WORM_OTORUN.ASH
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Worm
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This worm poses as a font file and uses the LNK vulnerability to propagate. There has also been an increase in customer infection because of this malware.
To get a one-glance comprehensive view of the behavior of this Worm, refer to the Threat Diagram shown below.
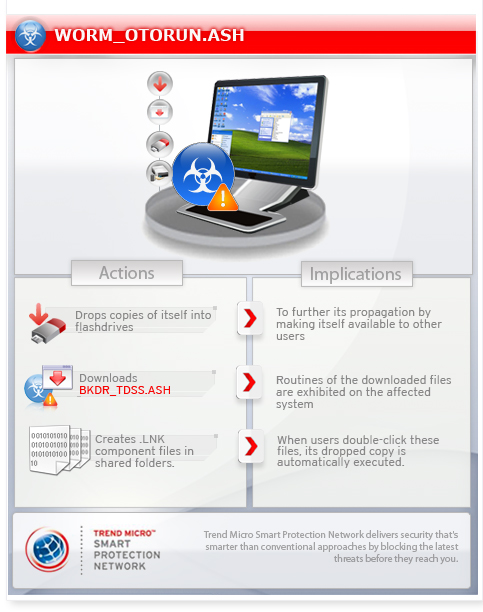
It also creates .LNK component files in shared folders. When users double-click these files, its dropped copy is automatically executed.
Trend Micro detects the said shortcut files either as LNK_OTORUN.SM or EXPL_CPLNK.SM, depending on the malware copy that it points to. If the shortcut file points to a local malware copy, it is detected as LNK_OTORUN.SM. But if it points to a remote malware copy, it is detected as EXPL_CPLNK.SM.
It searches for all shared folders on the affected system. It then drops copies of itself to the found folders using a certain file name.
Trend Micro detects the dropped AUTORUN.INF file as TROJ_OTORUN.SMF.
This worm arrives via removable drives. It may be downloaded by other malware/grayware/spyware from remote sites. It may be dropped by other malware.
It adds key(s)/entry(ies) to allow itself to run on safe mode. This action adds difficulty in the removal of this malware from the affected computer.
It drops copies of itself in all removable drives. It exploits software vulnerabilities to propagate to other computers across a network.
It connects to certain URLs. It may do this to remotely inform a malicious user of its installation. It may also do this to download possibly malicious files onto the computer, which puts the computer at a greater risk of infection by other threats. It executes the downloaded files. As a result, malicious routines of the downloaded files are exhibited on the affected system.
It does not have any information-stealing capability.
It deletes the initially executed copy of itself.
TECHNICAL DETAILS
Arrival Details
This worm arrives via removable drives.
It may arrive via network shares.
It may be downloaded by other malware/grayware/spyware from remote sites.
It may be dropped by other malware.
It may be downloaded from the following remote sites:
- http://{BLOCKED}9.88.8/spr.dll
Installation
This worm drops the following copies of itself into the affected system:
- %User Temp%\srv{random characters}.tmp
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003.)
It drops the following non-malicious file:
- %User Temp%\srv{Random Characters}.ini - configuration file
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003.)
It injects itself into the following processes running in the affected system's memory:
- spoolsv.exe
Autostart Technique
This worm registers itself as a system service to ensure its automatic execution at every system startup by adding the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\srv{random characters}
Type = "20"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\srv{random characters}
Start = "2"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\srv{random characters}
ErrorControl = "1"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\srv{random characters}
ImagePath = "%System Root%\system32\svchost.exe -k netsvcs"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\srv{random characters}
DisplayName = "srv{random characters}"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\srv{random characters}
ObjectName = "LocalSystem"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\srv{random characters}\parameters
servicedll = "\?\globalroot\Device\HarddiskVolume1\%User Temp%\srv{numbers}.tmp"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\srv{random characters}\Security
Security = "{hex values}"
It adds the following key(s)/entry(ies) to allow itself to run on safe mode:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Control\SafeBoot\Minimal\
srv{Random Characters}
Other System Modifications
This worm modifies the following registry key(s)/entry(ies) as part of its installation routine:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\SvcHost
netsvcs = "{Default Data} srv{Random Characters}"
(Note: The default value data of the said registry entry is {Default Data}.)
