BBOS_ZITMO.B
BlackBerry OS


Threat Type: Spyware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This spyware is flagged as noteworthy as it targets BlackBerry phone users.
To get a one-glance comprehensive view of the behavior of this Spyware, refer to the Threat Diagram shown below.
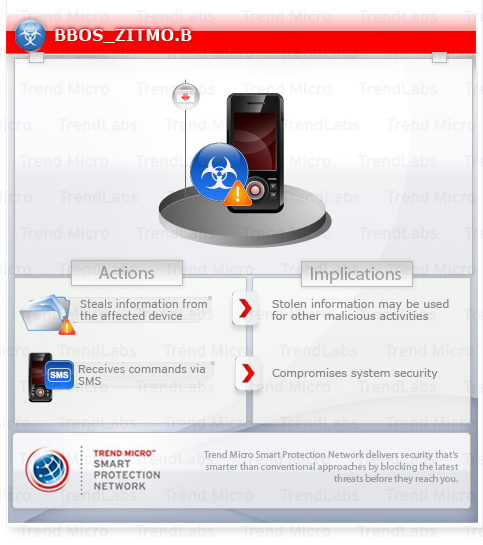
It sends notification to a UK number upon successful installation. It also monitors incoming calls and SMS. It adds a database to the phone that may contain a list of users and administrators for the app. It has a stealth mechanism that prevents being seen as an installed app.
It may receive commands via SMS. Its objective is to steal user information by forwarding SMS messages to a set/predefined admin number.
It is a counterpart of SYMBOS_ZBOT.B and WINCE_ZBOT.B, which are malware for devices running on Symbian OS and Windows Mobile, respectively. It is also a counterpart of TSPY_ZBOT.HQ, a Windows OS malware.
This spyware arrives as a component bundled with malware/grayware packages.
TECHNICAL DETAILS
Arrival Details
This spyware arrives as a component bundled with malware/grayware packages.
Other Details
This spyware does the following:
- Performs the following actions:
- Add a database to the infected phone that may contain a list of users and administrators for the app
- Monitor incoming calls and SMS
- Operated in stealth mode to prevents being seen as an installed app
- Send notification to the UK number, +447{BLOCKED} on successful installation
- Receives the following commands via SMS:
- Add sender
- Block
- Rem (remove) sender
- Set admin
- Set sender
- Steals user information by forwarding SMS messages to a set/defined admin number
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Scan your computer with your Trend Micro product to delete files detected as BBOS_ZITMO.B. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
NOTES:
If you recently connected your smartphone to your Windows PC, please do the aforementioned cleanup step.
Did this description help? Tell us how we did.


