TSPY_PASSTEAL.A
Trojan.Win32.Pakes (Ikarus), W32/Dapato.BNYX!tr (Fortinet)
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Spyware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This malware was seen to include a password recovery tool that steals information stored in browsers.
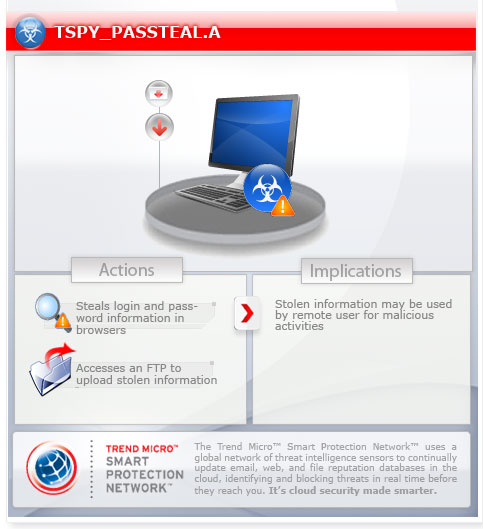
To get a one-glance comprehensive view of the behavior of this Spyware, refer to the Threat Diagram shown below.
For the related story, you may read the blog post HTTPS, SSL No Match for PASSTEAL Malware.
This spyware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Arrival Details
This spyware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This spyware drops the following files:
- %User Temp%\{random}.exe (also detected as TSPY_PASSTEAL.A)
- %User Temp%\cvtres.exe
- %System Root%\DOCUMENTS
- %User Profile%\Application Data\{computer name}.txt (stolen credentials)
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local\Temp on Windows Vista and 7.. %System Root% is the root folder, which is usually C:\. It is also where the operating system is located.. %User Profile% is the current user's profile folder, which is usually C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003, or C:\Users\{user name} on Windows Vista and 7.)
Drop Points
This spyware uploads files to the following File Transfer Protocol (FTP) sites:
- ftp://{BLOCKED}.{BLOCKED}.67.232
NOTES:
This spyware steals user names and password stored in the Firefox browser.
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product and note files detected as TSPY_PASSTEAL.A
Step 3
Restart in Safe Mode
Step 4
Search and delete files detected as TSPY_PASSTEAL.A
Step 5
Search and delete these files
- %User Temp%\cvtres.exe
- %System Root%\DOCUMENTS
- %User Profile%\Application Data\{computer name}.txt
Step 6
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TSPY_PASSTEAL.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

