Ransomware Spotlight: Hive
Overview of Hive’s operations
Hive operations are more prolific than their leak site might suggest. HiveLeaks only publishes the list of victims that have not settled the ransom, so it is tough to determine which — or how many — companies decided to pay the ransom. A report indicates that attack attempts by Hive affiliates hit an average of three companies per day since the group was first discovered in June 2021. The report also mentioned that security researchers who got access to information directly from the administrator panel of the Hive Tor site discovered that the number of enterprises whose systems had been compromised have reached 355 from September to December 2021.
Intelligence gathered by the researchers further revealed that the founders of the group deliberately put systems in place to achieve as much ease and transparency as possible particularly in the process of ransomware deployment and negotiations. Researchers also learned that the generation of malware versions by affiliates can be done within 15 minutes, while negotiations are coursed through the Hive ransomware administrators who relay the message to the victims in a chat window that the affiliates can see.
Researchers also shared that affiliates can see on the Hive administrator panel how much money was collected, the list of companies that paid, and those whose information was leaked.
The group’s emphasis on operational efficiency and transparency is key to enticing new affiliates. It suggests that the group is aiming for sustainability by creating an environment that is conducive to building a bigger and stronger affiliate base.
Of note is that some enterprises complained about the decryption tool that Hive operators provided after settling the ransom. Reports said it lacked proper functionality and claimed that the Master Boot Records of their virtual machines were corrupted, rendering them incapable of booting.
Top affected countries and industries
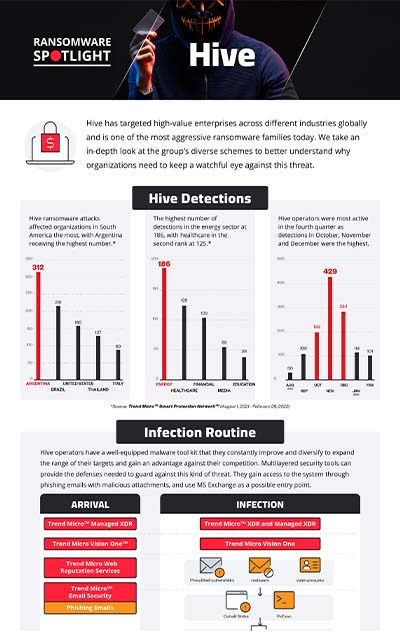
This section cites Trend Micro™ Smart Protection Network™ (SPN) data on Hive’s attempts to compromise organizations. Our detections show that Hive ransomware attack attempts against