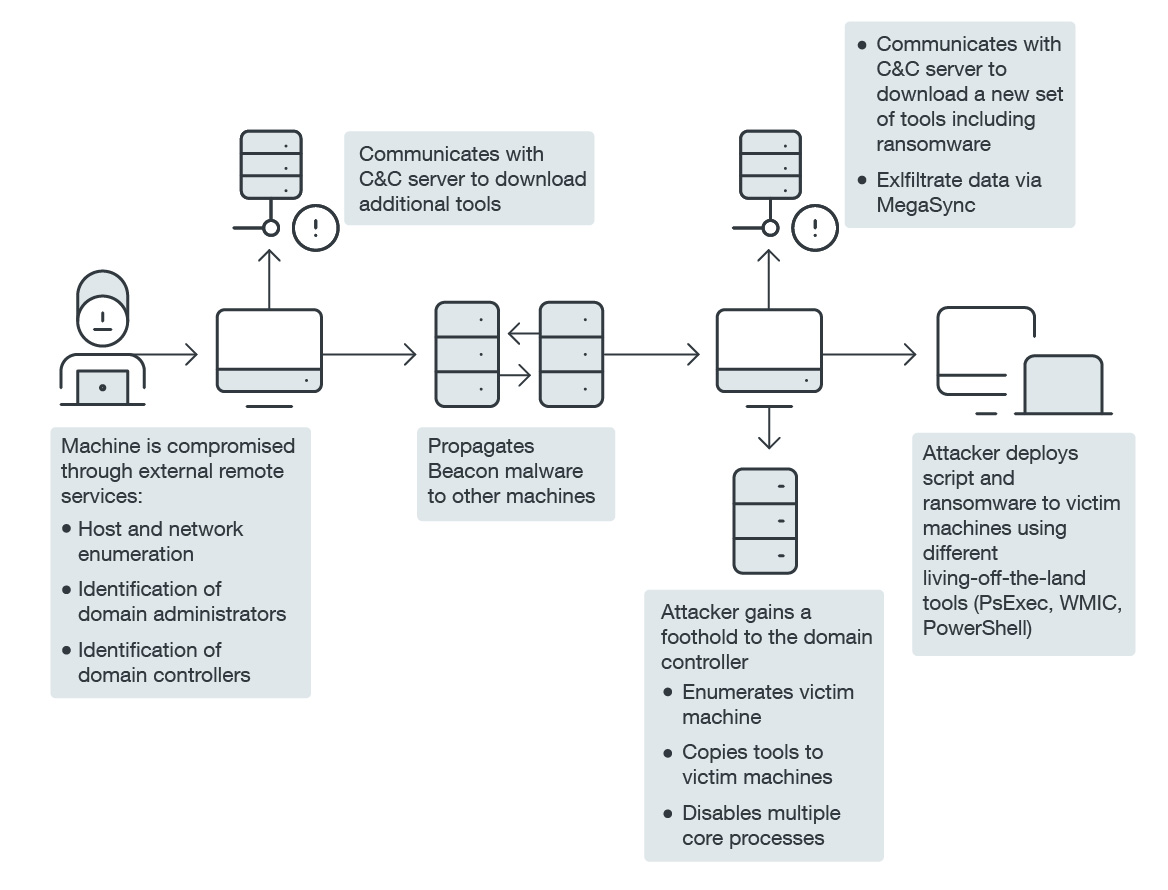
Figure 7. Nefilim infection chain
One of the commonly seen techniques in ransomware attacks this year is the use of the penetration testing tools like Cobalt Strike beacon or Meterpreter. These allow the attackers to perform a number of functions such as command execution and password dumping. Many times, these are fileless, or executed in memory using scripts like PowerShell. In this attack, it functioned as a backdoor that connects to the newly registered command-and-control (C&C) server.
For additional reconnaissance, we observed the use of SMBTools (detected as HackTool.Win32.SMBTool.AB). It can obtain information about the host, including the OS, admin rights, usernames and passwords, hostname, etc.
