TROJ_FOOKBACE.A
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Trojan
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This malicious browser extension is disguised as a Facebook Valentines Theme that affects browsers, one of which is the Google Chrome browser.
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This Trojan may be unknowingly downloaded by a user while visiting malicious websites. It may be manually installed by a user.
TECHNICAL DETAILS
Arrival Details
This Trojan may be unknowingly downloaded by a user while visiting malicious websites.
It may be manually installed by a user.
NOTES:
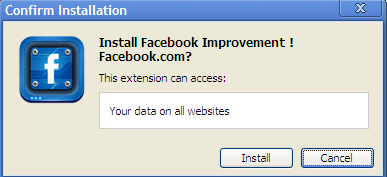
This is Trend Micro's detection for a browser extension which is disguised as a Facebook Valentines Theme that affects Google Chrome browser. Before continuing the installation, Chrome warns the user about the application's access rights.
Upon installation, this application executes a script in the following URL:
- http://{BLOCKED}rs.{BLOCKED}kakkar.com/script.php
- http://{BLOCKED}rs.{BLOCKED}kakkar.com/ad.php
- http://{BLOCKED}rs.{BLOCKED}kakkar.com/ad2.php
After 9 seconds it redirects to:
- http://{BLOCKED}rs.{BLOCKED}kakkar.com/video.php?new
Finally, when the user is logged in to his account, the script automatically 'likes' several pages including:
It may also post a message on friends' Facebook walls:

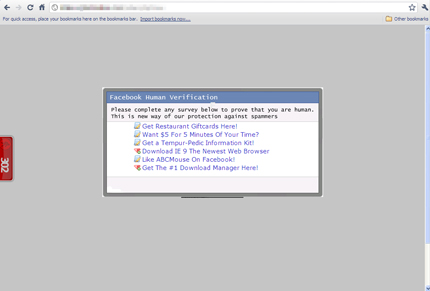
The message, when clicked redirects to this page when clicked:
- http://{BLOCKED}n2test2.{BLOCKED}r.com/?user={user ID}
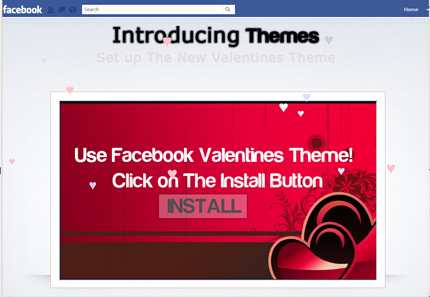
Clicking the image installs the malicious Chrome extension.
SOLUTION
Step 1
Scan your computer with your Trend Micro product to delete files detected as TROJ_FOOKBACE.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 2
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
NOTES:
MANUAL CLEANUP SOLUTION
To manually remove this chrome extension, please follow the steps below:
- Open Google Chrome browser.
- Click the "Customize and Control Google Chrome" button at the top right portion of the browser.
- Go to Tools > Extensions.
- Find "Facebook Improvement ! Facebook.com" and click "Uninstall".
Did this description help? Tell us how we did.