organizations were observed the most in South America, with Argentina receiving the highest number followed by Brazil. The United States takes the third spot, while the rest are spread across Europe, Asia, and the Middle East.
Figure 1. 10 countries with the highest number of attack attempts per machine for Hive ransomware (August 1, 2021 to February 28, 2022)
Source: Trend Micro Smart Protection Network
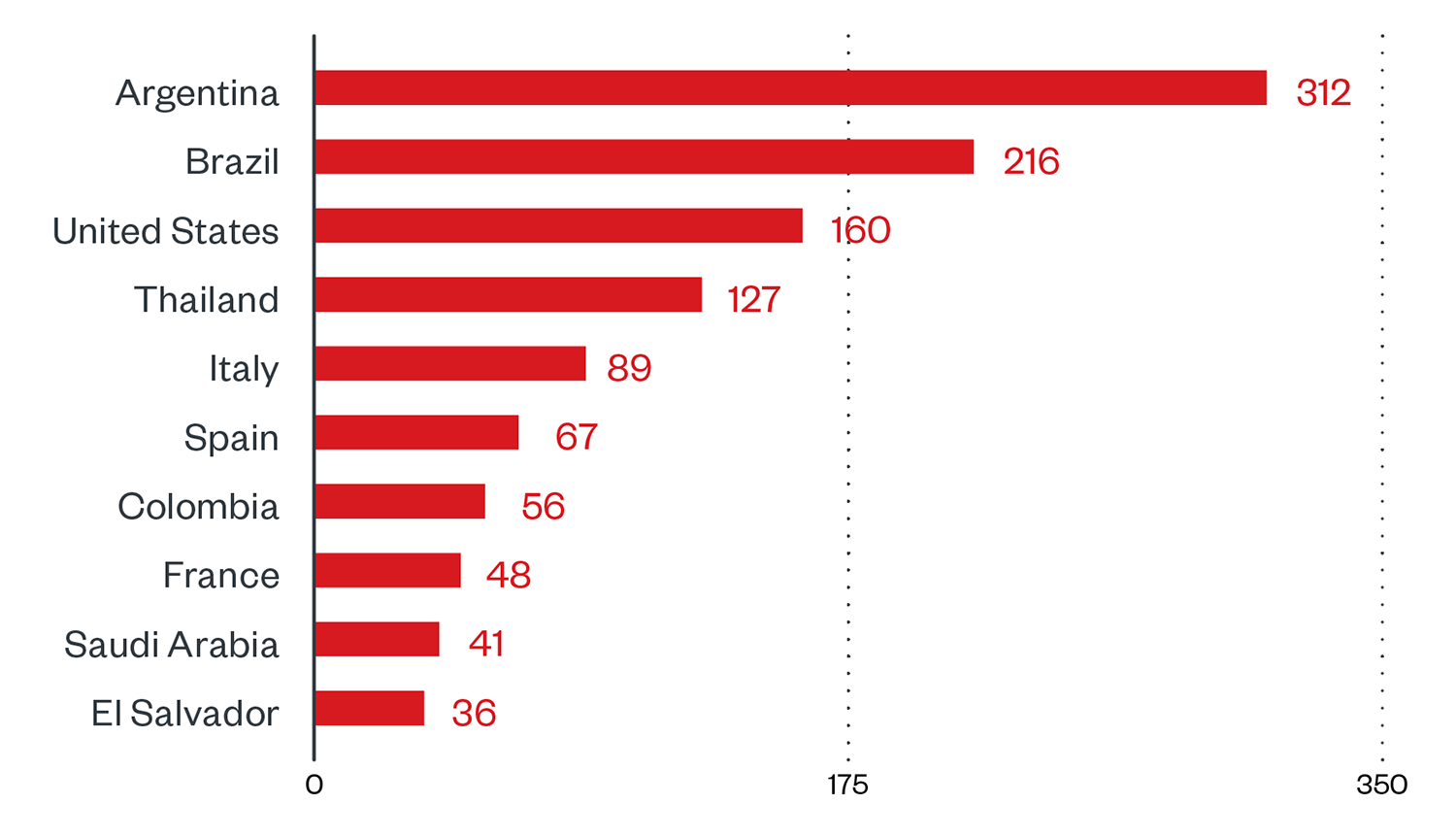
The energy sector had the highest number of attack attempts at 186; healthcare came in second at 125, followed by the financial sector with 102 detections.
Figure 2. 10 industries with the highest number of attack attempts per machine for Hive ransomware (August 1, 2021 to February 28, 2022)
Source: Trend Micro Smart Protection Network
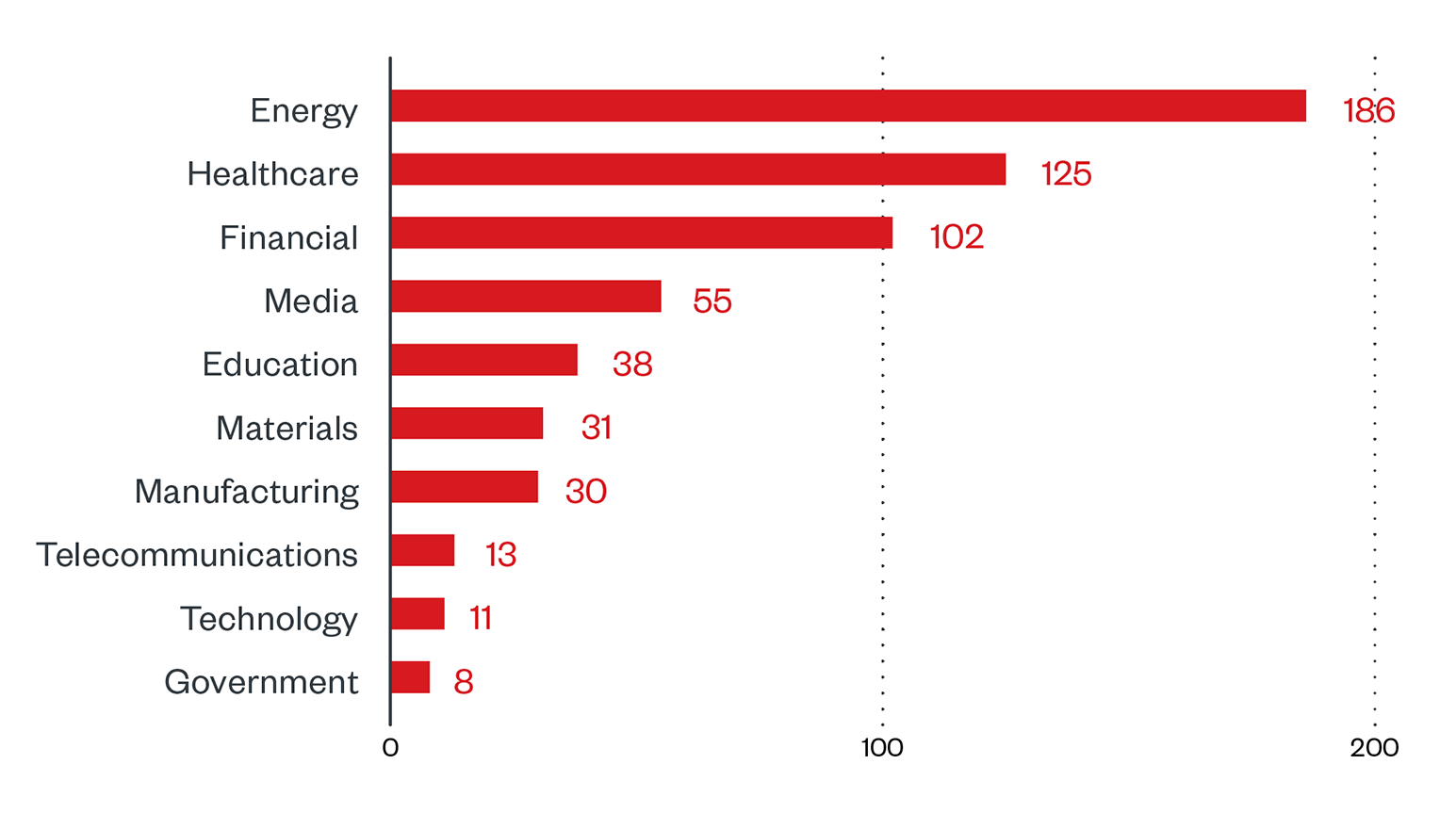
By breaking down the detections per month, our findings reveal that attack attempts peaked in November 2021 at 429. Hive operators were most active in the fourth quarter of 2021 as detections in December and October were the second and third highest numbers, respectively.