A few weeks after covertly gathering information, the attackers started to send the data out using MegaSync a day before the widespread ransomware infection occurred. This is somehow reminiscent of the data exfiltration method in the Sodinokibi incident, except that it used FileZilla.
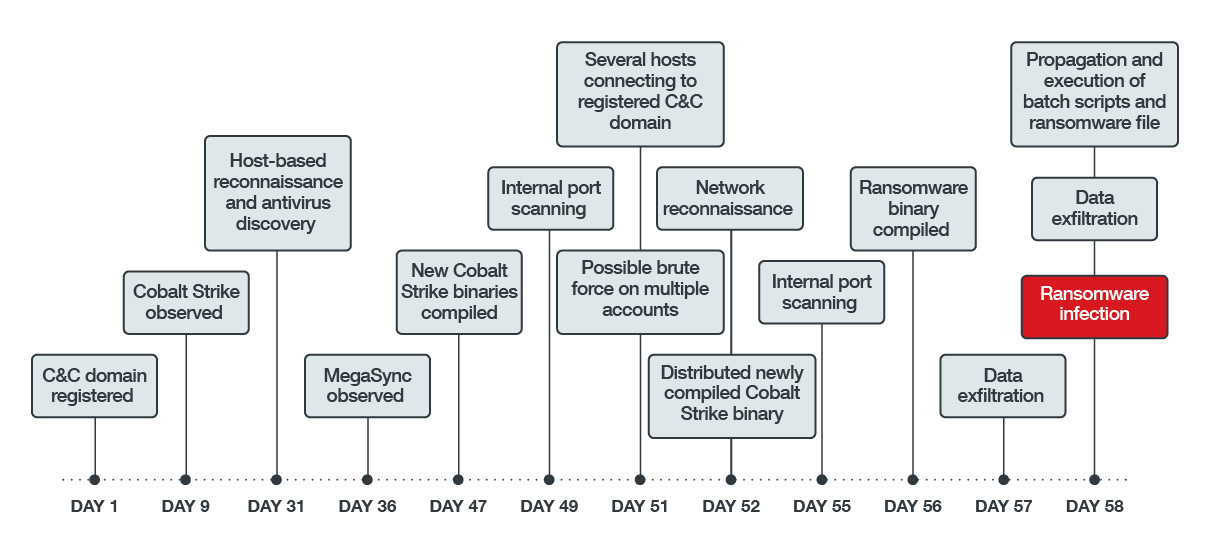
Figure 8. Nefilim attack timeline
What’s noteworthy about this attack?
Longer timeframe. Compared to other ransomware attacks, Nefilim takes considerably more time from start to finish. The longer timeframe makes its behavior seem like that of an APT attack because the actors didn’t rush towards their end-goal and quickly move on to another target.
Stealth or living-off-the-land techniques. Because this attack involves staying longer in the network, it needs to stay hidden for as long as they can. To do this, the threat actors mostly used legitimate utilities (taskkill.exe, net.exe, sc.exe, wmic.exe, etc.) that already existed in the environment — a technique typically known and described as living-off-the-land. Aside from this, the other components, such as the Cobalt Strike binaries, and the C&C domain, were newly compiled or newly registered. Reactive solutions such as signature-based blocking will not be effective in cases like this. Below are examples of how the threat actors used the living-off-the-land technique in this attack:
| Action | Legitimate utilities |
| Process and Service Termination | taskkill /im |
| net stop |
|
| sc config |
|
| Copies components to windows\temp | start copy |
| start wmic /node: |
|
| Executes a file remotely using psexec | start psexec.exe \\ |
Table 2. Examples of how legitimate utilities were used by Nefilim
They also used hack tools such as SMBTool, but its use varies depending on the need. Nefilim has been seen using other tools aside from those we have described here.