HKEY_USERS\.DEFAULT\Software\
Microsoft\Windows\CurrentVersion\
Internet Settings\Zones\3
CurrentLevel = "0"
(Note: The default value data of the said registry entry is 11000.)
HKEY_USERS\.DEFAULT\Software\
Microsoft\Windows\CurrentVersion\
Internet Settings\Zones\3
1601 = "0"
(Note: The default value data of the said registry entry is 1.)
It creates the following registry entry(ies) to bypass Windows Firewall:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\ SharedAccess\Parameters\
FirewallPolicy\StandardProfile\GloballyOpenPorts\
List
67:UDP = "67:UDP:*:Enabled:DHCP Server"
Propagation
This worm drops copies of itself in all removable drives.
The said .INF file contains the following strings:
;{garbage characters}
[AutoRun]
AcTIOn=opeN
;{garbage characters}
IcON=%Windows%\SYstEm32\ShelL32.DLl,4
;{garbage characters}
UsEaUtoPlAy=1
;{garbage characters}
oPEN=RUNDLl32.EXe sETup{numbers}.foN,{parameters}
;{garbage characters}
SHElL\eXPLore\ComManD=ruNDLL32.EXe setup{numbers}.fON,{parameters}
;{garbage characters}
SHelL\Open\cOmmaNd=rundLL32.EXE sETUP{numbers}.fON,{parameters}
;{garbage characters}
(Note: %Windows% is the Windows folder, which is usually C:\Windows or C:\WINNT.)
It exploits the following software vulnerabilities to propagate to other computers across a network:
Download Routine
This worm connects to the following malicious URLs:
- http://{BLOCKED}.{BLOCKED}.49.103/sknock.php?affid={parameter}&data=version={parameter}|{infection information}
- http://{BLOCKED}.{BLOCKED}.112.138/service/listener.php?affid={Parameter}
- http://{BLOCKED}.{BLOCKED}.123.34/service/scripts/files/aff_50039.dll - inaccessible
- http://{BLOCKED}.{BLOCKED}.123.33/service/listener.php?affid=50039 - inaccessible
It accesses the following websites to download files:
- http://{BLOCKED}8.{BLOCKED}2.189.105/service/listener.php?affid={numbers} - inaccessible
- http://{BLOCKED}8.{BLOCKED}2.189.105/service/scripts/files/aff_{numbers}.dll - inaccessible
- http://{BLOCKED}9.{BLOCKED}5.49.103/srv - configuration file
- http://{BLOCKED}9.{BLOCKED}5.49.103/dll - inaccessible
- http://{BLOCKED}9.{BLOCKED}5.49.103/exe - inaccessible
- http://{BLOCKED}5.{BLOCKED}4.112.136/dll - inaccessible
- http://{BLOCKED}5.{BLOCKED}4.112.136/srv - Configuration File
- http://{BLOCKED}5.{BLOCKED}4.112.136/exe - Copy of itself
- http://{BLOCKED}5.{BLOCKED}4.112.138/X - Copy of itself
- http://{BLOCKED}5.{BLOCKED}4.112.139/service/scripts/files/aff_{parameter}.dll - BKDR_TDSS.KARU
- http://{BLOCKED}.{BLOCKED}.210.72/service/listener.php?affid=50045 - inaccessible
- http://{BLOCKES}.{BLOCKED}.210.72//srv - inaccessible
- http://{BLOCKED}.{BLOCKED}.162.20/service/scripts/files/aff_50045.dll - BKDR_TDSS.ASH
- http://{BLOCKED}.{BLOCKED}.210.72/X - updated copy of itself
- http://{BLOCKED}.{BLOCKED}.210.72//dll - inaccessible
- http://{BLOCKED}4.{BLOCKED}0.123.34//srv – inaccessible
- http://{BLOCKED}4.{BLOCKED}0.123.34/service/scripts/files/aff_50045.dll - detected as BKDR_TDSS.ASH
- http://{BLOCKED}4.{BLOCKED}0.123.34//dll – inaccessible
- http://{BLOCKED}9.88.7/X - detected as BKDR_TDSS.ASH
- http://{BLOCKED}9.88.7/srv.dat - encrypted configuration file
- http://{BLOCKED}.{BLOCKED}.123.34/X - inaccessible
- http://{BLOCKED}8.{BLOCKED}9.89.121/X – detected as TROJ_KRYPTK.SMUH
- http://{BLOCKED}8.{BLOCKED}9.89.121/exe – inaccessible
It saves the files it downloads using the following names:
- %User Temp%\srv{Random Characters}.tmp
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003.)