Figure 3. Monthly breakdown of detections per machine for Hive ransomware (August 1, 2021 to February 28, 2022)
Source: Trend Micro Smart Protection Network
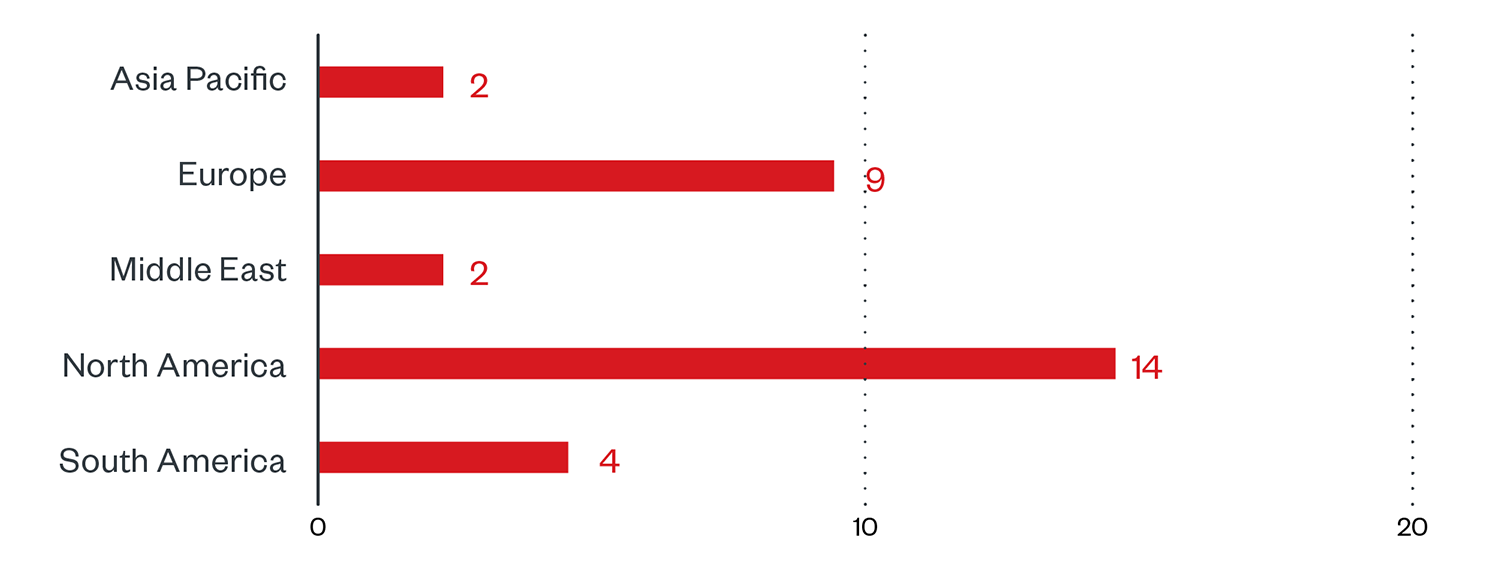
Targeted regions and sectors according to Hive’s leak site
An examination of the information that can be found on HiveLeaks reveals the number of successfully compromised companies that, as of this writing, have declined to pay the ransom. In our monitoring of their leak site from December 1, 2021 to February 28, 2022, attacks were highest in North America at 45.2% followed by Europe at 29% and Latin America at 12.9%.
Figure 4. Regional distribution of Hive victims according to the group’s leak site (December 1, 2021 to February 28, 2022)
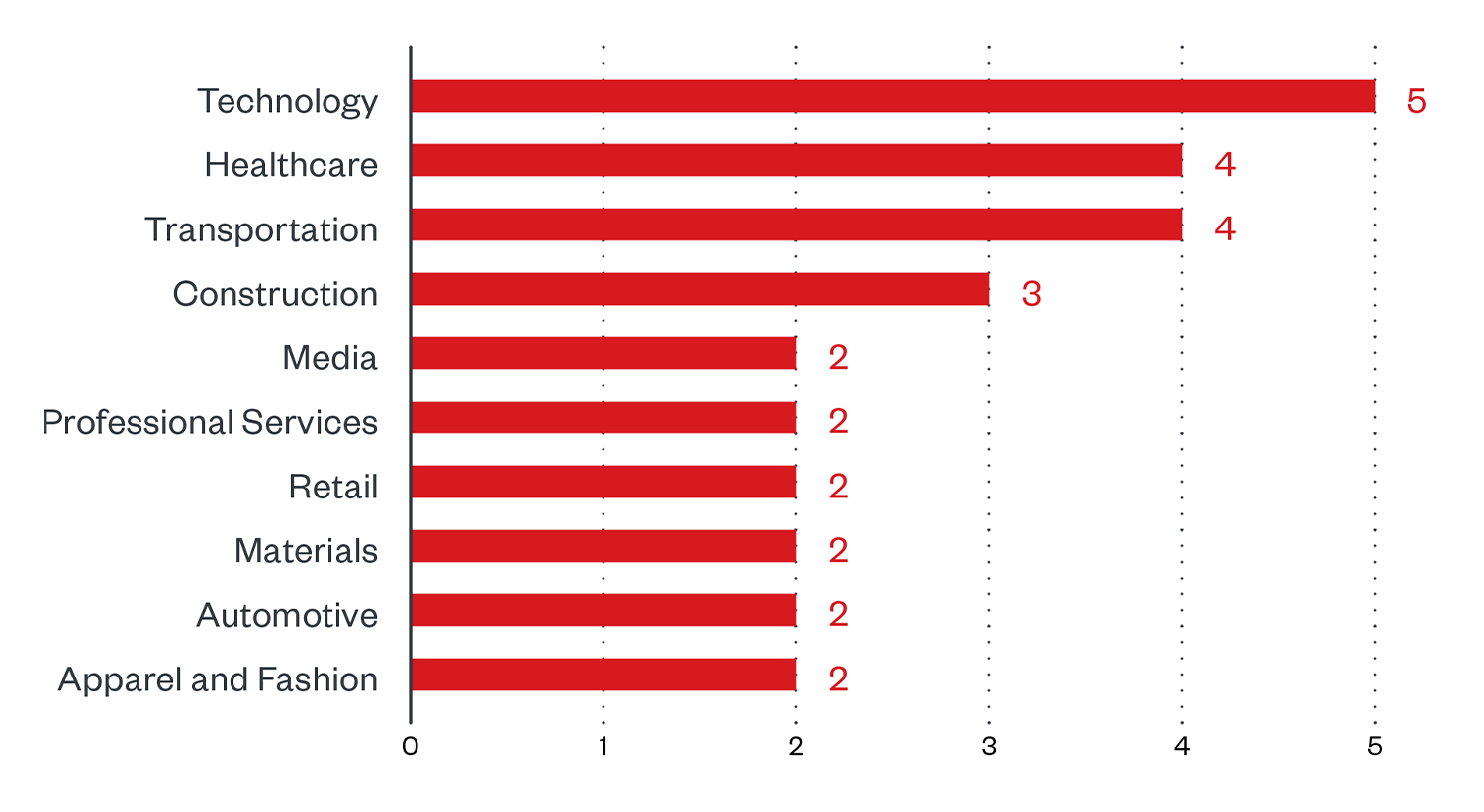
Enterprises appear to be Hive’s preferred targets estimated at almost 40%. Their victims were from a wide range of sectors, with technology at the top of the list having a victim count of 5. The healthcare and transportation sectors follow at 4 victims each. Other affected industries include construction, media and entertainment, professional services, retail, materials, automotive, apparel and fashion.
Figure 5. Sector distribution of Hive victims according to the group’s leak site (December 1, 2021 to February 28, 2022)
Data observed in the same time frame showed that most of the attacks took place on weekdays as malicious activities on weekends comprise only 6.5%.
