TSPY_RAPID.A
TrojanSpy:Win32/Skeeyah.A!rfn (Microsoft)
Windows


Threat Type: Trojan Spy
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Trojan Spy arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It retrieves specific information from the affected system.
TECHNICAL DETAILS
Arrival Details
This Trojan Spy arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Information Theft
This Trojan Spy retrieves the following information from the affected system:
- Roblox game session ticket from server
- Roblox Cookie - contains account data information
Other Details
This Trojan Spy does the following:
- It retrieves the game session ticket by getting the value of "-t" argument from running RobloxPlayerBeta.exe process.
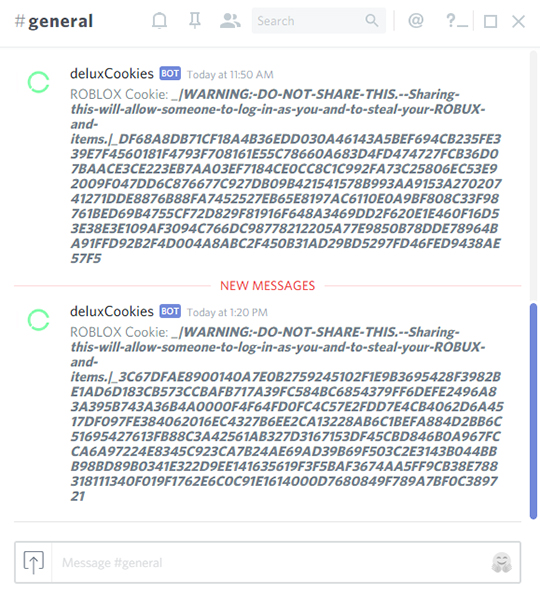
- It uses Discord Webhook URL to send the Roblox Cookie as an automated message to its Discord channel:
https://{BLOCKED}dapp.com/api/webhooks/292933102060437504/6dkH6MUyHmo9IZ0ImsKH7Z-Xo7CdG_EGTQGfj8RDzJPgkyIA5FTUWKZCf6gSO9UqagzN
NOTES:
The message sent to discord is in the following format: _|WARNING:-DO-NOT-SHARE-THIS.--Sharing-this-will-allow-someone-to-log-in-as-you-and-to-steal-your-ROBUX-and-items.|_{random hex values}
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as TSPY_RAPID.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