Table 3. Tactics and techniques used by Nefilim
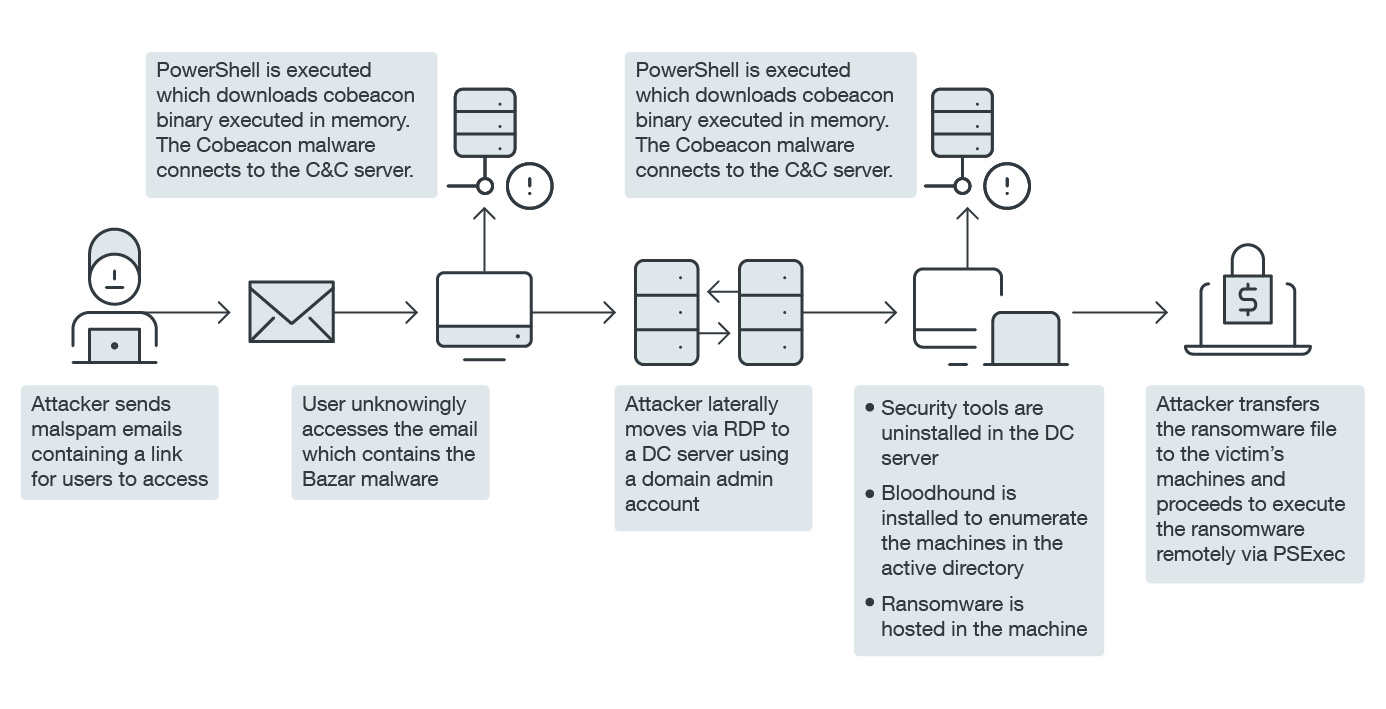
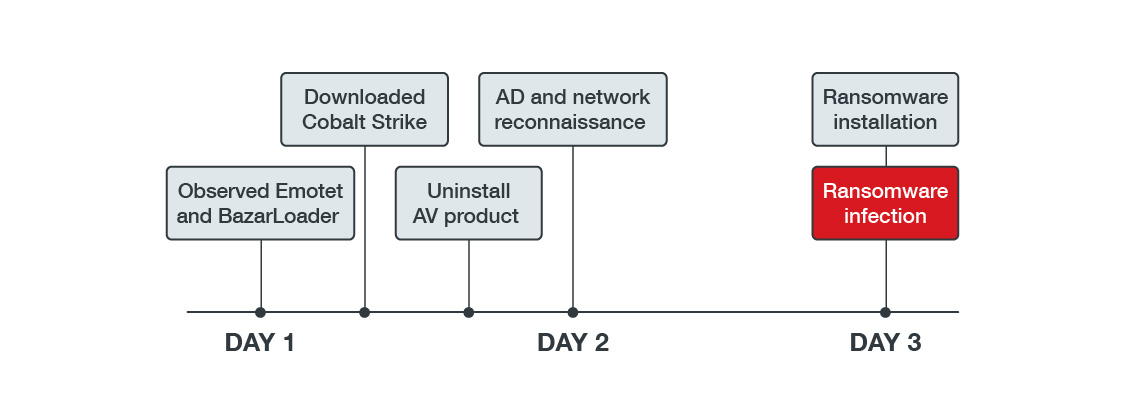
Case study 3: Ryuk
Figure 9. Ryuk infection chain
Among the three case studies we have chosen, this Ryuk campaign does not match the typical double extortion strategy that many ransomware families currently use. While Ryuk was first discovered in 2018, old does not mean obsolete in this case. Ryuk made quite a lot of noise again this year, mostly because it targeted the already-fatigued healthcare industry.