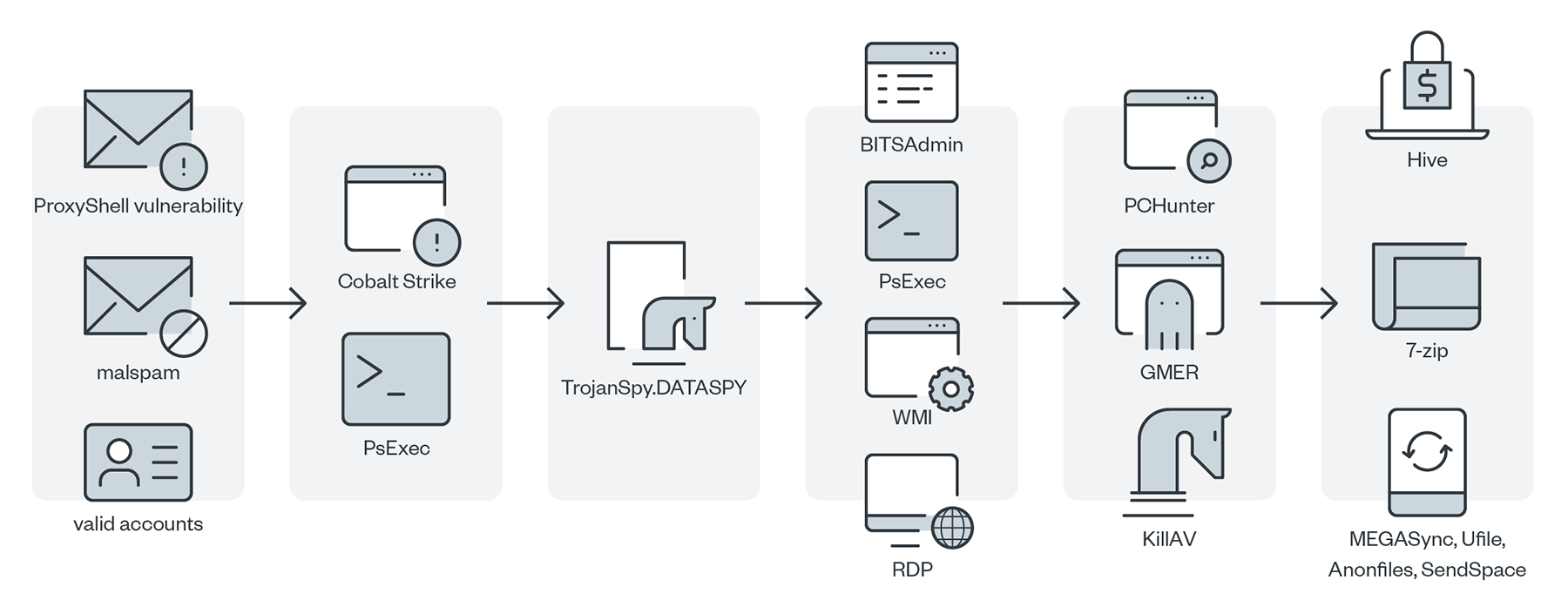
Initial Access
Hive operators breach systems through phishing emails with malicious attachments. We also observed Microsoft Exchange as a possible entry point for Hive ransomware based on our detection of the same post-exploitation scripts that can be found in the technique used to exploit ProxyShell-related vulnerabilities. These vulnerabilities were identified as CVE-2021-31207, CVE-2021-34473 and CVE-2021-34523.
Execution
Hive operators attempt to run the persistence technique for a Cobalt Strike beacon that can be used as a C&C method to accomplish lateral movement once they intrude into the system. Right after the attempt, Hive operators start to unload or uninstall antivirus (AV) products in the system so they can proceed to the download and execution of hacking tools such as PCHunter, GMER, and TrojanSpy.DATASPY. They use these tools to unload other AV products as a tactic to evade detection. We also observed the presence of WMI used to deploy uninstallation scripts and ransomware across the networks for lateral movement.
Defense Evasion, Discovery, and Credential Access
We observed the presence of PCHunter and GMER as their tools to discover and terminate services or processes to disable AV software. We also detected the use of TrojanSpy.DATASPY to gather information in the system such as machines in the network and the presence of specific AV products. In another attack, the threat actors deployed KillAV to terminate several AV products, also to avoid detection.
Lateral Movement, Command-and-Control
The Hive gang uses RDP and WMI to move laterally in the compromised network and deliver the payload remotely. We also detected the use of a BITSAdmin command for lateral movement. The threat actors also used PsExec to move laterally within the network.
Exfiltration
Our detections showed that the Hive operators use 7-Zip tool to archive stolen data for exfiltration. Moreover, the gang abuses anonymous file-sharing services such as MEGASync, AnonFiles, SendSpace, and uFile to exfiltrate data.
Impact
The ransomware payload proceeds with the encryption routine upon execution. The ransomware generates a random key that is used to encrypt based on RTLGenRandom API, which will be initially saved on the device’s memory. The key is then used in what appears to be a custom implementation of the encryption process.
The key also encrypts through RSA via GoLang’s implementation of RSA encryption. It accomplishes the RSA encryption through a list of public keys embedded in the binary. It is then saved as
The generated key will then be wiped from memory, leaving the encryption key as the only copy of the key for decryption.
