Container
What is a container?
A container is a unit of software that holds the necessary components — code, runtime, system tools, system libraries, and software dependencies, among others — for an application to run easily across different computing environments, i.e., any computer hardware, infrastructure, or cloud environment.
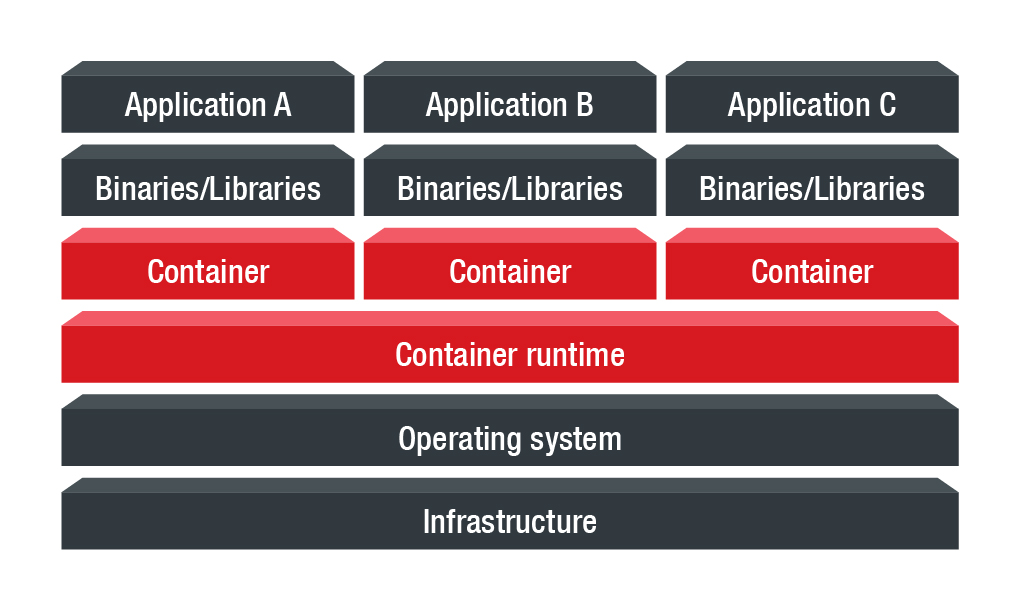 Using a container optimizes the process of software development. Typically, getting software to run from one computing environment to another can be problematic. For example, challenges arise when the supporting software environments are not the same. Containers solve this by bundling all components into one package. Now, the differences in operating system and the underlying infrastructure are not a hindrance because they have been abstracted away by the container runtime.
Using a container optimizes the process of software development. Typically, getting software to run from one computing environment to another can be problematic. For example, challenges arise when the supporting software environments are not the same. Containers solve this by bundling all components into one package. Now, the differences in operating system and the underlying infrastructure are not a hindrance because they have been abstracted away by the container runtime.
What is a container image?
A container image defines the executable code, supporting libraries, computing requirements, and other objects required to run a process on IT infrastructure. To build a running container, a container image is needed.
A container image is compiled from file system layers built onto a modified or a completely new image. An image can be built from scratch using the build command of a container platform, and it can also be modified and be used as basis for a new container. In addition, it can be updated over time to fix bugs, introduce more functionalities, or change the product completely.
How to secure containers
Secure containers by identifying flaws in their components
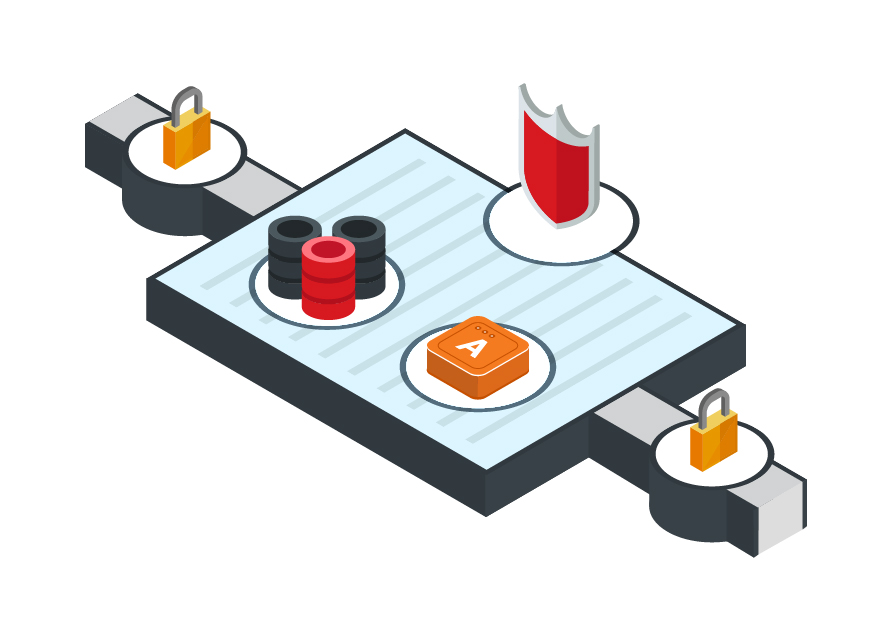
Containers use images to run applications. A vulnerable image means a container is at risk of malware infection or exploitation, and, in turn, the host running the container may also be at risk. Security flaws should be identified early in the build process and before the container is run in production. This way, security is already integrated into the process, saving time and effort by getting reliable builds into production. It can also reduce overhead and disruptions in the application’s lifecycle. Here are some conditions for ensuring a secure container:
- Container images should be scanned. After scanning, container images that are known to be safe or in good quality should be signed, authenticated, and drawn from a trusted registry. A user can easily assume that a registry is safe, but when the said precautions aren’t in place, problems can arise.
- The container runtime should be secured as it runs containers in a loosely isolated manner. If the container runtime is not secured, significant consequences concerning the container and the host can take place. Therefore, access to it should be restricted. In addition, encrypted communication protocols should be employed when exposing it in the network.
- Resources should be isolated. Control groups and namespaces should be properly configured, for example, it should be determined what resources and how much a container is allowed to use.
- Security should be baked into the process in order to improve the overall efficiency of the operations. For example, Docker has documentation on the built-in security features of its container engine.