Figure 10. Ryuk campaign timeline
Spear phishing and malspam campaigns are tried and tested techniques that can easily be exploited to distribute certain malware. Although we did not see evidence of related malicious emails in this incident, we suspect that it might be the point of entry in this attack because of already known information about Ryuk’s companion malware such as Emotet and Trickbot.
The TTPs in this incident are almost comparable to the other two incidents previously discussed. It used a combination of living-off-the-land techniques, AV termination using a software uninstaller, and penetration testing tools. Cobalt Strike beacon was downloaded from a remote location through PowerShell. PowerShell Invoke-Command and Invoke-SMBExec commands were also used to execute Bazarloader remotely.
Several compromised accounts were used to login via RDP to move across the network and perform specific tasks. Once logged on, the attacker attempted to uninstall the AV software using its own uninstaller. In other machines, they performed AD reconnaissance using ADFind and BloodHound. Other possible reconnaissance tools used were built-in tools such as ping.exe, net.exe, nslookup, etc.
Finally, after a day or two spent enumerating hosts in the network, Ryuk ransomware was distributed via bitsadmin and then executed remotely through PsExec.
What’s noteworthy about this attack?
Target. Despite the increased popularity of double extortion ransomware, some older ransomware families still afflict many organizations. Ryuk is particularly interesting because of its target of choice. While many ransomware threat actors said that they would leave the healthcare industry alone as the world grapples with the pandemic, the people behind Ryuk made no such promise and continued to do so. In October 2020, US-CERT released an advisory regarding ransomware targeting the healthcare sector.
Companion malware. Ryuk’s TTP didn’t stray too far away from what we’ve seen in 2018. It is still targeted and can be distributed through another malware, only this time we’ve seen it linked to Emotet and BazarLoader instead of Trickbot. BazarLoader or Bazar malware has been linked to Trickbot because of similarities in code, crypters, infrastructure, and infection techniques, including reused domains, use of revoked certificates, and almost identical decryption routines. It was also seen in Covid-19 themed phishing emails that contained links to malicious Google Docs files. Bazar malware is known to deploy both Ryuk and its backdoor component to establish persistence.
Ryuk isn’t the only ransomware that utilized other malware to propagate. We have reported on a Defray ransomware variant that used a trojanized version of a well-known software to propagate. The use of a popular open-source software as a façade helped in disguising its activities, always useful in targeted attacks.