MITRE tactics and techniques
| Initial Access | Execution | Persistence | Defense Evasion | Discovery | Lateral Movement | Collection | Command and Control | Exfiltration | Impact |
|---|---|---|---|---|---|---|---|---|---|
T1566.001 - Phishing: Spear-phishing attachment T1190 - Exploit public-facing application T1078 - Valid accounts | T1106 - Native API T1059.003 - Command and scripting interpreter: Windows Command Shell T1059.001 - Command and scripting interpreter: PowerShell T1053.005 - Scheduled Task/Job: Scheduled TaskRegisters and executes malicious tasks T1204 - User execution T1047 - Windows Management Instrument | T1053.005 - Boot or logon autostart execution T1068 - Exploitation for Privilege Escalation | T1562.001 - Impair Defenses: Disable or Modify Tools | T1083 - File and directory discovery T1018 - Remote system discovery T1057 - Process discovery T1063 - Security software discovery T1049 - System Network Connections Discovery T1135 - Network Share Discovery | T1570 - Lateral tool transfer T1021.002 - Remote services: SMB/Windows admin shares T1021.006 - Remote Services: Windows Remote Management Uses WMI to execute and deploy uninstallation scripts and the ransomware payload. | T1005 - Data from local system T1560.001 - Archive Collected Data: Archive via Utility | T1105 - Ingress Tool Transfer | T1567 - Exfiltration over web service | T1486 - Data encrypted for impact |
Summary of malware, tools, and exploits used
Security teams can watch out for the presence of the following malware tools and exploits that are typically used in Hive attacks:
| Initial Access | Execution | Discovery | Lateral Movement | Defense Evasion | Exfiltration |
|---|---|---|---|---|---|
Phishing emails with malicious attachments Exoitpls:
|
|
|
|
|
|
Recommendations
Despite being relatively new, Hive ransomware has already made its mark as one of the most prolific and aggressive ransomware families today. Our detections of their malicious activities show that their operations are robust, thus providing an incentive for new affiliates to join them. Hive operators are also known to constantly refine and diversify their TTPs, so it is important for companies to stay vigilant and be well-informed of potential threats. An organization stands a better chance of addressing ransomware threats if they implement strong defenses early on.
To protect systems against similar threats, organizations can establish security frameworks that allocate resources systematically for establishing a strong defense strategy against ransomware.
Here are some best practices that organizations can consider:
Audit and inventory
- Take an inventory of assets and data
- Identify authorized and unauthorized devices and software
- Audit event and incident logs
Configure and monitor
- Manage hardware and software configurations
- Grant admin privileges and access only when necessary to an employee’s role
- Monitor network ports, protocols, and services
- Activate security configurations on network infrastructure devices such as firewalls and routers
- Establish a software allowlist that only executes legitimate applications
Patch and update
- Conduct regular vulnerability assessments
- Perform patching or virtual patching for operating systems and applications
- Update software and applications to their latest versions
Protect and recover
- Implement data protection, backup, and recovery measures
- Enable multifactor authentication (MFA)
Secure and defend
- Employ sandbox analysis to block malicious emails
- Deploy the latest versions of security solutions to all layers of the system, including email, endpoint, web, and network
- Detect early signs of an attack such as the presence of suspicious tools in the system
- Use advanced detection technologies such as those powered by AI and machine learning
Train and test
- Regularly train and assess employees on security skills.
- Conduct red-team exercises and penetration tests.
A multilayered approach can help organizations guard possible entry points into their system (endpoint, email, web, and network). Security solutions can detect malicious components and suspicious behavior, which can help protect enterprises.
- Trend Micro Vision One™ provides multilayered protection and behavior detection, which helps block questionable behavior and tools before the ransomware can do any damage.
- Trend Micro Cloud One™ Workload Security protects systems against both known and unknown threats that exploit vulnerabilities. This protection is made possible through techniques such as virtual patching and machine learning.
- Trend Micro™ Deep Discovery™ Email Inspector employs custom sandboxing and advanced analysis techniques to effectively block malicious emails, including phishing emails that can serve as entry points for ransomware.
- Trend Micro Apex One™ offers next-level automated threat detection and response against advanced concerns such as fileless threats and ransomware, ensuring the protection of endpoints.
Indicators of Compromise (IOCs)
The IOCs for this article can be found here. Actual indicators might vary per attack.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Ransomware Spotlight: Agenda
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™
- Forecasting Future Outbreaks: A Behavioral and Predictive Approach to Proactive Cyber Risk Management
- Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report


 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One