
Ransomware is malware that encrypts important files on local and network storage and demands a ransom to decrypt the files. Hackers develop this malware to make money through digital extortion.
Ransomware is encrypted, so the key cannot be forced and the only way to recover the information is from a backup.
The way ransomware works makes it especially damaging. Other types of malware destroy or steal data but leave other recovery options open. With ransomware, if there are no backups, you must pay the ransom to recover the data. Sometimes businesses pay the ransom, and the attacker does not send the decryption key.
Table of Contents
Ransomware targets important information
Once the ransomware starts to work, it scans local and network storage, looking for files to encrypt. It targets files it assumes are important to your business or to individuals. This includes backup files that could help recover the information. Following are a few file types ransomware targets:
- Microsoft Office: .xlsx, .docx, and .pptx plus older versions
- Image: .jpeg, .png, .jpeg, .gif
- Business-related images: .dwg
- Data: .sql and .ai
- Video: .avi, .m4a, .mp4
Different types of ransomware target different sets of files, but there are also common targets. Most ransomware targets Microsoft Office files because they often store critical business information. Targeting important files increases the chance that you will pay the ransom.
Phishing emails often contain ransomware
Ransomware is different from other malware because of what it does after it activates. It usually executes when a user opens an attachment or clicks on a link in a phishing email. The malware then downloads from an attacker-controlled server.
After ransomware downloads, it can stay dormant on your network drive or run directly on an infected computer. When it runs, it scans available local and network storage systems for targeted file extensions and encrypts them. Encryption is either asymmetric or symmetric, but many recent ransomware attacks use both.
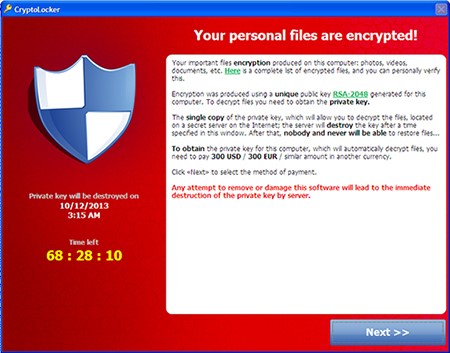
Attackers demand payment
An attacker always demands payment in cryptocurrency, mainly Bitcoin. Taking payments this way reduces the risk of being caught. Attackers also use servers behind TOR, an anonymity network, to avoid being identified.
After the ransomware encrypts the files, it displays a message to your business. The attackers demand payment in exchange for keys to unlock the files. The ransom can be a few hundred dollars or a few million. If you do not not pay right away, the malware increases the ransom.
Some ransomware attacks feature double extortion. The attacker demands a fee to release the files. It also posts a list of organizations that were attacked but refused to pay. Double extortion further motivates the you to pay the ransom and avoid damage to your brand.
Ransomware is evolving
There are variations of ransomware that differ in how they encrypt data and stop users from getting the decryption key. Older ransomware used client or server asymmetric encryption or simple symmetric encryption. Newer ransomware combines the two to increase an attack’s effectiveness.
Symmetric encryption
Ransomware hackers today rarely use symmetric encryption alone. Symmetric encryption by itself uses a single key for encryption and decryption. The key is often stored on the local system. There, specialists and researchers can find it and decrypt the data without paying the ransom. To resolve this issue, hackers now more commonly use hybrid cryptography.
Client-side asymmetric encryption
Asymmetric encryption uses a public key to encrypt data, and a separate, private key to decrypt it. One common encryption method is RSA cryptography, which HTTPS also uses. RSA is slower than symmetric encryption, and all files must be encrypted before the attacker can send the private key to the server.
The software finishes encrypting, sends the private key to the attacker’s server, and deletes it from local storage. The risk is that the computer goes offline before encryption is complete. In that case, the private key is never transferred to the attacker’s server. The attacker is then unable to demand a ransom.
Server-side asymmetric encryption
Server-side asymmetric encryption solves the problem of client-side encryption by encrypting files when the computer comes online. The attacker’s server generates a private / public key pair and encrypts files with the server’s public key.
When you pay the ransom, the attacker transfers the private key for decryption. The risk to the attacker is that when the private key transfers, you can intercept and get the key. The risk to the attacker is that when the private key transfers, you can intercept and get the key, which can then be shared with other affected businesses, making the ransomware useless.
Hybrid encryption
Hackers discovered that the earlier versions of ransomware were vulnerable, so they designed hybrid versions. In the hybrid versions, the software generates two sets of keys, and a chain of encryption solves the issues with the older versions. The chain of encryption works like this:
- The symmetric key encrypts files.
- The software generates a client-side key pair. The client-side public key encrypts the symmetric key file.
- The software generates a server-side key pair. The server-side public key encrypts the client-side private key, and it then goes to the attacker.
- When you pay the ransom, the server-side private key decrypts the client-side private key, and this key goes to your business where the encryption chain reverses.
Prevent ransomware with backups
The best way to protect against ransomware is with backups. Backup files stored locally or on a network drive are vulnerable. Cloud storage is protected from ransomware network scans, so it is a good solution for recovery. An exception is if you map cloud storage as a local drive or subfolder.
To prevent ransomware damage, it is best to stop it before it starts. Most attacks start when users unintentionally download the software directly or run a malicious script by accident.
Two ways to stop users from downloading ransomware are DNS-based content filtering and email cybersecurity that incorporates artificial intelligence quarantining. DNS-based content filtering stops users from browsing blacklisted websites. Email filters send malicious content and attachments to quarantine for administrator review.
Finally, always run anti-malware software with machine learning and behavior monitoring on every device including mobile. A good anti-malware application detects ransomware before it can access memory and encrypt files. For greatest effectiveness, anti-malware software must always be patched and up to date so it can recognize the latest threats.
Ransomware attacks affect thousands
Ransomware attacks affect thousands of users globally. In some cases, even after victims think the ransomware is contained, it can continue to cause issues. Anti-malware programs catch many older versions, but hackers continually develop new types to avoid detection.
For instance, in 2018 and 2019, Ryuk ransomware disabled Windows System Restore functionality. Users were then unable to recover from a previous restore point in the operating system. Because it targeted businesses, Ryuk demanded hundreds of thousands of dollars in ransom.
CryptoLocker, WannaCry, and Petya were all different forms of ransomware that caused global infrastructure shutdowns, affecting even banks and government agencies. WannaCry, in particular, targeted Windows machines and used an exploit developed by the United States National Security Agency (NSA) to scan open network drives and encrypt vulnerable files.
Ransomware threats that persist include Gandcrab, SamSam, Zeppelin, and REvil. While these variants are newer, they still persist as dangerous malware with the ability to destroy corporate systems.
Ransomware continues to be a threat
Ransomware targets businesses of any size, crippling your organization if no backups are available. Understanding the way ransomware works and how it can affect your business helps you better defend against it. The best way to stop an attack is to educate users, run anti-malware on all devices, and stop users from accessing malicious email messages.
Fernando Cardoso is the Vice President of Product Management at Trend Micro, focusing on the ever-evolving world of AI and cloud. His career began as a Network and Sales Engineer, where he honed his skills in datacenters, cloud, DevOps, and cybersecurity—areas that continue to fuel his passion.