Table 4. Tactics and techniques used by Ryuk
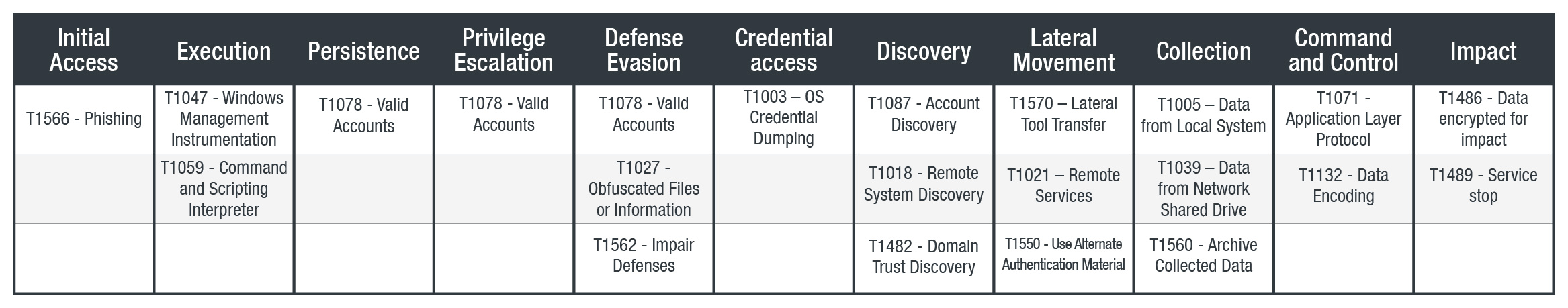
Case study 4: RansomEXX
Aside from these case studies that demonstrate the four stages while also highlighting each ransomware family’s unique features, it is also worth noting that ransomware continues to evolve. A good example of this is RansomEXX, another consistent name in the 2020 ransomware landscape and has been behind several high-profile attacks during that year.
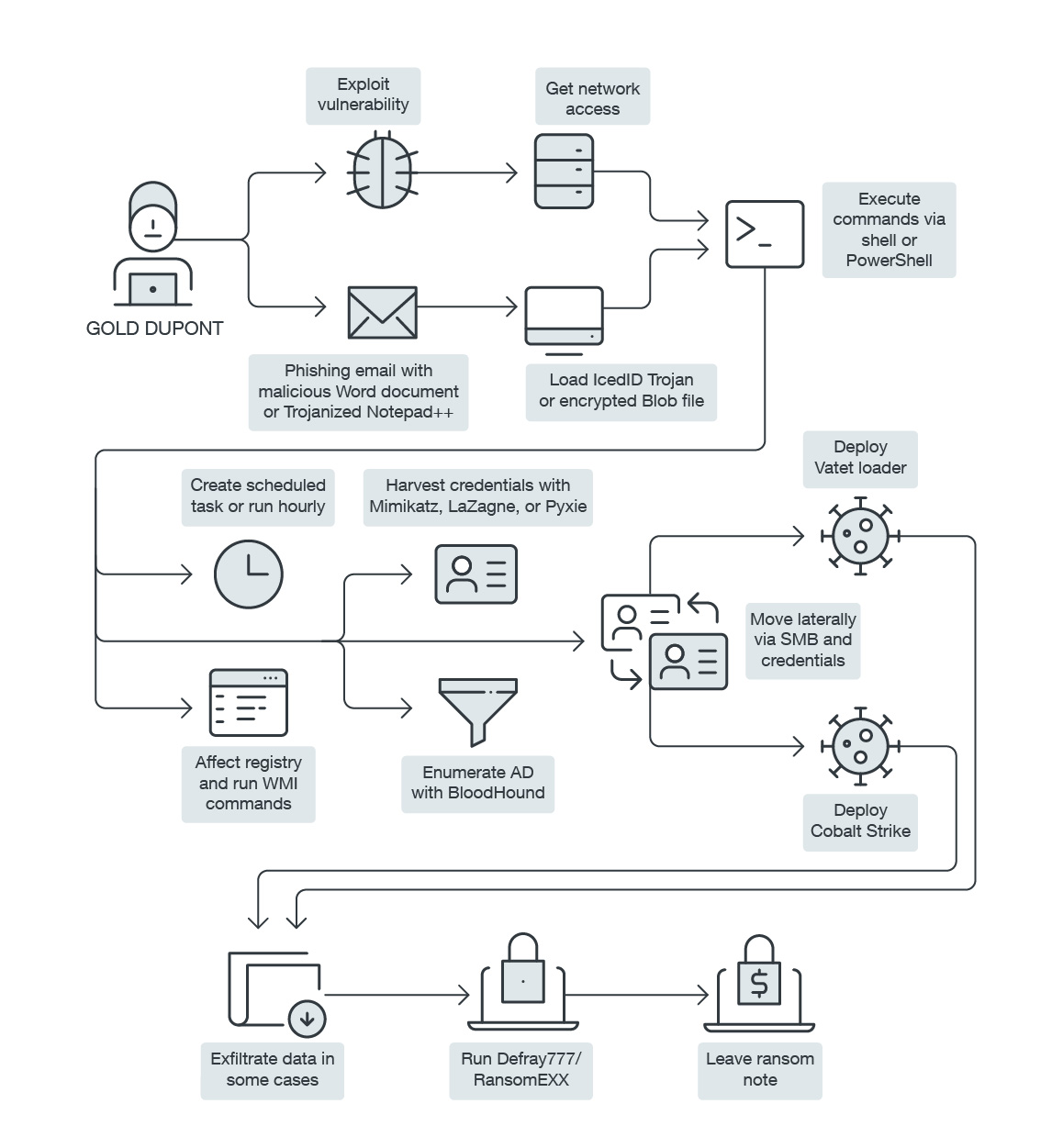
RansomEXX, aka Defray777, has been linked to the cybercriminal group Gold Dupont, which has been active 2018. Their goals are focused on financial gain, and their main arsenal includes RansomEXX or Defray777, Cobalt Strike, Metasploit, and Vatet Loader.
Figure 11. Timeline of known and public RansomEXX attacks in 2020
