BKDR_CARBANAK.A
Trojan:Win32/Qadars.A (Microsoft), Backdoor.Win32.Carbanak.n (Kaspersky)
Windows


Threat Type: Backdoor
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This malware is related to the reported attack that hit more than 100 banks and financial institutions located in countries like Russia, US, Ukraine, and countries located in the Asia Pacific region. The said attack began in 2013.
To get a one-glance comprehensive view of the behavior of this Backdoor, refer to the Threat Diagram shown below.
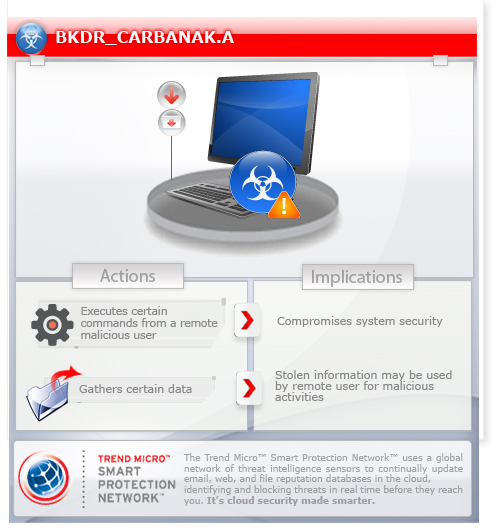
This backdoor executes commands from a remote malicious user such as capturing screenshots and downloading arbitrary files. These routines allow remote attackers to view and manipulate data transacted on the affected computer.
This backdoor may be dropped by other malware.
It executes commands from a remote malicious user, effectively compromising the affected system. It connects to a website to send and receive information.
TECHNICAL DETAILS
Arrival Details
This backdoor may be dropped by the following malware:
Installation
This backdoor injects codes into the following process(es):
- iexplore.exe
Backdoor Routine
This backdoor executes the following commands from a remote malicious user:
- Download arbitrary files
- Download and immediately execute updated copy
- Download and execute updated copy after reboot
- Start SOCKS proxy server
- Stop SOCKS proxy server
- Reboot the system
- Steal cookies
- Delete cookies from browsers
- Uninstall itself
- Download configuration file
- Inject codes to site to monitor sites
- Capture screenshots
It connects to the following websites to send and receive information:
- http://{BLOCKED}.{BLOCKED}.90.193/nbotlogs/debug.php?
It sends information in the following format: ver={version}&uid={UID}&process={process name}&pid={process ID}&level={value}&error={value}&status={value}&time={value}&message={message ID}&counter={value}&left={value}&data={value}
Information Theft
This backdoor gathers the following data:
- OS version
- number of processors
- computer name
- username
- current time
- windows directory
- system directory
- program files directory
- application data directory
- screenshots
NOTES:
This backdoor monitors the following browsers:
- Firefox
- Google Chrome
- Internet Explorer
Its configuration file may contain the sites and processes that it monitors. It may perform any of the following once configuration file is received:
- Capture screenshots upon accessing specific sites
- Inject scripts in specific websites
- Monitor specific processes
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Remove the malware/grayware file dropped/downloaded by BKDR_CARBANAK.A. (Note: Please skip this step if the threat(s) listed below have already been removed.)
Step 3
Restart in normal mode and scan your computer with your Trend Micro product for files detected as BKDR_CARBANAK.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.



