RANSOM_CRYPCHIM.A
Win32/Filecoder.NEZ (ESET); Trojan-Ransom.Win32.Chimera.d (Kaspersky); TR/Crypt.ZPACK.127699 (Avira);
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
Makers of this ransomware scares users by claiming that it posts online all files that it locks and encrypts. It also invites its victims to be affiliated with its makers. It ensures that its victims pay the ransom amount by encouraging to download a decrpyting software that detects whether payment has been made or not.
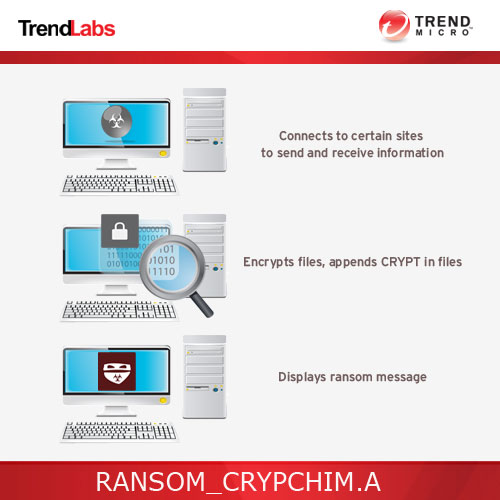
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It connects to certain websites to send and receive information. It deletes itself after execution.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan adds the following processes:
- iexplore.exe
It is injected into the following processes running in memory:
- taskhost.exe
Other Details
This Trojan connects to the following URL(s) to get the affected system's IP address:
- http://bot.whatismyipaddress.com
It connects to the following website to send and receive information:
- {BLOCKED}.{BLOCKED}.168.168
- {BLOCKED}.{BLOCKED}.211.81
It encrypts files with the following extensions:
- .3dm
- .3ds
- .3fr
- .3g2
- .3ga
- .3gp
- .a2c
- .aa
- .aa3
- .aac
- .accdb
- .aepx
- .ai
- .aif
- .amr
- .ape
- .apnx
- .ari
- .arw
- .asf
- .asp
- .aspx
- .asx
- .avi
- .azw
- .azw1
- .azw3
- .azw4
- .bak
- .bay
- .bin
- .bmp
- .camproj
- .ccd
- .cdi
- .cdr
- .cer
- .cgi
- .class
- .cmf
- .cnf
- .conf
- .config
- .cr2
- .crt
- .crw
- .crwl
- .cs
- .csv
- .cue
- .dash
- .dat
- .dbf
- .dcr
- .dds
- .der
- .disc
- .dmg
- .dng
- .doc
- .docm
- .docx
- .dvd
- .dwg
- .dxf
- .eip
- .emf
- .eml
- .eps
- .epub
- .erf
- .fff
- .flv
- .gfx
- .gif
- .gzip
- .htm
- .html
- .iiq
- .indd
- .ini
- .iso
- .jar
- .java
- .jfif
- .jge
- .jpe
- .jpeg
- .jpg
- .js
- .jsp
- .k25
- .kdc
- .key
- .lit
- .m3u
- .m4a
- .m4v
- .max
- .mdb
- .mdf
- .mef
- .mkv
- .mobi
- .mov
- .movie
- .mp1
- .mp2
- .mp3
- .mp4
- .mp4v
- .mpa
- .mpe
- .mpeg
- .mpg
- .mpv2
- .mrw
- .msg
- .mts
- .nef
- .nrg
- .nri
- .nrw
- .number
- .obj
- .odb
- .odc
- .odf
- .odm
- .odp
- .ods
- .odt
- .ogg
- .orf
- .p12
- .p7b
- .p7c
- .pages
- .pdd
- .pef
- .pem
- .pfx
- .php
- .png
- .pps
- .ppt
- .pptm
- .pptx
- .prf
- .ps
- .psd
- .pspimage
- .pst
- .ptx
- .pub
- .py
- .qt
- .r3d
- .ra
- .raf
- .ram
- .rar
- .raw
- .rm
- .rpf
- .rtf
- .rw2
- .rwl
- .sql
- .sqllite
- .sr2
- .srf
- .srt
- .srw
- .svg
- .swf
- .tga
- .tiff
- .toast
- .ts
- .txt
- .vbs
- .vcd
- .vlc
- .vmdk
- .vob
- .wav
- .wb2
- .wma
- .wmv
- .wpd
- .wps
- .x3f
- .xlk
- .xls
- .xlsb
- .xlsm
- .xlsx
- .xml
- .xps
- .xsl
- .yuv
- .zip
It deletes itself after execution.
NOTES:
This malware drops the file YOUR_FILES_ARE_ENCRYPTED.HTML once it is successful in encrypting files.
It appends crypt to successfully encrypted files.
It checks the following file paths for the presence of installed AV Products:
- %Program Files%(x86)
- %Program Files%
It checks the system for the presence of the following AV Products:
- AVAST Software
- AVG
- AhnLab
- Avira
- Bitdefender
- Bullguard Ltd
- COMODO
- CheckPoint
- ESET
- F-Secure
- G DATA
- K7 Computing
- Kaspersky Lab
- Malwarebytes Anti-Malware
- McAfee
- McAfee.com
- Microsoft Security Client
- Norman
- Norton Security
- Norton Security with Backup
- NortonInstaller
- Panda Security
- Quick Heal
- Spybot - Search & Destroy
- Spybot - Search & Destroy 2
- Trend Micro
- VIPRE
The following web page is displayed after the encryption routine ends.

SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Search and delete this file
- YOUR_FILES_ARE_ENCRYPTED.HTML
Step 3
Scan your computer with your Trend Micro product to delete files detected as RANSOM_CRYPCHIM.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
NOTES:
Restore the encrypted files from backup.
Did this description help? Tell us how we did.