RansomEXX was first discovered in May 2020. By the second half of the year, it deployed attacks months apart. The RansomEXX ransomware family’s latest reported victim is the world’s third-largest airplane maker based in Brazil. The company reported that the attack happened on November 30. Less than a month later, it was reported that RansomEXX had leaked the company’s data in retaliation for not paying the ransom, making good on their double extortion scheme.
Figure 12. RansomEXX infection chain
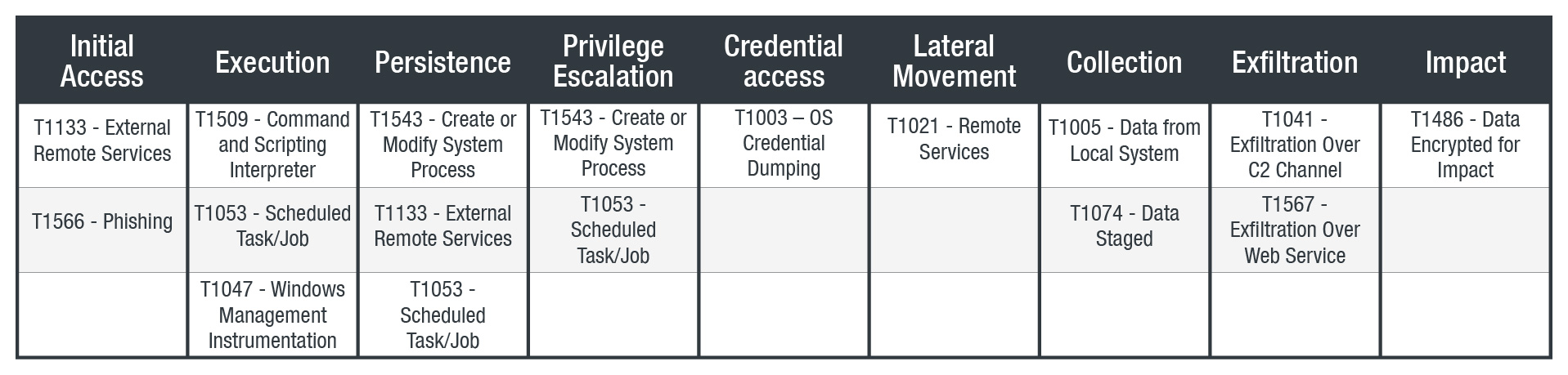
Table 5. Tactics and techniques used by RansomEXX
That same month, the Brazilian Superior Justice Court suffered a very similar ransomware attack that encrypted all their 1,200 virtual machines — including their backups. The attack, used a trojanized version of Notepad++ or Vatet loader, similar to the aforementioned Defray case. In this attack, RansomEXX also used several vulnerabilities to elevate privileges, move laterally, and compromise ESXi hosts such as CVE-2018-13379, CVE-2019-5544, CVE-2020-1472, and CVE-2020-3992.
