On June 2023, the SANS Institute published a new report, “Breaking IT/OT Silos With ICS/OT Visibility” written by Jason Christopher, SANS analyst, with the cooperation of Trend Micro. This survey explores how respondents tackle ICS/OT visibility challenges, the gaps across the IT-OT boundary, the roadblocks to expanding visibility, and the maturity comparisons from both domains. This survey had nearly 350 respondents responsible for IT and OT security across a wide variety of industrial sectors worldwide.
This article discusses the barriers to expand visibility and the labor intensity of security operation with referring to the essence of the report.
Barriers to expand visibility
As I mentioned in my previous blog, organizations with OT assets already have some visibility in OT and are on the way to further expansion. The top three challenges in covering the entire OT environment were:
- Technology limitations on legacy devices and networks :44.8%
- IT staff does not understand OT operational requirements :39.6%
- Traditional IT security technologies are not designed for control systems and cause disruptions in OT environments :37.2%
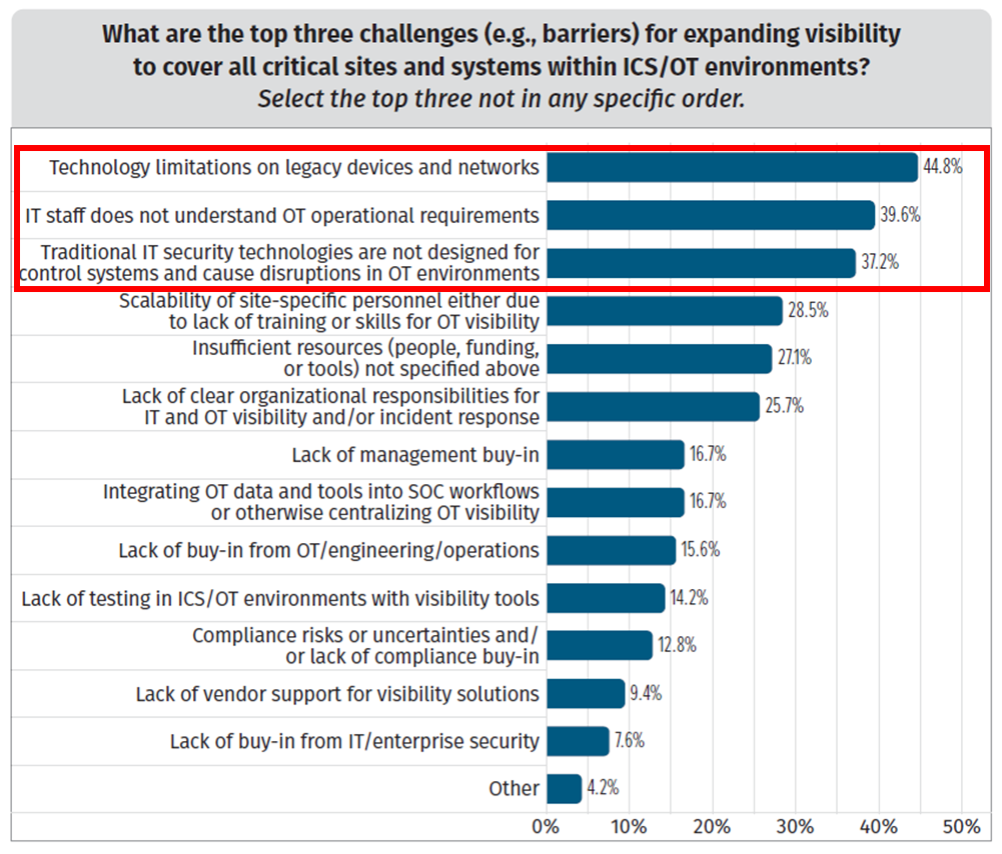
Figure 1: What are the challenges for expanding visibility to cover all OT environments
Given that IT and OT are completely different technologies, the following should be considered to ensure comprehensive visibility across IT and OT and improve organization’s security capabilities.
Barrier #1: Legacy and OT specific security requirement
- Legacy devices and networks are blind spots when it comes to covering the entire OT
- The application of traditional IT security techniques compromises the availability of operations.
Even if your complete inventory of OT assets including legacy, are you keep assessing their risks? It is necessary to check whether preventive measures have been taken to see if vulnerabilities or inadequate configurations remain.
Barrier #2: OT security skill and knowledge
- It will become common for the IT security team to also cope with OT security.
- IT security staff should understand their OT environment and adapt security requirements according to the OT systems.
Giving OT security training to IT security staff is common, and it is also effective to conduct risk assessments in workshops mixed with IT and OT teams. In addition, IT security staff working for OT systems in short term and vice versa, in the form of internships within companies, will also raise the cybersecurity capability from the perspectives of human resources.
Labor intensity: OT security needs too much effort
Besides visibility, the survey also focused on the labor intensity in OT security because it will be necessary to understand the differences between IT and OT security operations and achieve efficient operations totally.
With reference to the NIST CSF security capabilities, we asked participants to rate the labor intensity of each item on a 3-point scale (Low, Medium, High).
