BKDR_GATAKA.A
Trojan:Win32/Gataka.D (Microsoft); PWS-Zbot.gen.ahw( McAfee); Trojan-Spy.Win32.Zbot.eomj (Kaspersky)
Windows 2000, Windows Server 2003, Windows XP (32-bit, 64-bit), Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Backdoor
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This malware has the capability of downloading and installing plugins from a remote server. This feature allows the malware to be more flexible in its attacks. Affected users may find their personal information stolen due to the security of their systems being compromised.
To get a one-glance comprehensive view of the behavior of this Backdoor, refer to the Threat Diagram shown below.
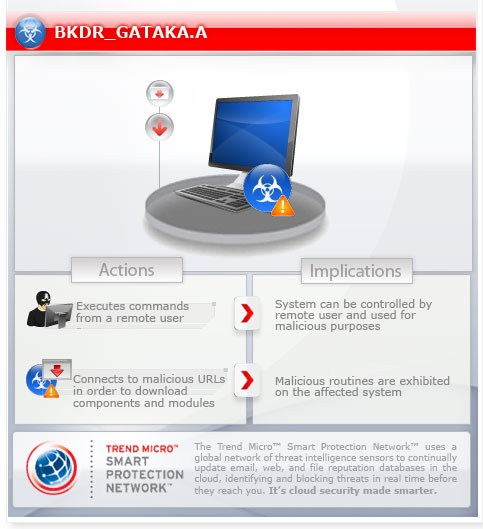
This backdoor collects system information and remotely execute arbitrary commands or other applications.
This backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It executes commands from a remote malicious user, effectively compromising the affected system. However, as of this writing, the said sites are inaccessible.
It opens a hidden Internet Explorer window. It deletes the initially executed copy of itself.
TECHNICAL DETAILS
Arrival Details
This backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This backdoor drops the following copies of itself into the affected system:
- %Application Data%\{folder name 1}\{CLSID 1}\{malware file name}.exe
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Roaming on Windows Vista and 7.)
It drops the following component file(s):
- %Application Data%\{folder name 2}\{CSLID 2}\{random hex}.dat - non-malicious file
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Roaming on Windows Vista and 7.)
It creates the following folders:
- %Application Data%\{folder name 1}\{CLSID 1}
- %Application Data%\{folder name 2}\{CSLID 2}
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Roaming on Windows Vista and 7.)
It injects codes into the following process(es):
- explorer.exe
Autostart Technique
This backdoor adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
{malware file name} = "%Application Data%\{folder name 1}\{CLSID 1}\{malware file name}.exe"
Other System Modifications
This backdoor adds the following registry entries as part of its installation routine:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
StartProcIrq = "dword:0000000c"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
StartPage
CustomBarMenu = "{encrypted location of {random hex}.dat}"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
StartCurrId = "dword:00000009"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
StartCurrMask = "dword:0000003e"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
StartMainId = "dword:0000000a"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
StartMainMask = "dword:0000007e"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
PersistFile = "dword:00000003"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
PersistFolder = "dword:00000002"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
StartMenuMask = "dword:00015be1"
Backdoor Routine
This backdoor executes the following commands from a remote malicious user:
- Collect System Information
- Browse Files and Folders
- Connect to Server
- Get AutoRun FilePath
- Get AutoRun ValueName
- Get Bot Id
- Download and Install plugins/modules
- Open Browser
- Perform remote shell
- Download and execute arbitrary files
- Set AutoRun Value
- Start As Client
- Start As Server
- Stop Client
- Stop Server
- Terminate itself
It connects to the following URL(s) to send and receive commands from a remote malicious user:
- {BLOCKED}-summer.hu/ip.php
- {BLOCKED}ly.com/ip.php
- dns.{BLOCKED}g.cc/mak/g.php
- {BLOCKED}rve.name/mak/g.php
However, as of this writing, the said sites are inaccessible.
Information Theft
This backdoor injects itself into the following web browsers to monitor searches made by the user on the following search engines:
- iexplore.exe
- maxthon.exe
- opera.exe
- firefox.exe
- sol.exe
Other Details
This backdoor opens a hidden Internet Explorer window.
It deletes the initially executed copy of itself
NOTES:
The {folder name} and {malware file name} can be any of the following:
- Adobe
- Apple
- Dropbox
- Google Inc
- Identities
- LicenseValidator
- Macromedia
- Media Center Programs
- Media Player Classic
- Microsoft
- Microsoft Corporation
- Mozilla
- NtCoreDefender
- NtGarbageCollector
- Opera
- RdcRpcController
- renovator
- RpcLowAccessPipe
- RpcLowReader
- RpcNtComm
- RpcScheduler
- RpcSearchIndexer
- RpcWin32Router
- RpcWin32Service
- SearchHelper
- Skype
- TeamViewer
- Upgrade
- UpgradeChecker
- UpgradeHelper
- Validator
- Win16Communicator
- Win32Defender
- Win32GlobalFinder
- Win32RpcAccessCtrl
- Win32RpcDecrypt
- Win32Scheduler
- Win32UserFinder
- Win64Expected
- Win64GarbageCollector
- Windows Desktop Search
- Windows Search
- WindowsRpcAccess
- WinRAR
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product and note files detected as BKDR_GATAKA.A
Step 3
Restart in Safe Mode
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- {malware file name} = "%Application Data%\{folder name 1}\{CLSID 1}\{malware file name}.exe"
- {malware file name} = "%Application Data%\{folder name 1}\{CLSID 1}\{malware file name}.exe"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- StartProcIrq = "dword:0000000c"
- StartProcIrq = "dword:0000000c"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\StartPage
- CustomBarMenu = "{encrypted location of {random hex}.dat}"
- CustomBarMenu = "{encrypted location of {random hex}.dat}"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- StartCurrId = "dword:00000009"
- StartCurrId = "dword:00000009"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- StartCurrMask = "dword:0000003e"
- StartCurrMask = "dword:0000003e"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- StartMainId = "dword:0000000a"
- StartMainId = "dword:0000000a"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- StartMainMask = "dword:0000007e"
- StartMainMask = "dword:0000007e"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- PersistFile = "dword:00000003"
- PersistFile = "dword:00000003"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- PersistFolder = "dword:00000002"
- PersistFolder = "dword:00000002"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- StartMenuMask = "dword:00015be1"
- StartMenuMask = "dword:00015be1"
Step 5
Search and delete these folders
- %Application Data%\{folder name 1}\{CLSID 1}
- %Application Data%\{folder name 2}\{CSLID 2}
Step 6
Restart in normal mode and scan your computer with your Trend Micro product for files detected as BKDR_GATAKA.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