What is notable about RansomEXX?
Expansion to Linux. One of the most noteworthy developments of RansomEXX is its Linux variant, which was used in November in Brazil, mostly targeting VMWare environments. From initially infecting Windows servers, its developers have created a newer variant capable of infecting Linux servers. We have also observed threat actors actively using this variant, detailed in our “Expanding Range and Improving Speed: A RansomEXX Approach” blog post.
Hardcoded name of the victim organization. RansomEXX is also a good example of the targeted nature of ransomware. One indication of how RansomEXX targets its victims lies in the samples from each attack, which contained the hardcoded name of the victim. This shows how much threat actors behind these attacks customize their campaigns to fit the profile of their chosen victims.
Aside from demonstrating the ransomware trends seen over the past year, RansomEXX’s consistency, speed, and activity seem to stem from the preparation and planning the threat actors behind this malware have done before the beginning of their campaigns and the momentum of development that they built throughout 2020.
Conclusion and security recommendations
As mentioned earlier, the capability to conduct data breaches (and consequently, double extortion) was introduced by the targeted approach ransomware attacks have adapted. With knowledge of their victims, cybercriminals can better plan and identify the right pressure points to maximize their chances of extorting money. What can organizations do if backups no longer offer a nearly consequence-free solution to ransomware?
Like with any cyberthreat, prevention is still key. Organizations should be knowledgeable of the current techniques and components being used by ransomware operators. Taking note of the four stages of a ransomware attack can help in identifying signs of intrusion such as phishing emails and possible openings like unpatched vulnerabilities.
It is also important to take note of other trends and factors that affect the cyberthreat landscape. At present, work-from-home (WFH) and remote setups are still realities organizations face. This reality has opened new security challenges as operations have spread out over home devices and networks with varying degrees of security. Ransomware is among the threats to have seemingly gained from this prolonged situation. Advocating a culture of security and employing WFH best practices can help minimize the chances of success for any of today’s cyberthreats.
Finally, organizations should review and update existing defenses and protocols against ransomware attacks. Ransomware has changed a great deal in a span of a few years. Strategies that were developed for previous attacks, while still relevant, might not be adequate for future versions of ransomware.
For now, here are our security recommendations.
- Regularly back up files. Despite current developments, backups still provide a significant safeguard against ransomware encryption and other cyberthreats.
- Limit access to shared/network drives and turn off file sharing. This minimize the chances of spreading a ransomware infection to other devices.
- Employ secure authentication strategies. Enable options such as multi-factor authentication to deny threat actors access to accounts.
- Disable local admin accounts. If this is not possible, follow Microsoft’s recommendations on securing local admin accounts.
- Update and patch. Keep systems updated and apply patches as soon as possible to prevent infection through exploits.
- Enforce the principle of least privilege. This prevents users from running certain programs, like hack tools and unwanted applications, utilized by ransomware.
- Enforce application control. This mitigates the use of remote access software. An example of this is Microsoft Applocker and Trend Micro Application Control.
Trend Micro Solutions
Trend Micro Cloud One™– Workload Security has a virtual patching feature that can protect the system against exploits. Since some of the malware’s techniques can bypass signature-based security agents, technologies like Trend Micro Behavior Monitoring and Machine Learning can be used to prevent and block those threats.
Enterprises can also take advantage of Trend Micro XDRTM, which collects and correlates data across endpoints, emails, cloud workloads, and networks, providing better context and enabling investigation in one place. This, in turn, allows teams to respond to similar threats faster and detect advanced and targeted threats earlier.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Ransomware Spotlight: Agenda
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™
- Forecasting Future Outbreaks: A Behavioral and Predictive Approach to Proactive Cyber Risk Management
- Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report


 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One