As an average of all items, 41.4% answered that OT security is highly labor intensive. Aggregating the five cores of NIST CSF, Respond was the most labor intensive. (50.3%)
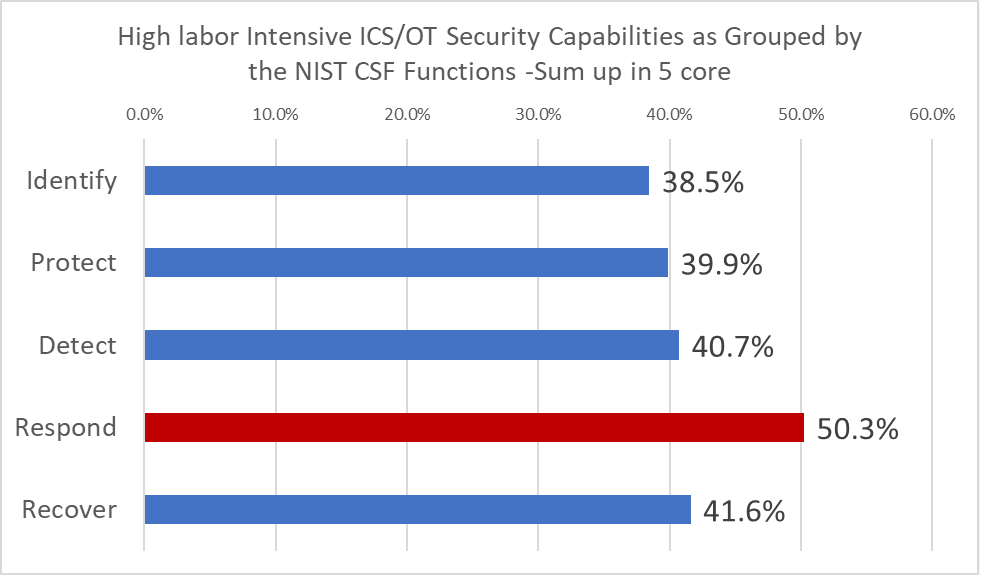
Figure 2: High labor-intensive OT security capabilities (NIST CSF 5 Core)
Furthermore, looking at the specific security capabilities, the score for each function gives:
Cyber incident eradication 54.3%
Cyber incident recovery 47.5%
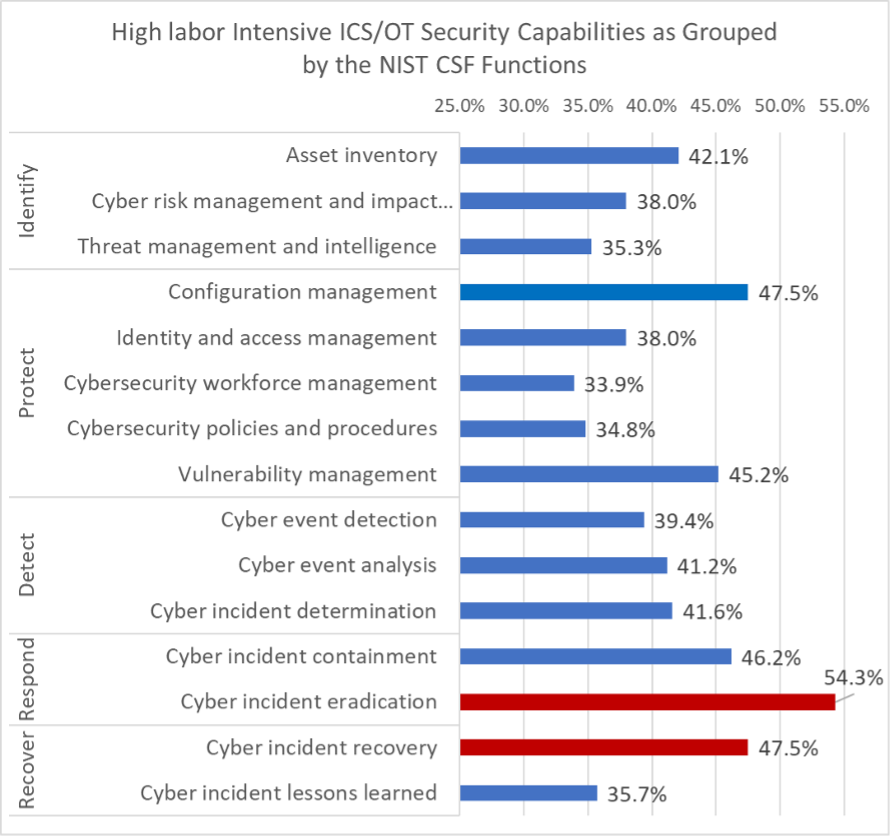
Figure 3: High labor-intensive OT security capabilities (detail)
I think the factors that make these OT security tasks labor intensive include the large number and wide geographic distribution of the assets involved. And as mentioned in my previous blog, the monitoring tools have not covered the entire environment yet. In addition, the fact that on-site confirmation and decision are necessary to ensure safety requires a large human load in response.
OT Incident response
- OT response and recovery require unique processes that are especially conscious of safety and availability.
- On the other hand, since OT incidents often result from attacks on the IT side, it is necessary for IT and OT teams to jointly develop an incident response plan.
The starting point is to discuss beyond the organizational silos of IT and OT what to identify the crown jewels in your organization, what to identify the threats that harm it. Incident response includes process of decision-making because an incident that harms OT is a disruption to the business itself. Greater visibility into what's happening where and how it's impacting your entire network can help you make better decisions. Also, in the response and recovery phases, a platform that allows the IT team and the OT team to see the same information and work together will be required to operate efficiently.
To learn more about how Trend Micro's OT security technologies and platforms can help your security operation process, please visit here.
Reference:
Breaking IT/OT Silos with ICS/OT Visibility - 2023 SANS ICS/OT visibility survey

