SWF_EXPLOYT.YYKI
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This is the detection for the exploit that targets the Adobe zero-day vulnerability covered in CVE-2015-5119. The said vulnerability affects the latest versions of Flash on Windows, Mac, and Linux. Accordingly, various exploit kits such as Nuclear Exploit Pack, Neutrino Exploit Kit, and Angler Exploit Kit have integrated the Hacking team Flash zero-day.
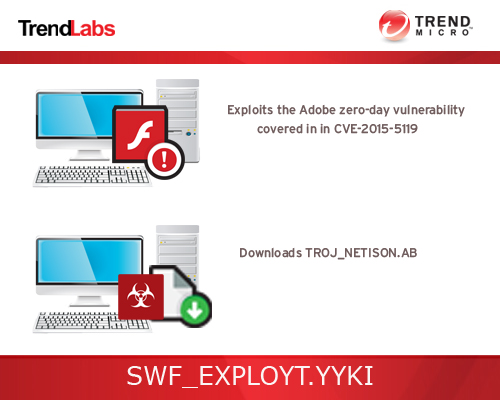
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This Trojan is a component of other malware.
It executes the downloaded files. As a result, malicious routines of the downloaded files are exhibited on the affected system.
TECHNICAL DETAILS
Arrival Details
This Trojan may be downloaded from the following remote sites:
- http://{BLOCKED}360.com/img_h/ims2/icon.swf
Installation
This Trojan is a component of other malware.
Download Routine
This Trojan connects to the following website(s) to download and execute a malicious file:
- http://{BLOCKED}360.com/img_h/ims2/icon.jpg
It saves the files it downloads using the following names:
- %User Temp%\RealTemp.exe - detected as TROJ_NETISON.AB
(Note: %User Temp% is the user's temporary folder, where it usually is C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local\Temp on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
It then executes the downloaded files. As a result, malicious routines of the downloaded files are exhibited on the affected system.
Other Details
This Trojan is a zero-day exploit for the following vulnerability:
NOTES:
There is no patch for this vulnerability, yet at the time of writing. Please refer to the link specified above for the software updates.
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Close all opened browser windows
Step 3
Remove the malware/grayware file dropped/downloaded by SWF_EXPLOYT.YYKI. (Note: Please skip this step if the threat(s) listed below have already been removed.)
- TROJ_NETISON.AB
Step 4
Scan your computer with your Trend Micro product to delete files detected as SWF_EXPLOYT.YYKI. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


