ANDROIDOS_DORDRAE.N
TrojanSpy:AndroidOS/DDLight.B (Microsoft); Trojan-Downloader.AndroidOS.DorDrae.ai (Kaspersky)
Information Stealer, Malicious Downloader
Android OS


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This is the new variant of DroidDreamLight that exhibits information theft routines. It also guises itself as apps like battery-monitoring tool, a task-listing tool, and an app listing the permissions used by installed apps.
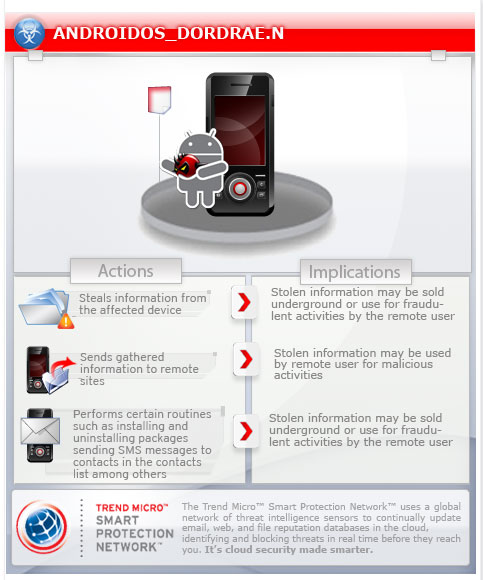
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This malware arrives via Trojanized Android applications.
This is Trend Micro's detection for Trojanized Android applications. While the legitimate software runs, it silently executes malicious code in the background. Upon execution of the affected application, the malware starts gathering certain information.
It sends these information to certain remote servers.
This Trojan may be manually installed by a user.
TECHNICAL DETAILS
Arrival Details
This Trojan may be manually installed by a user.
This malware arrives via the following means:
- Via Trojanized Android applications
NOTES:
This is Trend Micro's detection for Trojanized Android applications. While the legitimate software runs, it silently executes malicious code in the background. Upon execution of the affected application, the malware starts gathering the following information:
- IMEI
- IMSI
- Installed app information
- Language setting
- Package name of the trojanized app
- Phone model
- SDK version
It sends these information to the following remote servers:
- http://{BLOCKED}cdoo.com/wmzq.jsp
- http://{BLOCKED}eety.com/vrzl.jsp
It also steals information from the affected device such as:
- Call log (incoming/outgoing)
- Contacts lists
- Google accounts
- SMS messages (inbox/outbox content)
The information is saved and compressed in the /data/data/%package name%/files directory. These are then uploaded to any of the following URLs:
- http://{BLOCKED}ead.com
- http://{BLOCKED}yed.com
Based on the analysis of the codes, it also has the following routines:
- Check if the affected device has been rooted
- Insert a message entry in the inbox with the sender and body specified by the malicious author
- Install and uninstall packages
- Send SMS messages to contacts in the contacts list
SOLUTION
Step 1
Trend Micro Mobile Security Solution
Trend Micro Mobile Security Personal Edition protects Android smartphones and tablets from malicious and Trojanized applications. The App Scanner is free and detects malicious and Trojanized apps as they are downloaded, while SmartSurfing blocks malicious websites using your device's Android browser.
Download and install the Trend Micro Mobile Security App via Google Play.
Step 2
Remove unwanted apps on your Android mobile device
Did this description help? Tell us how we did.