It then executes the downloaded files. As a result, malicious routines of the downloaded files are exhibited on the affected system.
Information Theft
This worm does not have any information-stealing capability.
Other Details
This worm deletes the initially executed copy of itself
NOTES:
It also creates the following .LNK component files in shared folders. When users double-click these files, its dropped copy is automatically executed:
- autorun.inf
- myporno.avi.lnk
- pornmovs.lnk
- setup{number}.lnk
Trend Micro detects the said shortcut files either as LNK_OTORUN.SM or EXPL_CPLNK.SM, depending on the malware copy that it points to. If the shortcut file points to a local malware copy, it is detected as LNK_OTORUN.SM. But if it points to a remote malware copy, it is detected as EXPL_CPLNK.SM.
It searches for all shared folders on the affected system. It then drops the following copies of itself to the found folders using the following file name:
- setup{numbers}.fon
Trend Micro detects the dropped AUTORUN.INF file as TROJ_OTORUN.SMF.
This malware modifies the DNS settings of the affected machine by configuring it as a DHCP server with the DNS set to {BLOCKED}9.88.7 and {BLOCKED}.{BLOCKED}.88.8.
It may also delete registries related to the system's DNS settings.
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Remove malware files dropped/downloaded by WORM_OTORUN.ASH
Step 3
Identify and delete files detected as WORM_OTORUN.ASH using either the Startup Disk or Recovery Console
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\GloballyOpenPorts\List
- 67:UDP = "67:UDP:*:Enabled:DHCP Server"
- 67:UDP = "67:UDP:*:Enabled:DHCP Server"
Step 5
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal
- srv{Random Characters}
- srv{Random Characters}
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services
- srv{Random Characters}
- srv{Random Characters}
Step 6
Restore this modified registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SvcHost
- From: netsvcs = "{Default Data} srv{Random Characters}"
To: netsvcs = "{Default Data}"
- From: netsvcs = "{Default Data} srv{Random Characters}"
- In HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\3
- From: CurrentLevel = "0"
To: CurrentLevel = "11000"
- From: CurrentLevel = "0"
- In HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\3
- From: 1601 = "0"
To: 1601 = "1"
- From: 1601 = "0"
Step 7
Search and delete this file
- %User Temp%\srv{random}.ini
Step 8
Search and delete AUTORUN.INF files created by WORM_OTORUN.ASH that contain these strings
;{garbage characters}
[AutoRun]
AcTIOn=opeN
;{garbage characters}
IcON=%Windows%\SYstEm32\ShelL32.DLl,4
;{garbage characters}
UsEaUtoPlAy=1
;{garbage characters}
oPEN=RUNDLl32.EXe sETup{numbers}.foN,{parameters}
;{garbage characters}
SHElL\eXPLore\ComManD=ruNDLL32.EXe setup{numbers}.fON,{parameters}
;{garbage characters}
SHelL\Open\cOmmaNd=rundLL32.EXE sETUP{numbers}.fON,{parameters}
;{garbage characters}
Step 9
Scan your computer with your Trend Micro product to delete files detected as WORM_OTORUN.ASH. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 10
Download and apply these security patches Refrain from using these products until the appropriate patches have been installed. Trend Micro advises users to download critical patches upon release by vendors.
NOTES:
Recommendations:
- Since this malware spreads via network shares, machines that are affected should immediately be removed from the network.
- Enable scanning of network drives on your Trend Micro product to remove malware that may spread to network drives.
- Avoid accessing the listed malicious URLs to prevent possible re-infection.
- The latest Trend Micro product pattern and engine removes this malware. Always keep pattern files and engine are up-to-date.
Did this description help? Tell us how we did.



