TROJ_FLASHUP.B
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
The malicious files <i>flash32.exe</i> and <i>kbflashUpd.dll</i> are detected as TROJ_FLASHUP.A and TROJ_FLASHUP.B, respectively. These are the downloaded payloads of TROJ_NETISON.AB. The malware TROJ_NETISON.AB is the payload from the Adobe Flash zero-day vulnerability CVE-2015-5119.
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
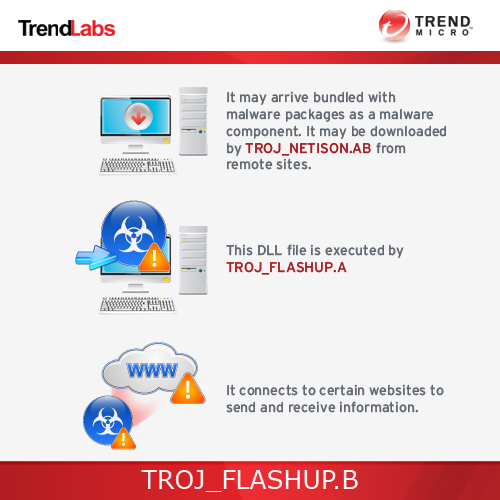
This Trojan may arrive bundled with malware packages as a malware component. It may be downloaded by other malware/grayware from remote sites.
It connects to certain websites to send and receive information.
TECHNICAL DETAILS
Arrival Details
This Trojan may arrive bundled with malware packages as a malware component.
It may be downloaded by the following malware/grayware from remote sites:
- TROJ_NETISON.AB
Installation
This Trojan adds the following mutexes to ensure that only one of its copies runs at any one time:
- Windows Update System Verifier
It is injected into the following processes running in memory:
- dwm.exe
- wuauclt.exe
- ctfmon.exe
- wscntfy.exe
It terminates itself if it finds the following processes in the affected system's memory:
- regmon.exe
- filemon.exe
- procMon.exe
Other Details
This Trojan connects to the following URL(s) to check for an Internet connection:
- www.update.microsoft.com
It connects to the following website to send and receive information:
- http://{BLOCKED}esstea.com/page2/oneclick.php?max-width={value}
- http://{BLOCKED}esstea.com/page2/oneclick.php?ads_id={value}&rparam={encrypted data}-{Computer Name}-{Version}-{encrypted data}
- http://{BLOCKED}esstea.com/page2/oneclick.php?cat_id={value}
NOTES:
This DLL file is executed by TROJ_FLASHUP.A
This Trojan searches for the following files and executes them if it exists:
- %Application Data%\microsoft\common\iecache32.exe
- %Application Data%\microsoft\common\iecookie.exe
- %Application Data%\microsoft\common\upx32.dll
- %Application Data%\microsoft\common\dllhosts.exe
It searches files in the folder %Application Data%\adobe\reader\temp. If files exists, it encrypts the file and sends it to the site http://{BLOCKED}esstea.com/page2/oneclick.php?cat_id={value}. It then deletes the file afterwards.
It creates the following processes and injects flash32.exe:
- %System%\cipher.exe
- %System%\gpupdate.exe
- %System%\services.exe
- %System%\sppsvc.exe
- %System%\winrshost.exe
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Remove the malware/grayware file dropped/downloaded by TROJ_FLASHUP.B. (Note: Please skip this step if the threat(s) listed below have already been removed.)
- TROJ_NETISON.AB
Step 3
Scan your computer with your Trend Micro product to delete files detected as TROJ_FLASHUP.B. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


